Classification method applicable for intrusion detection
A technology of intrusion detection and classification methods, applied in the field of network security, can solve the problems of high misjudgment rate and low detection rate, and achieve the effect of improving the unsatisfactory recognition effect
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
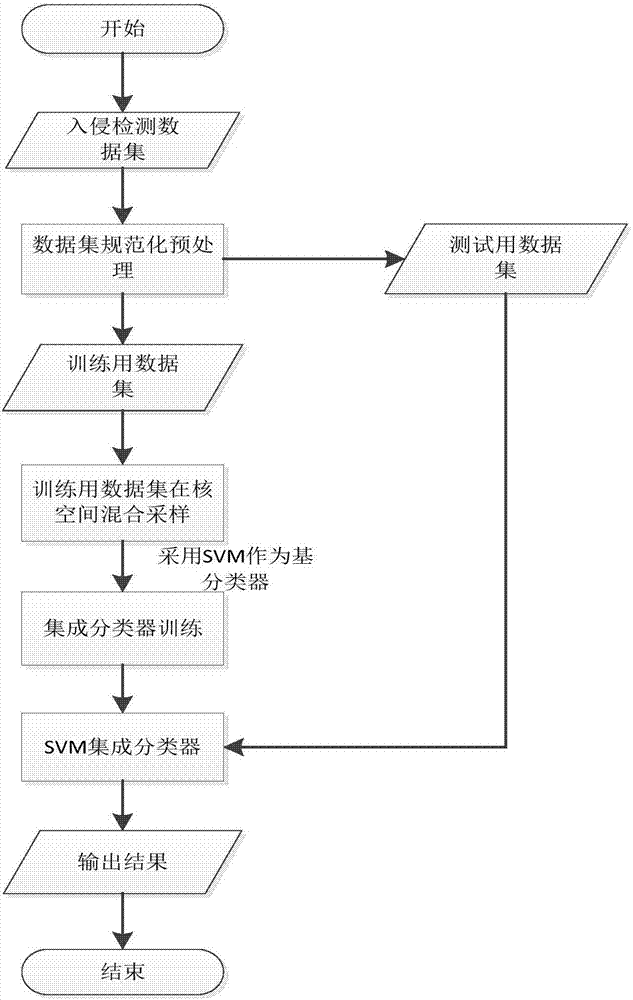
[0014] The implementation process of the present invention will be described in detail below in conjunction with the accompanying drawings, as figure 1 As shown, the workflow of the inventive method is mainly divided into 4 parts:
[0015] 1) Data preprocessing: Normalize the sample feature parameters for the intrusion detection standard data set KDD CUP99, realize the numerical conversion of all text attribute information, and normalize all feature attributes, and unify the measurement of attributes.
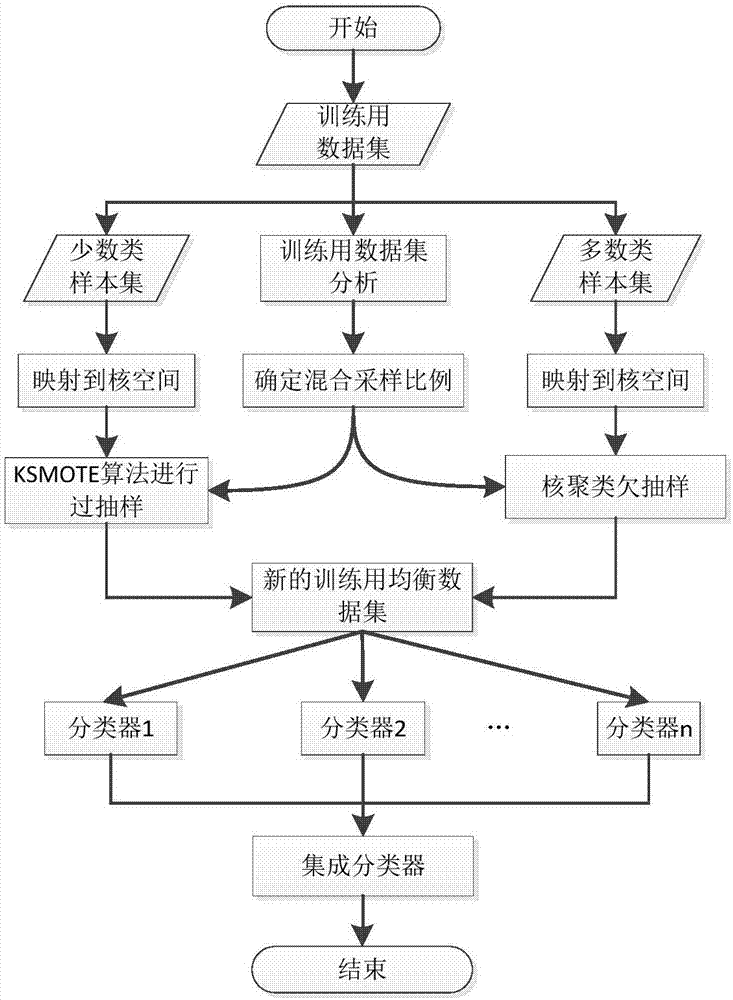
[0016] 2) For the unbalanced training data set, mix sampling in the kernel space to improve the category balance. The following is the generation process of the mixed sampling new sample set, such as figure 2 As shown in the description, it is divided into two parts:
[0017] Step 2.1: Perform SMOTE oversampling on the minority class samples in the kernel space.
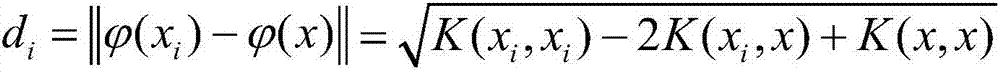
[0018] Suppose the minority class sample set to be processed is: F={x 1 ,x 2 ,...x n},x i ∈R h , i=1,2,···,...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com