A two-key symmetric encryption method based on nanomaterials with composite signals and binary
An encryption method and nanomaterial technology, applied in the field of information encryption and storage, can solve problems such as the inability to understand the content of information, and achieve the effect of being conducive to confidentiality and simple materials
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
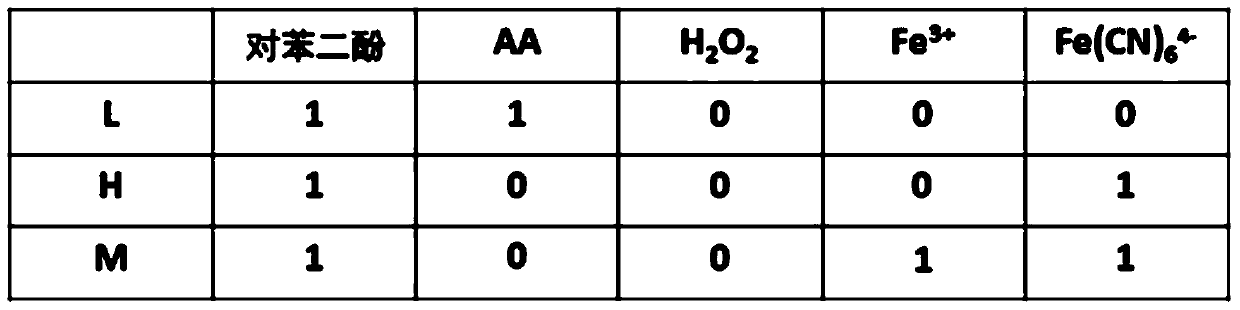
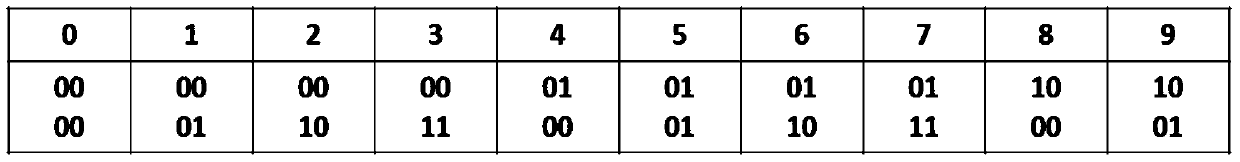
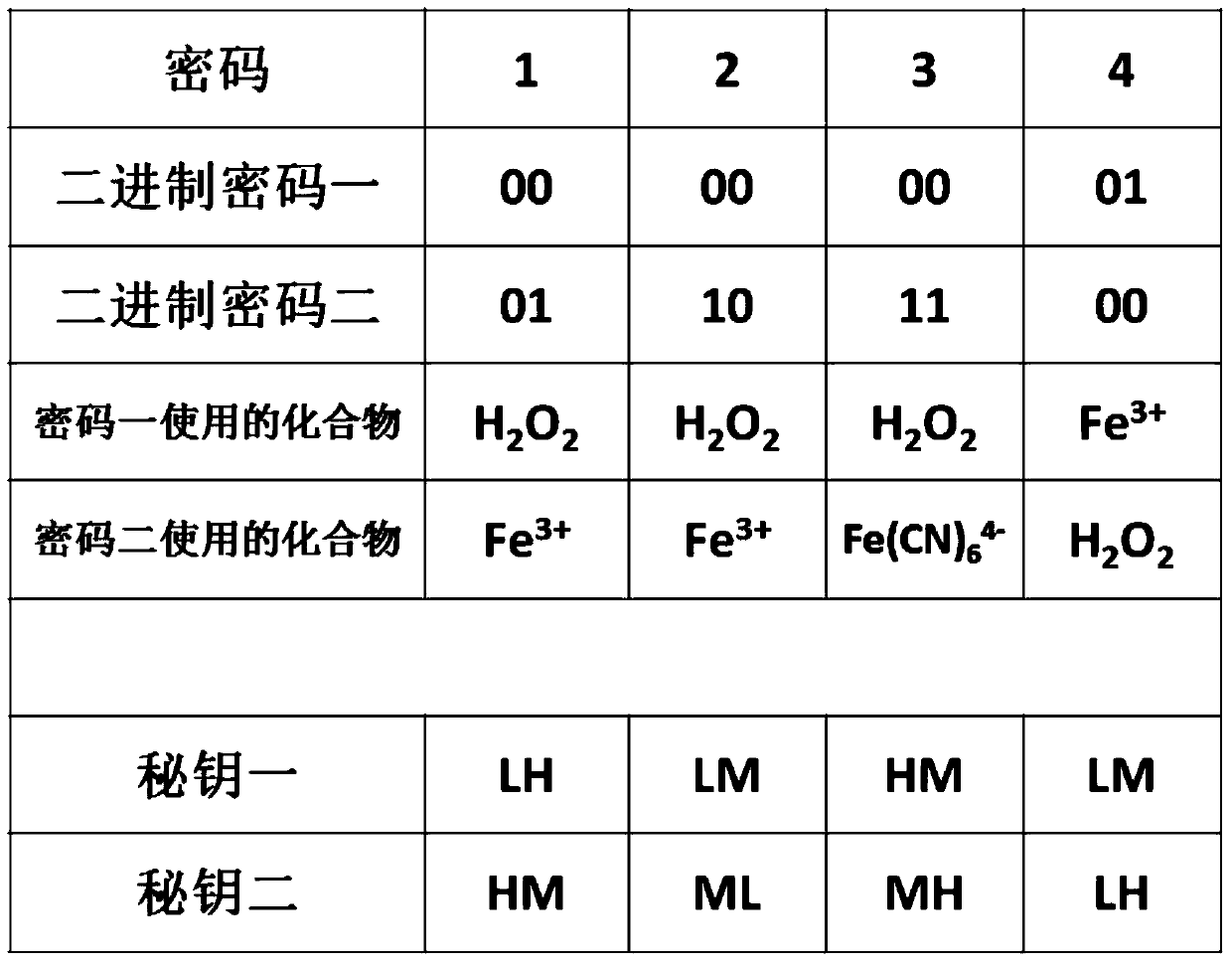
[0061] Embodiment 1, based on nanomaterials with composite signals and a binary novel double-key encryption method:
[0062] 1. Encryption part: first list the digital information segment to be encrypted as 1234, press the digital information segment 1234 figure 2 Converted to two sets of binary numbers, such as image 3 As shown, they are binary password 1: 00 00 00 01, binary password 2: 01 1011 00, and then according to figure 1 Convert binary code 1 and binary code 2 into corresponding colorless compound solutions, that is, the compounds used in binary code 1 and the corresponding secret keys are as follows: image 3 As shown, the compound used in the binary code 2 and the corresponding secret key 2 are as image 3 As shown, the digital information segment that needs to be encrypted is 1234 encrypted.
[0063] 2. Cracking part: Fe with a molar concentration of 1mM 3+ Modified 40% Gd NaLuF 4 : The aqueous solution of Yb, Er, Gd nanoparticles and the hydrogen peroxide (H...
Embodiment 2
[0064] Embodiment 2, based on nanomaterials with composite signals and a binary novel double-key encryption method:
[0065] 1. Encryption part: first list the letter information segment that needs to be encrypted as ZHOU, then set the letter information segment as ZHOU and press Figure 8 Converted to two sets of binary numbers, such as Figure 9 As shown, they are binary code 1 and binary code 2 respectively, and then according to figure 1 Convert binary code 1 and binary code 2 into corresponding colorless compound solutions, that is, the compounds used in binary code 1 and the corresponding secret keys are as follows: Figure 9 As shown, the compound used in the binary code 2 and the corresponding secret key 2 are as Figure 9 As shown, that is, the letter information segment that needs to be encrypted is encrypted for ZHOU.
[0066] 2. Cracking part: the molar concentration of 1mM Ni 3+ Modified NaGdF containing 80% Gd 4 : The aqueous solution of Yb, Er, Tm and the a...
PUM
| Property | Measurement | Unit |
|---|---|---|
| thickness | aaaaa | aaaaa |
| diameter | aaaaa | aaaaa |
Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com