A payment method and device
A payment device and payment card technology, applied in the financial field, can solve the problems of easy interception and tampering, poor security in the payment process, etc., and achieve the effect of preventing interception and tampering and improving security.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
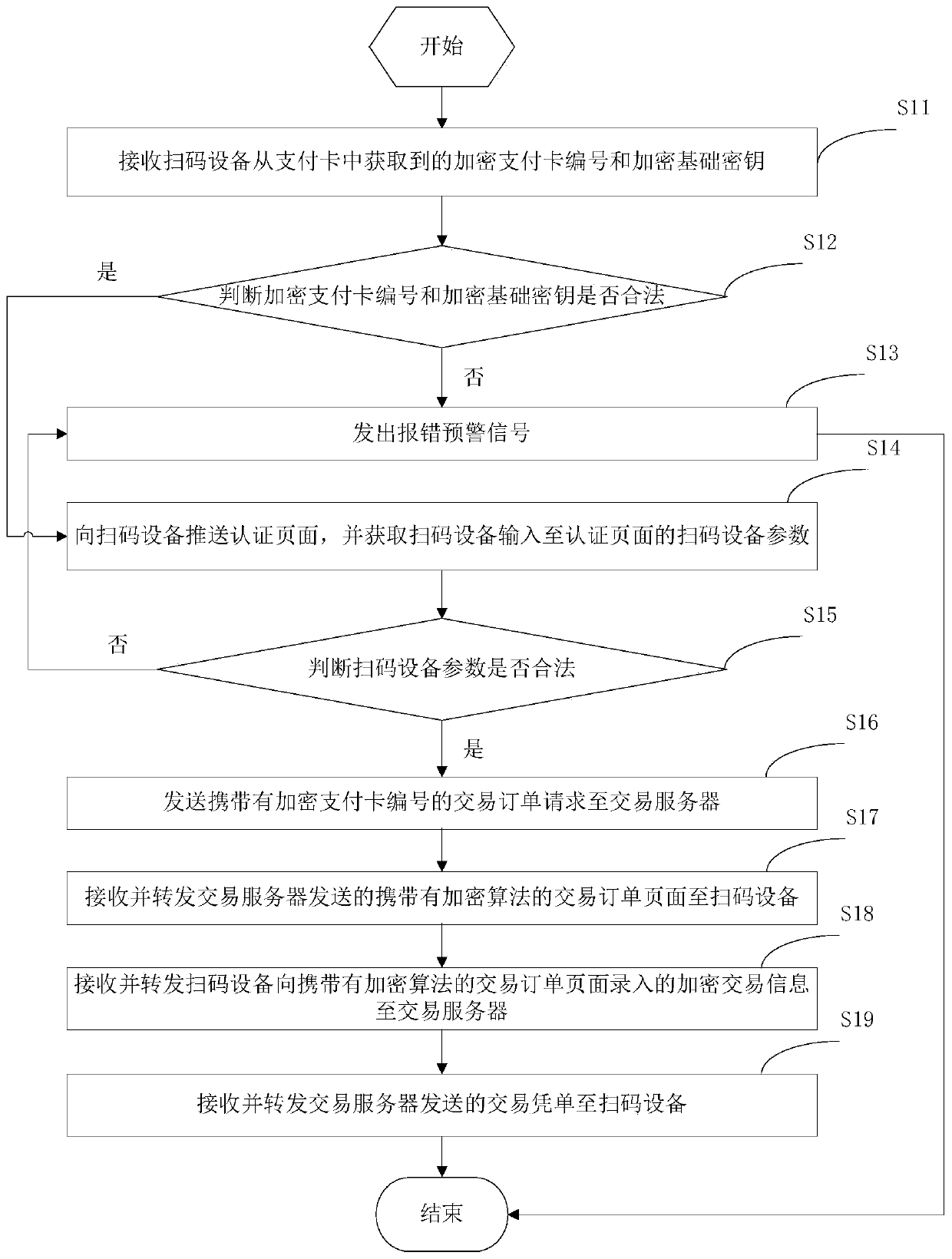
[0074] In this embodiment, a payment method is provided, which is applied to the website server, please refer to figure 1 , which shows a flow chart of the payment method provided by this application, which may include the following steps:
[0075] Step S11: Receive the encrypted payment card number and encrypted basic key obtained from the payment card by the code scanning device.
[0076] The encrypted payment card number is generated by encrypting the payment card number by the transaction server, and the encrypted basic key is generated by encrypting the basic key by the transaction server.
[0077] Wherein, multiple different payment card information mapping relationships are stored in the database of the transaction server, and each payment card information mapping relationship is a mapping relationship between a payment card number and a basic key.
[0078] In this embodiment, the encrypted payment card number and the encrypted basic key are pre-written into the paymen...
Embodiment 2
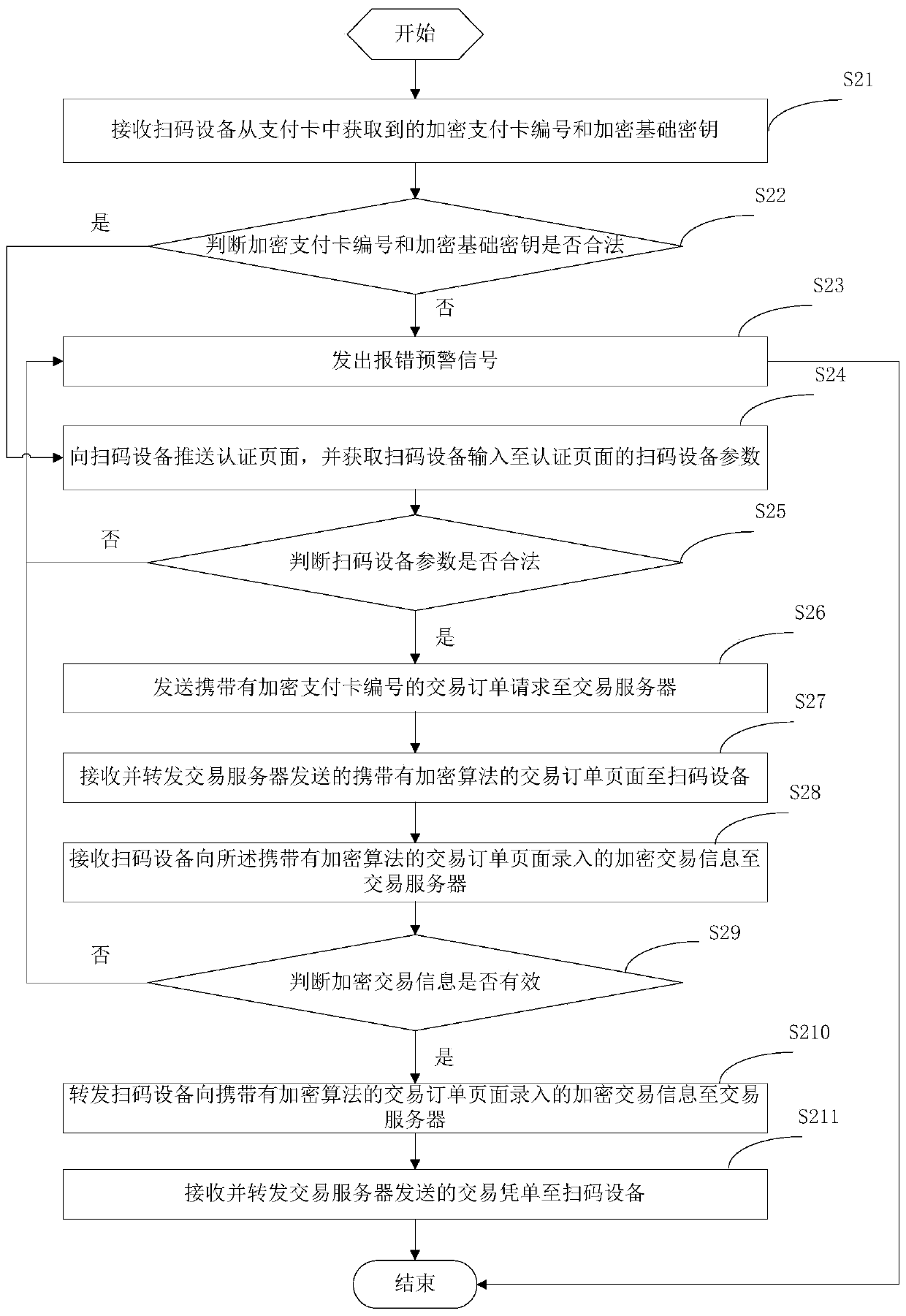
[0118] In this example, in figure 1 Based on the payment method shown, another payment method is extended, please refer to figure 2 , can include the following steps:
[0119] Step S21: Receive the encrypted payment card number and encrypted basic key obtained from the payment card by the code scanning device.
[0120] The encrypted payment card number is generated by encrypting the payment card number by the transaction server, and the encrypted basic key is generated by encrypting the basic key by the transaction server.
[0121] Step S22: judging whether the encrypted payment card number and the encrypted basic key are legal.
[0122] If not, execute step S23, and if yes, execute step S24.
[0123] Step S23: sending out an error warning signal.
[0124] Step S24: Pushing an authentication page to the code scanning device, and acquiring parameters of the code scanning device input to the authentication page by the code scanning device.
[0125] Step S25: Judging whethe...
Embodiment 3
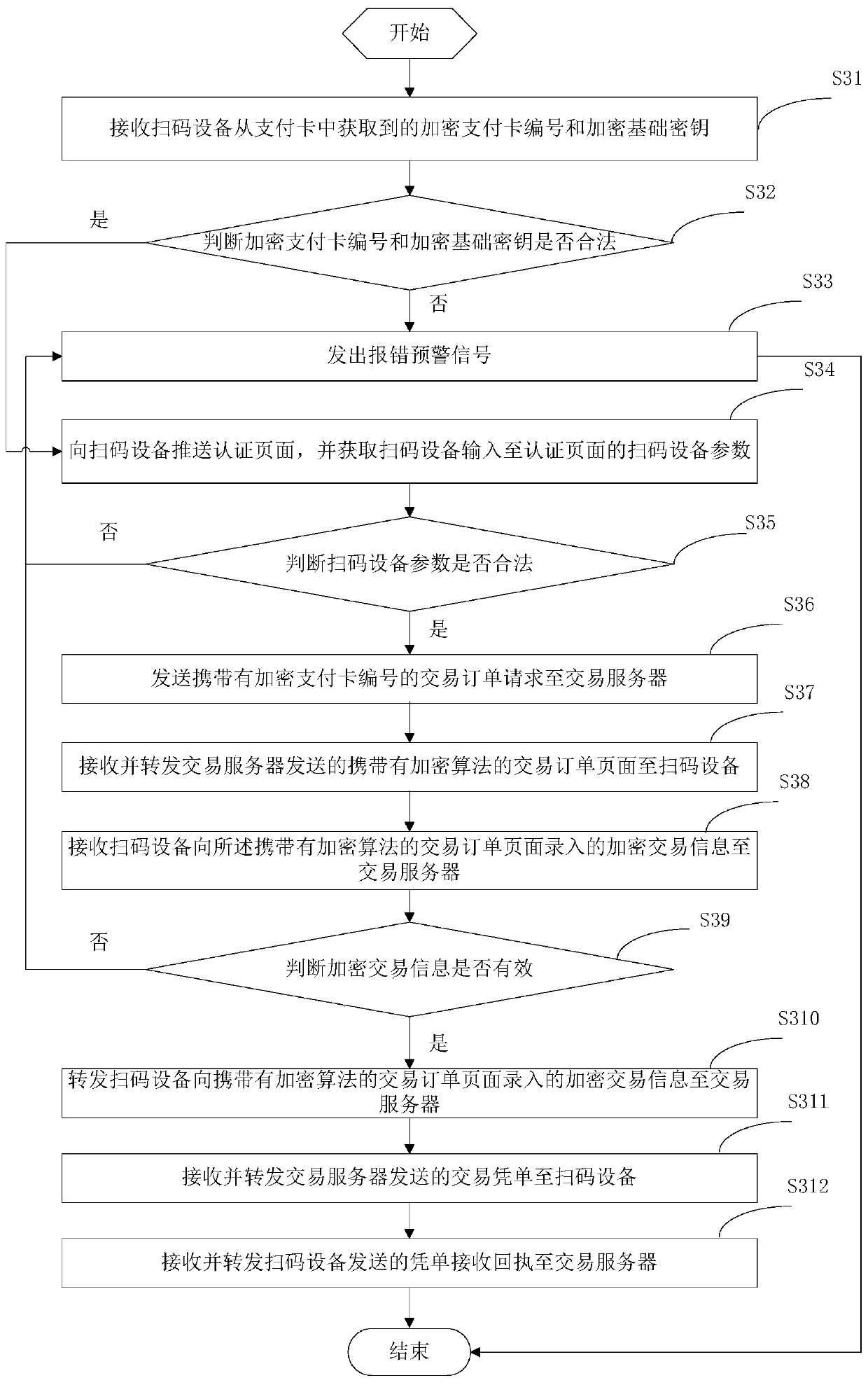
[0140] In this example, in figure 2 Based on the payment method shown, another payment method is extended, please refer to image 3 , can include the following steps:
[0141] Step S31: Receive the encrypted payment card number and encrypted basic key obtained from the payment card by the code scanning device.
[0142] The encrypted payment card number is generated by encrypting the payment card number by the transaction server, and the encrypted basic key is generated by encrypting the basic key by the transaction server.
[0143] Step S32: judging whether the encrypted payment card number and the encrypted basic key are legal.
[0144] If not, execute step S33, and if yes, execute step S34.
[0145] Step S33: sending out an error warning signal.
[0146] Step S34: Pushing an authentication page to the code scanning device, and acquiring parameters of the code scanning device input to the authentication page by the code scanning device.
[0147] Step S35: Judging whethe...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com