Filtering position selection method against bandwidth consumption-type attacks
A technology for filtering location and bandwidth consumption, applied in electrical components, transmission systems, etc., can solve problems such as large economic losses and network performance impact, and achieve the effects of improving efficiency, minimizing bandwidth resources, and reducing complexity
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
experiment example
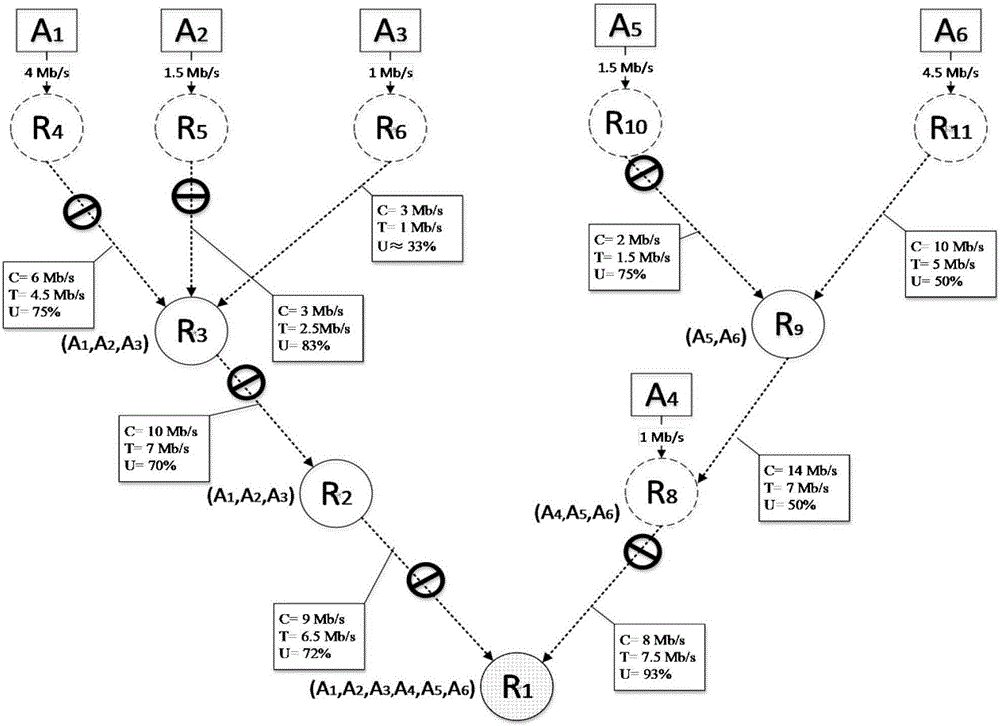
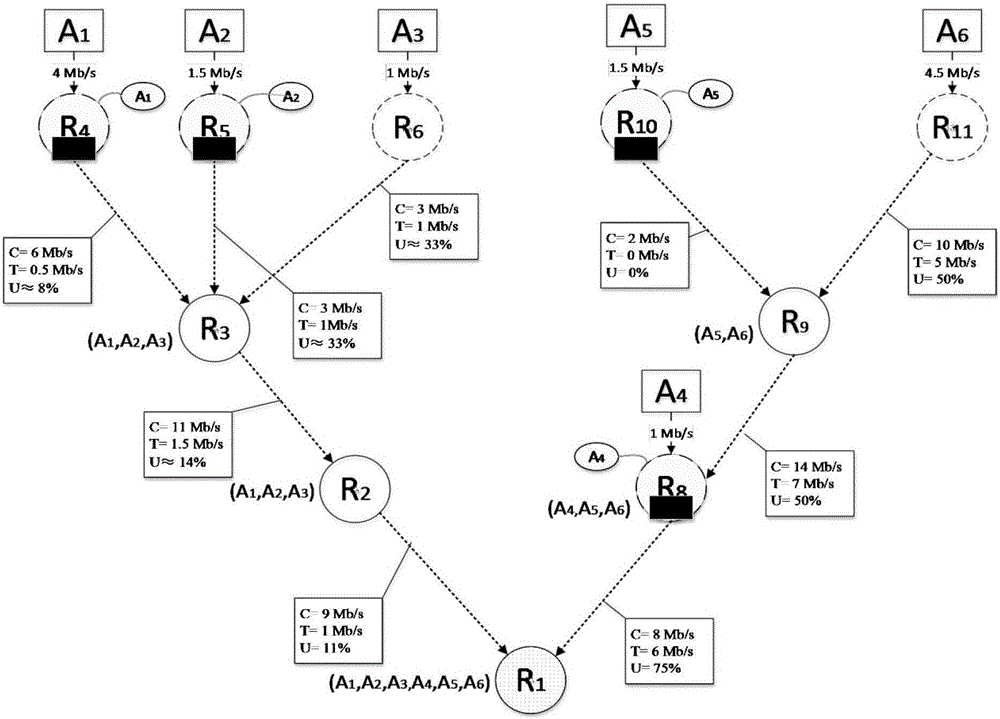
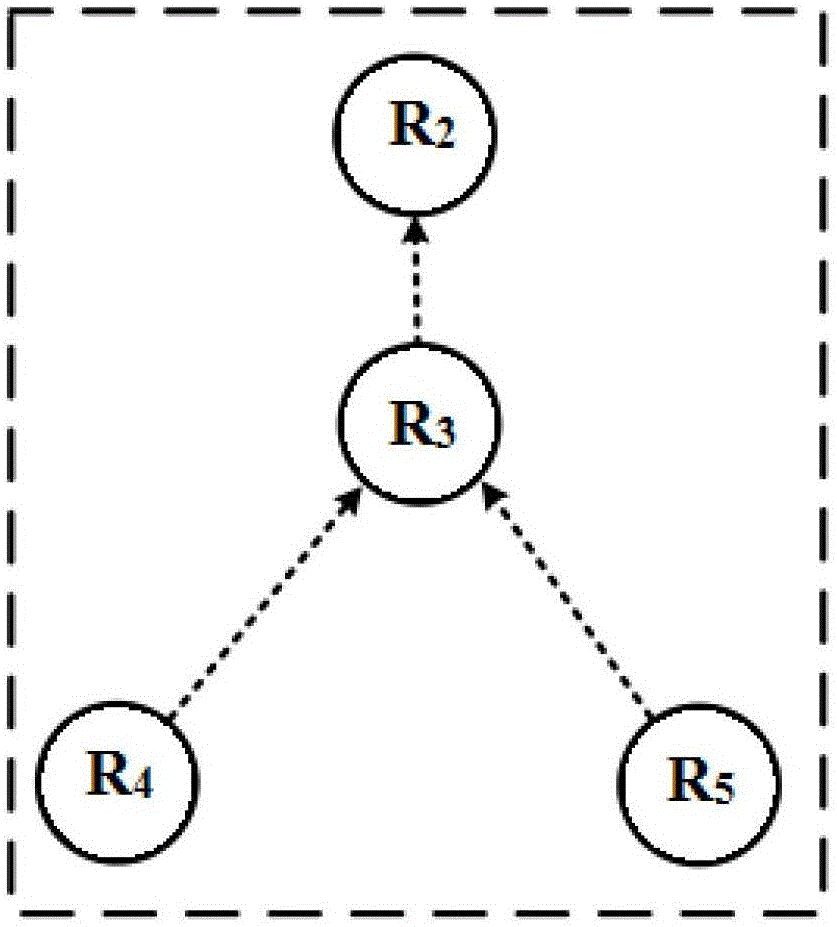
[0077] Experimental example: figure 1 is the given attack network (which can be constructed using the traceability method), figure 2 is the corresponding defense model. After in-depth analysis of the attack behavior, the bandwidth-exhausted attack network can be defined as a multi-source single-sink graph, denoted as G S ={V S ,L S ,S S ,D S ,R S ,F S ,C S ,T S}, where, G S means attacking the network, V S Indicates attacking network G S The set of nodes in , L s Indicates attacking network G S The set of links in , S s Indicates attacking network G S The set of attack sources in , D s Indicates attacking network G S The root node in R S Indicates attacking network G S The set of attack flow rates in , F S Represents the set of relationships between nodes and attack paths in the attack network, C S Indicates attacking network G S Bandwidth usage of the medium link, T s Indicates the actual traffic set for each link.
[0078] Among them, the set of nod...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D Engineer
- R&D Manager
- IP Professional
- Industry Leading Data Capabilities
- Powerful AI technology
- Patent DNA Extraction
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2024 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com