A Distributed Encryption Storage and Authentication Method Based on Local Area Network
An encrypted storage and distributed technology, applied in the field of information security, can solve problems such as adverse user privacy, economic loss, user information leakage, etc., to achieve the effect of taking into account security and timeliness, not easy to decipher, and avoid information leakage
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0029] In order to make the object, technical solution and advantages of the present invention more clear, the present invention will be further described in detail below in conjunction with the examples. It should be understood that the specific embodiments described here are only used to explain the present invention, not to limit the present invention.
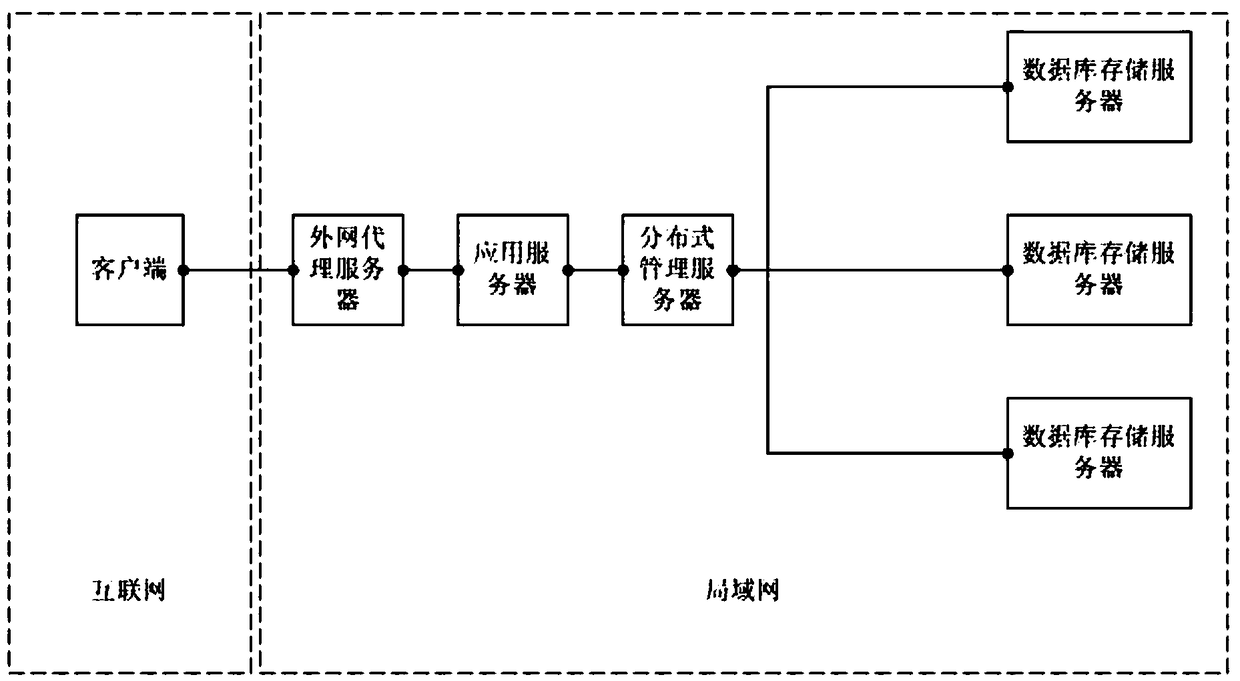
[0030] Encryption and authentication method of the present invention is mainly realized based on local area network, as figure 1 As shown, the client is in the general environment of the Internet, and is connected to the proxy server of the external network by signal, and the proxy server of the external network is connected to the application server by signal, so as to realize the transmission of information from the Internet to the LAN, and the application server transmits the information to the distributed management server , after being processed by the distributed management server (segmentation and weighting), and the...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D Engineer
- R&D Manager
- IP Professional
- Industry Leading Data Capabilities
- Powerful AI technology
- Patent DNA Extraction
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2024 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com