Reverse-based intrusion detection system and reverse-based intrusion detection method
An intrusion detection system and intrusion detection technology, applied in transmission systems, electrical components, etc., can solve the problems of stealing users, increasing the difficulty of review and certification, and achieve the effect of reducing overhead and simple detection rules
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0046] Below in conjunction with accompanying drawing and embodiment describe in detail:
[0047] 1. System
[0048] 1. Overall
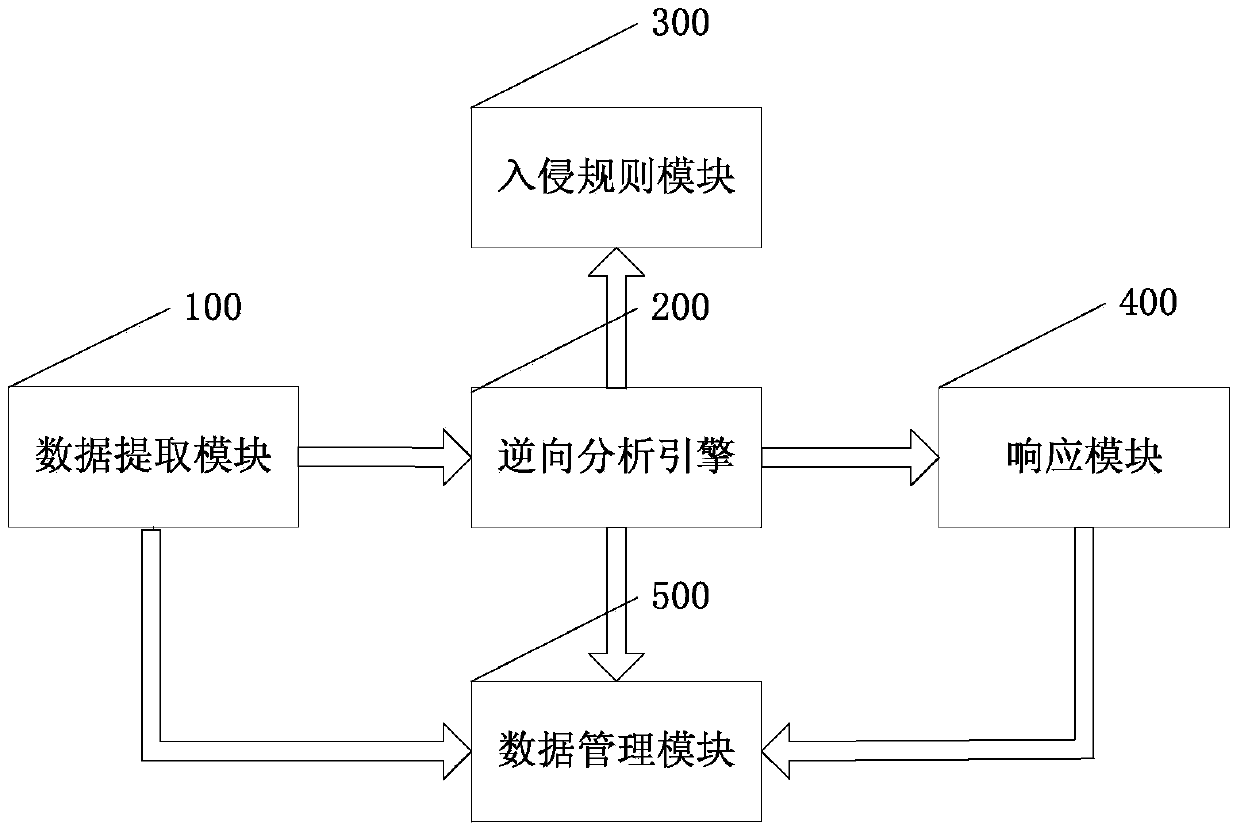
[0049] Such as figure 1 , the system includes a data extraction module 100, a reverse analysis module 200, an intrusion rule module 300, a response module 400 and a data management module 500;
[0050] Its interaction relationship is:
[0051] The data extraction module 100, the reverse analysis module 200 and the response module 400 interact in turn to realize the extraction of network data packets, reverse analysis and response to intrusion behavior;
[0052] The reverse analysis module 200 interacts with the intrusion rule module 300 and the data management module 500 respectively to realize the accumulation and storage of intrusion behavior rules;
[0053] The data extraction module 100 and the response module 400 respectively interact with the data management module 500 to realize the generation of system logs and network logs, thereby iden...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com