A User Identity Authentication System
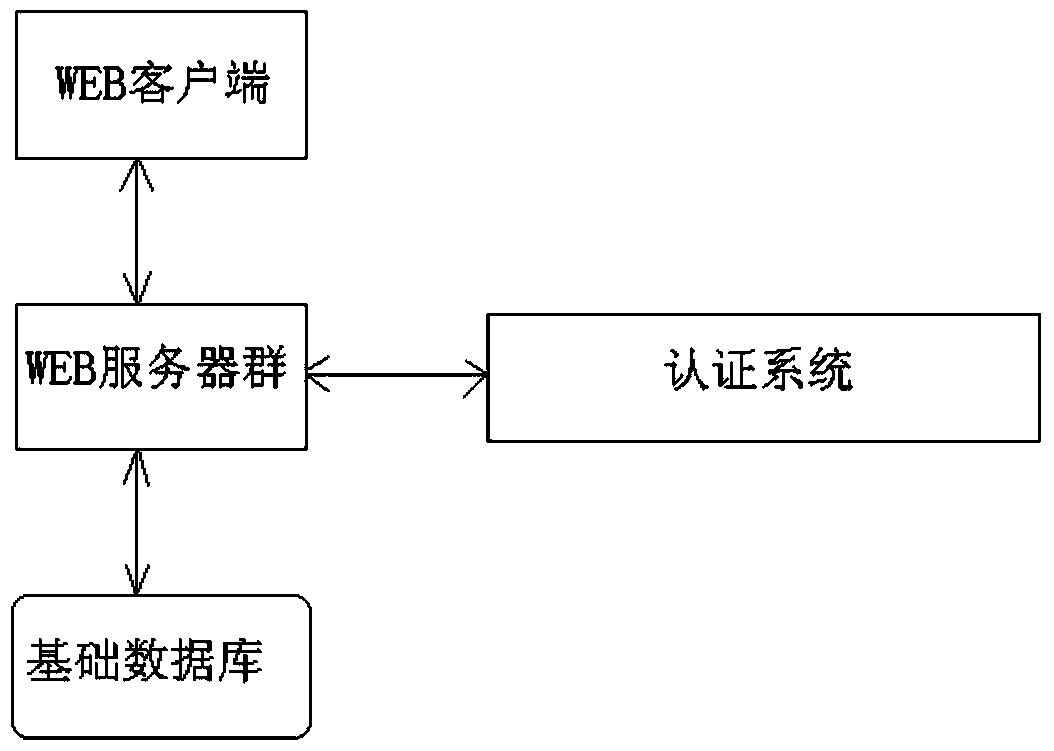
A technology for user identity authentication and identity authentication, applied in transmission systems, electrical components, etc., can solve problems such as high error rate, illegal activities, and low efficiency
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
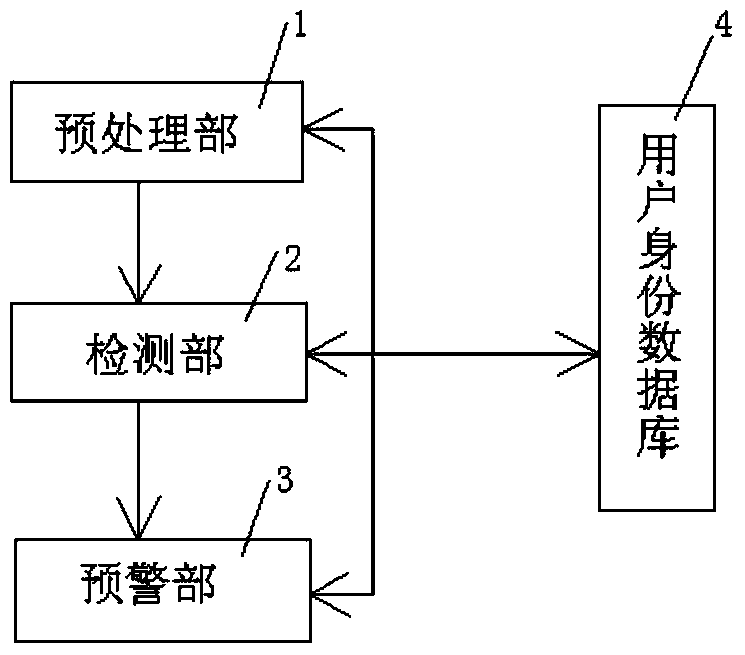
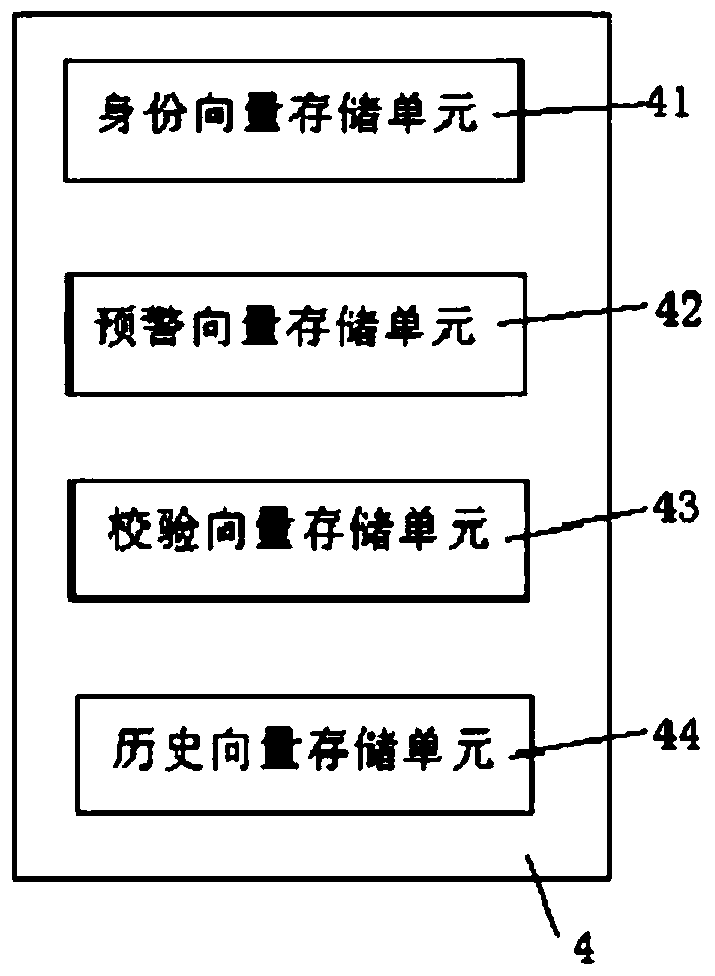
[0013] The user login authentication system and method include a preprocessing unit 1, a detection unit 2, an early warning unit 3, and a user identity database 4.
[0014] The preprocessing unit 1 includes a processing unit and an encryption unit.
[0015] After the user initiates a login request through HTTP, the processing unit collects the user's UDI information (UserDetail Information). The UDI information includes user login network environment data (UDIinternet) and social_network data (UDI_social). The network environment data includes data information such as IP address, operating system, and browser. Social network data includes account information of social networking sites, such as Weibo, WeChat, Facebook, school intranet, and various blog information.
[0016] The encryption unit encrypts the UDI information, and can use DEA (Data Encryption Algorithm) to encrypt the UDI information into a structured vector SUDI, and store the vector SUDI in the identity vector storage...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - Generate Ideas
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com