Certificateless signature algorithm for user identity authentication in network environment
A technology for user identity authentication and network environment, applied in the field of certificateless signature, it can solve the problem of low execution efficiency of secure certificateless signature algorithm, and achieve the effect of easy implementation, high execution efficiency and high security.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment
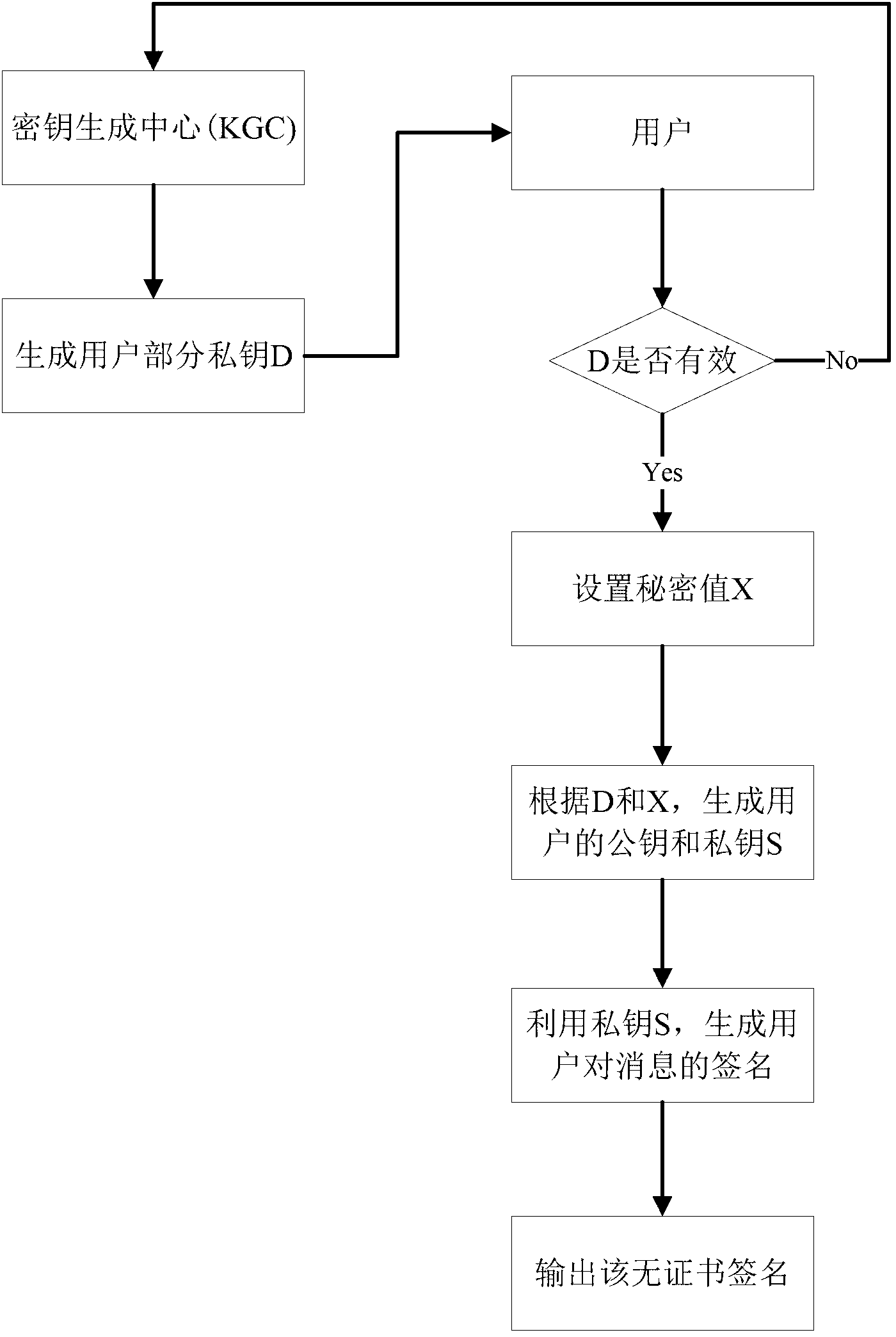
[0025] In this embodiment, the non-certificate signature method is performed according to the following steps:
[0026] (1) Assume two cyclic groups G of order q 1 and G 2 , a bilinear pair e:G 1 ×G 1 →G 2 and the master key of the Key Generation Center (KGC) and two secure hash functions Let P be G 1 generator, Q=sP is the public key of KGC, g=e(P, p), then the key generation center (KGC) public parameter PP=(e, H 1 ,H 2 , Q, g); In this embodiment, the P-192 elliptic curve recommended by the National Institute of Standards and Technology is selected, and the corresponding bilinear pair e and generator P are determined by it. Hash function H 1 ,H 2 Select SHA-2, master key s select A random number in .
[0027] (2) The user enters the master key and the user's identity ID ∈ {0,1} * , KGC randomly selects and calculate R ID = r ID P and z ID = r ID +H 1 (ID, R ID )smod; finally, KGC will (R ID ,z ID ) is sent to the user whose identity is ID; ID∈{0,...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com