Document monitor and management system based on comprehensive safety audit
A technology of monitoring management and security management, applied in transmission systems, computer security devices, computing, etc., can solve problems such as single inspection means, reduced user experience, and no monitoring
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0046] In order to make the above objects, features and advantages of the present invention more comprehensible, the present invention will be further described in detail below in conjunction with the accompanying drawings and specific embodiments.
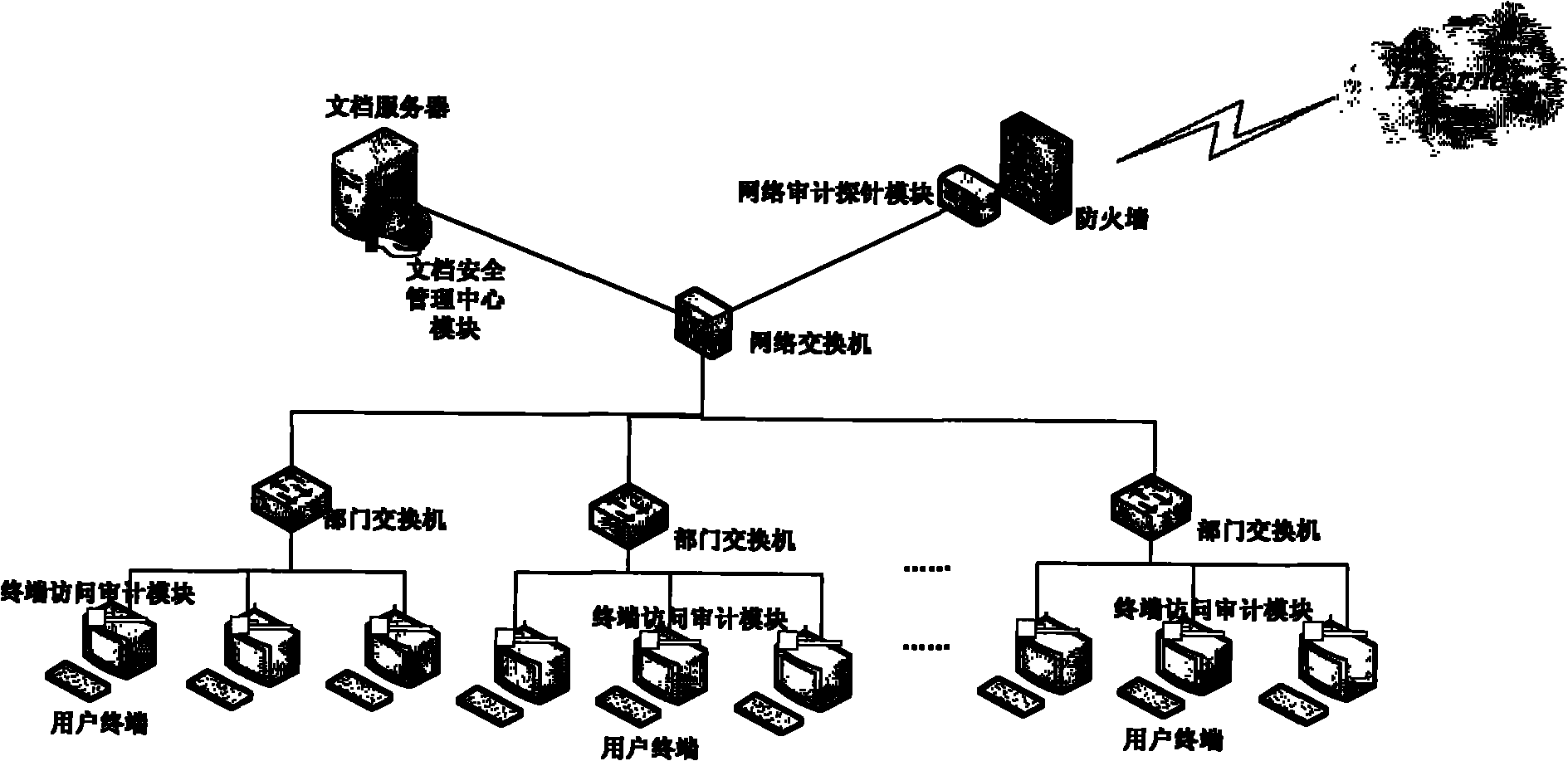
[0047] Referring to FIG. 1 , FIG. 1 is a schematic diagram of the network structure of an embodiment of the comprehensive security audit-based document monitoring and management system of the present invention.
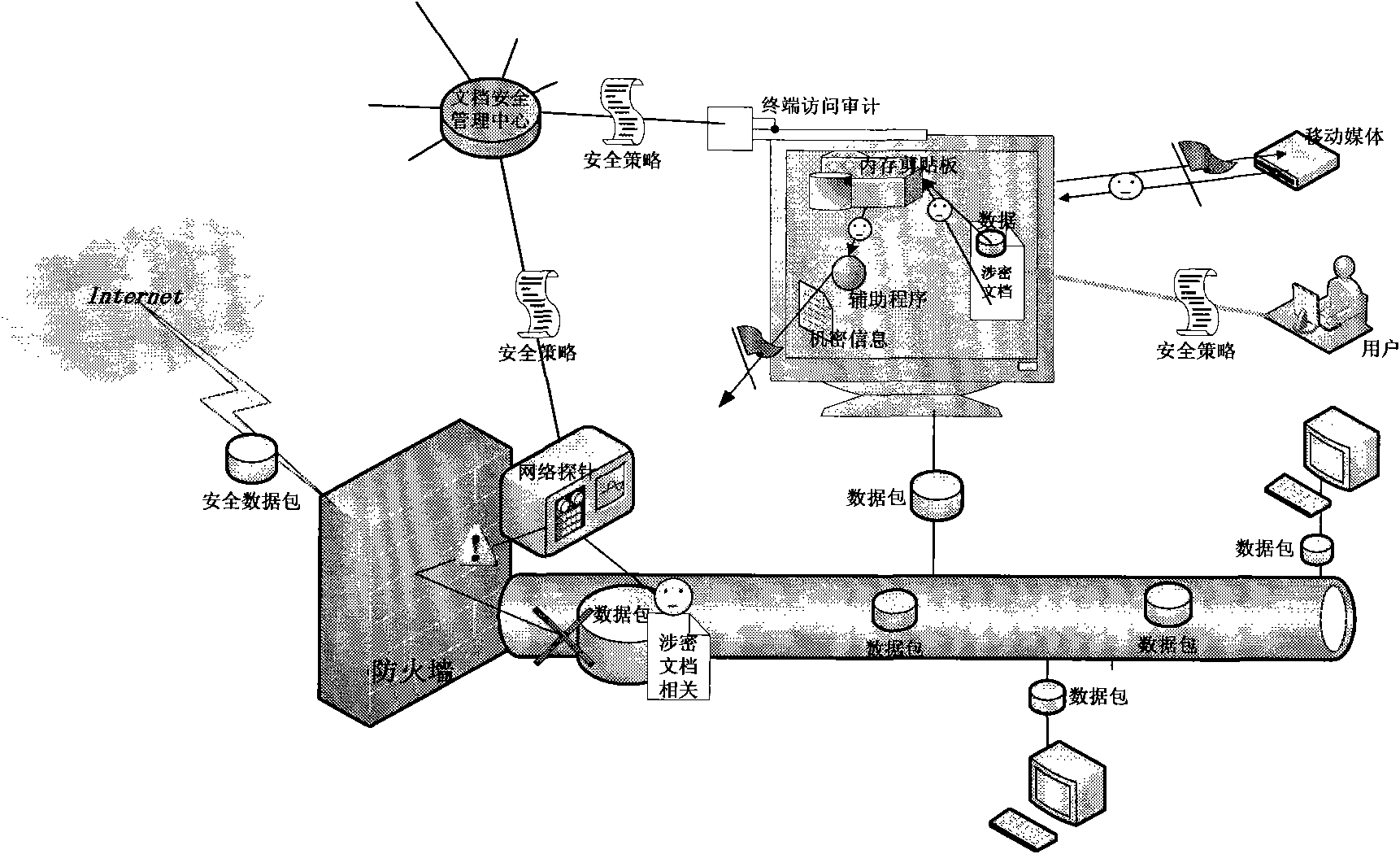
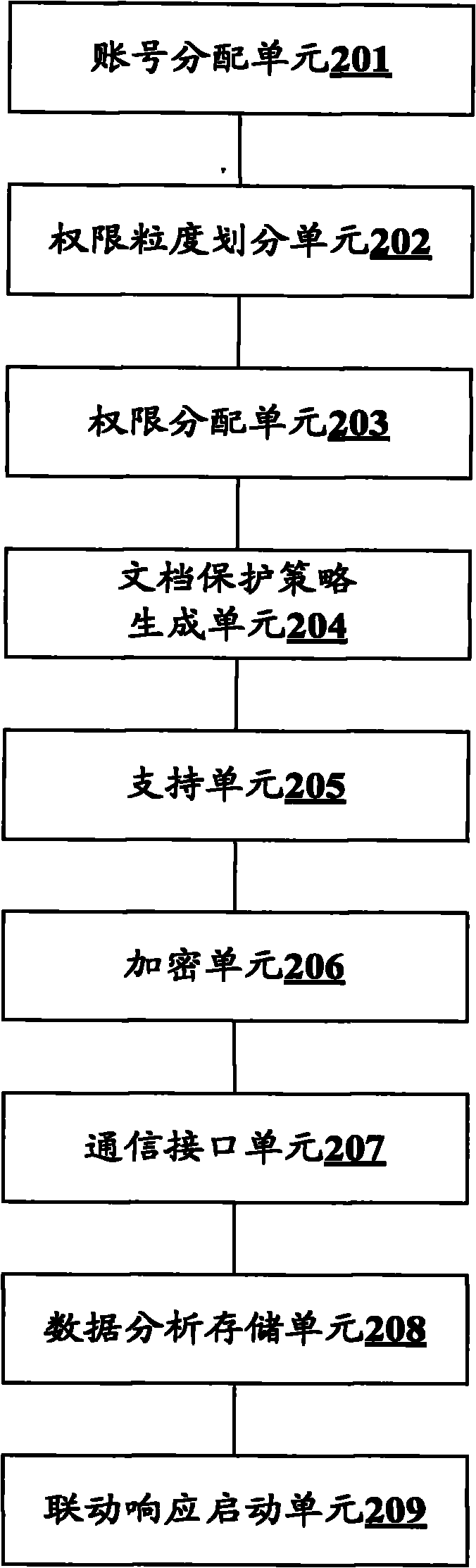
[0048] Figure 1A Figure 1B Among them, the document monitoring and management system based on comprehensive security audit adopts the B / S (browser / server) structure implementation scheme, which mainly includes a core module, two key modules, and other auxiliary function modules, and comprehensively utilizes identity authentication and access control , data encryption and security audit related technologies, identify and analyze behaviors that endanger the organization's information security, and provide document securit...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D Engineer
- R&D Manager
- IP Professional
- Industry Leading Data Capabilities
- Powerful AI technology
- Patent DNA Extraction
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2024 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com