Antitheft tracing method for ensuring computer security based on Internet
A security and computer technology, applied in the computer field, can solve problems such as poor practicability, single technology, and increased investment in hardware equipment, and achieve the effect of good practicability and wide application fields
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
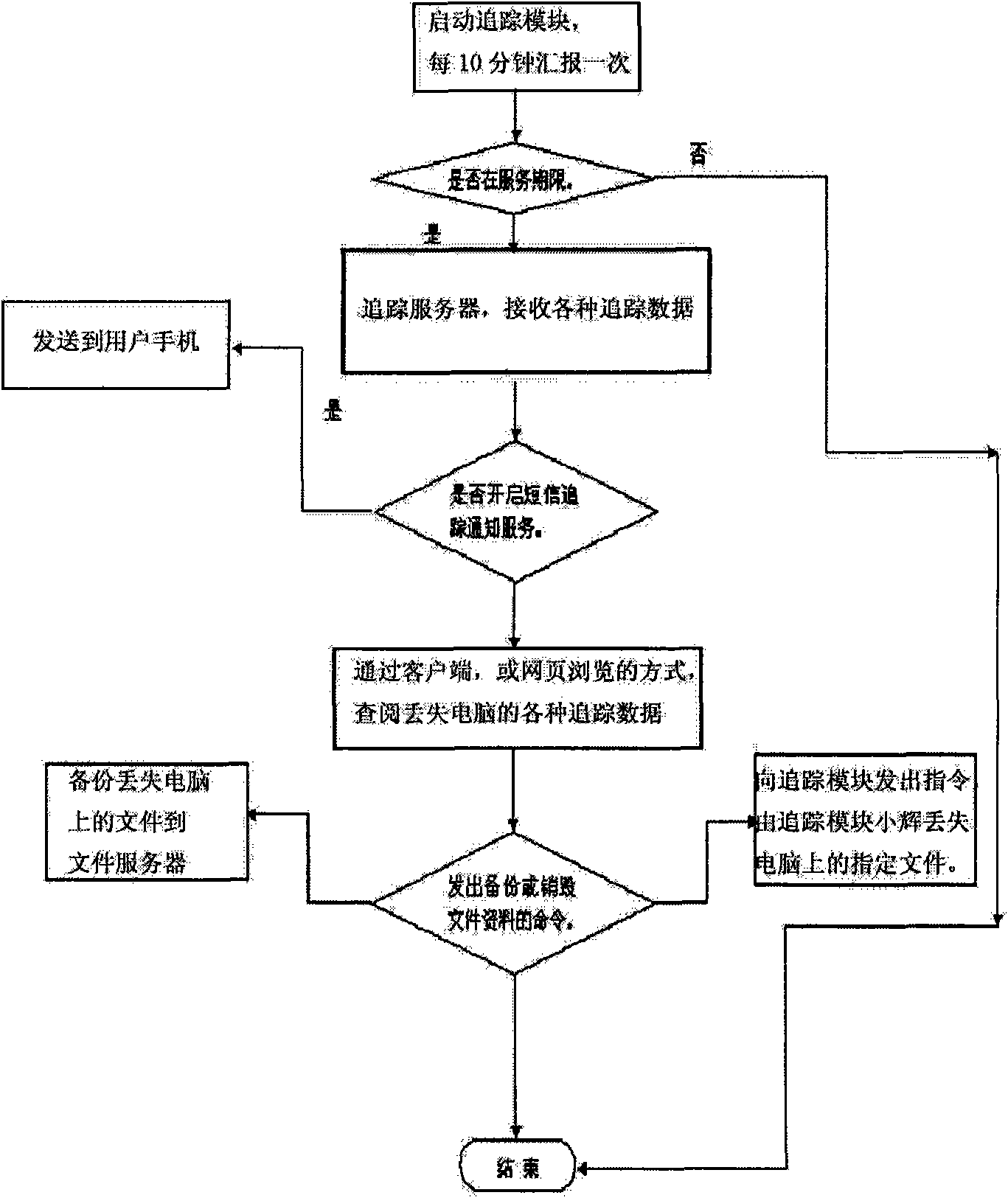
[0016] The present invention will be described in detail below in conjunction with the accompanying drawings and specific embodiments.
[0017] During implementation, an alarm module, command receiving module, tracking module, concealment module, anti-formatting module, firewall penetration protection module, and peripheral tracking server should be installed in the computer, so as to realize anti-theft, tracking, and file backup of the computer. .
[0018] The concrete steps of implementing the present invention are:
[0019] (1), the hidden module enters the registry of the computer, deletes the unloading item, and then utilizes the Windows Socket (2) SPI technology to hide the process of each module.
[0020] Winsock(2) SPI provides a Windows socket application programming interface (API) for applications to access network services, and also includes Winsock service provider interface (SPI) and ws(2)_(3)(2).dll. Here, the transmission service provider is taken as an exam...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D Engineer
- R&D Manager
- IP Professional
- Industry Leading Data Capabilities
- Powerful AI technology
- Patent DNA Extraction
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2024 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com