A method to respond to TOCTOU attacks against TPM trusted computing in the environment of multiple virtual domains
A technology of trusted computing and virtual domain, applied in computing, computer security devices, instruments, etc., to achieve the effect of maintaining effective utilization, strong scalability, and defense against TOCTOU attacks
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
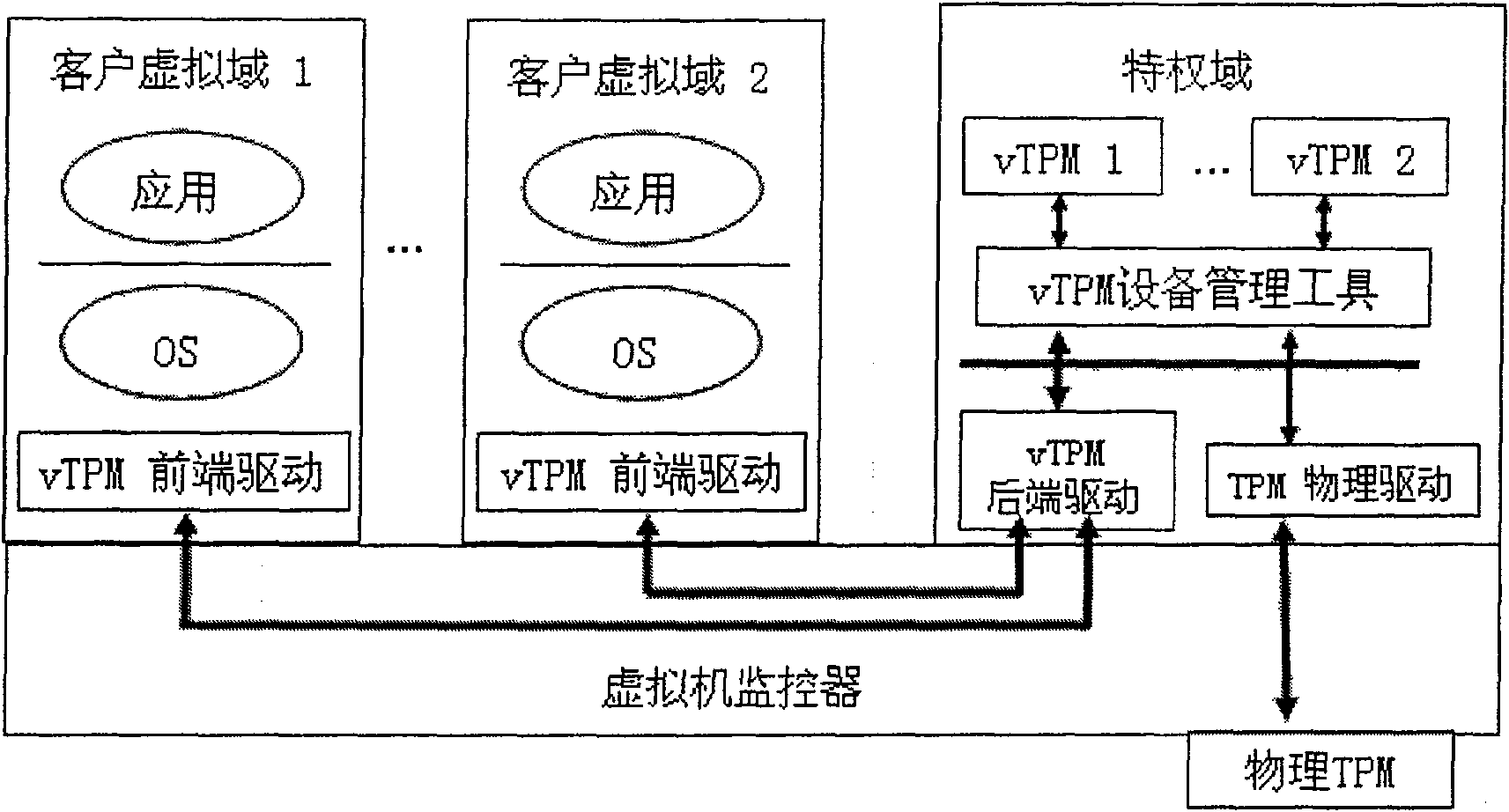
[0023] The present invention assumes figure 1 The system has been deployed, and the subordinate steps of the response method of the present invention are given below:
[0024] Step 1, integrate the memory monitoring module into the virtual machine monitor, then increase T_hypercall and T_vIRQ in the virtual machine monitor and the privileged domain kernel, and finally restart the computer.
[0025] Step 2, replace the enhanced virtual domain management tool figure 1 The method provides virtual domain management tools.
[0026] Step 3, replace the enhanced vTPM device program figure 1 The vTPM device program provided by the method.
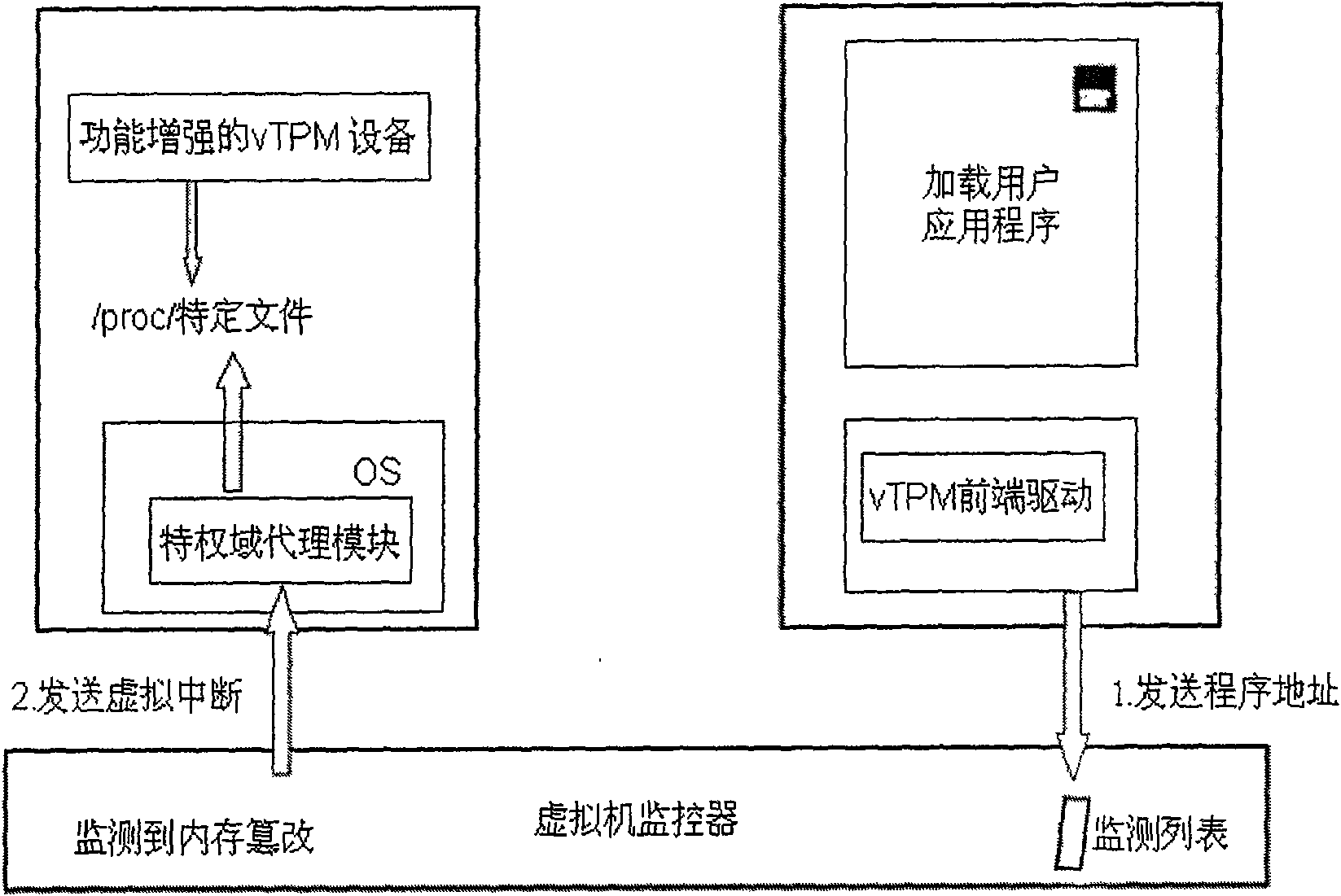
[0027] Step 4: Load the privileged domain proxy module in the privileged domain.
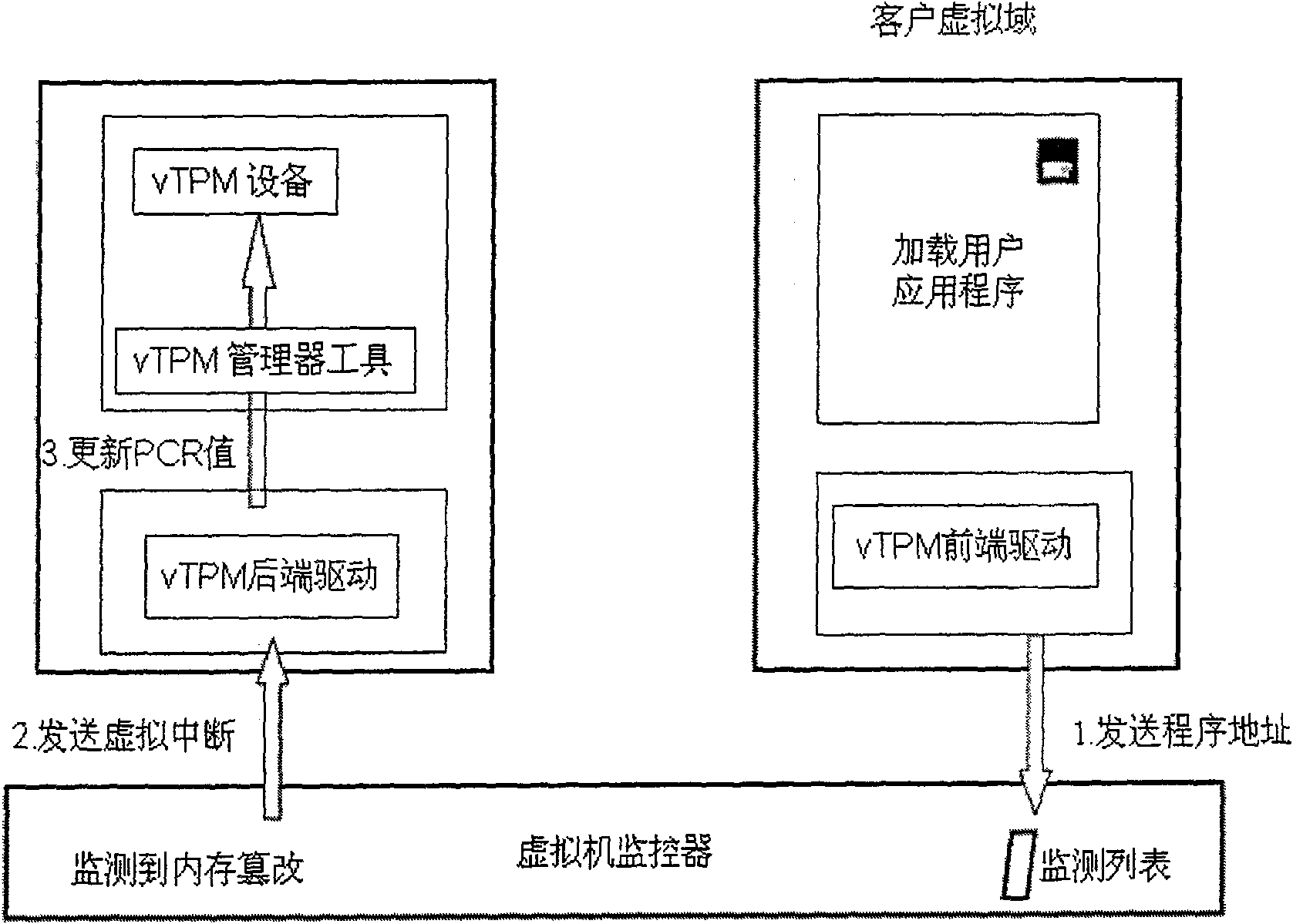
[0028] Combine below Figure 5 and Image 6 Describe in detail the workflow of the present invention to design the TOCTOU attack response method:
[0029] (1) In the privileged domain, the virtual domain is started by the enhanced virtual domain management too...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com