Method for authenticating user terminal
A user terminal and authentication technology, applied in the field of communication, can solve problems such as increased network message traffic, increased request processing delay, and impact on user experience, achieving the effects of process control, reduced processing overhead, and guaranteed reliability
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0063] In order to make the purpose, technical solution and advantages of the present invention clearer, the present invention will be further described in detail below in conjunction with the accompanying drawings and specific embodiments.
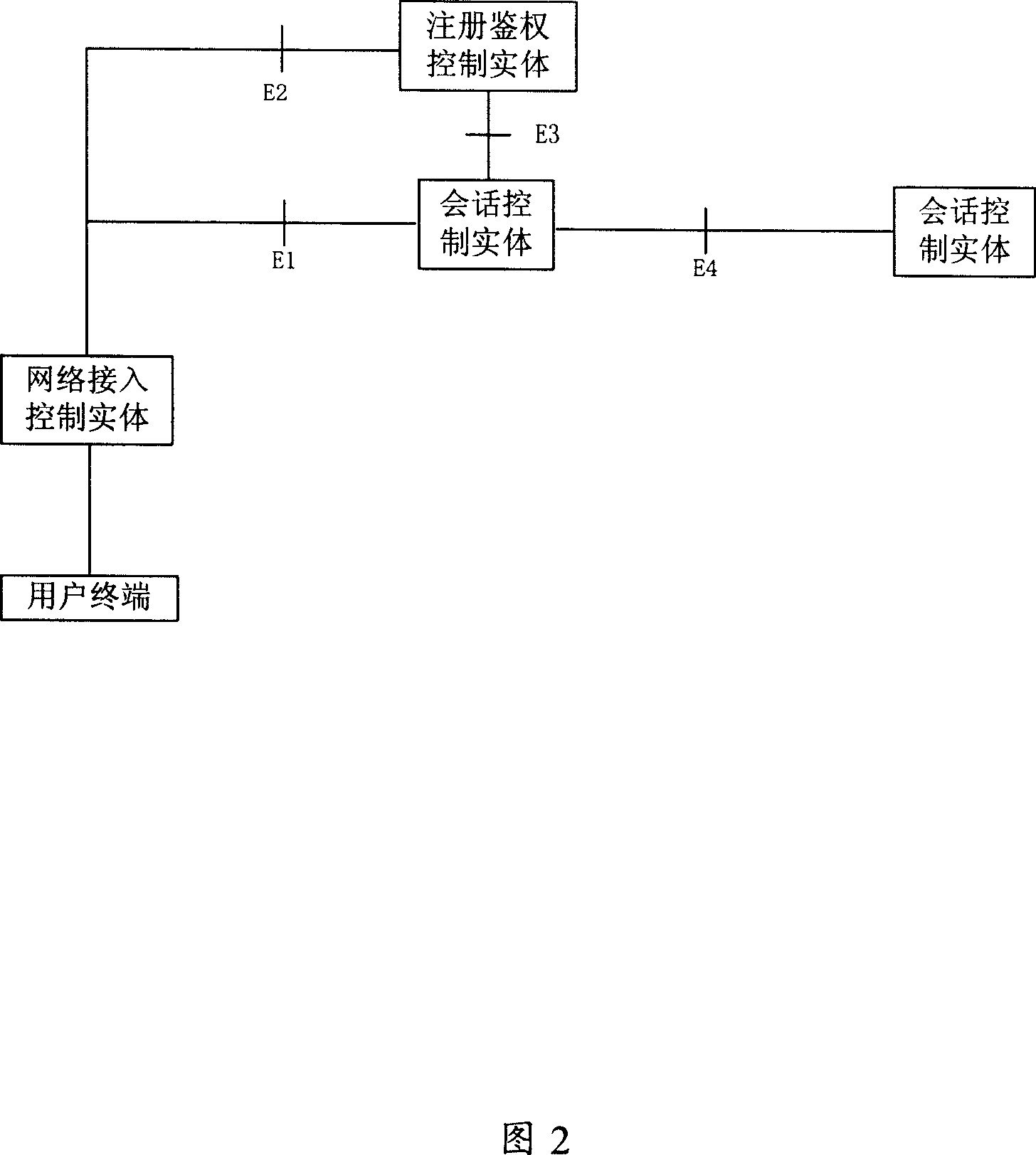
[0064] The implementation network of the present invention includes but not limited to packet networks such as IMS network, NGN network, and Internet network; the implemented signaling includes but not limited to SIP, HTTP, etc.; the authentication mode of the network to the terminal includes but not limited to IMS AKA, HTTP Digest, etc. Authentication method; the secure channel established between the terminal and the network access control entity includes but is not limited to IPSec secure channel, TLS secure channel, etc., or there is no secure channel. The implementation network logic structure of the present invention is as shown in Figure 2, wherein:
[0065] A user terminal is any type of communication terminal that can access a pa...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com