Identity authentication method and device
An identity authentication and identity technology, applied in the field of identity authentication methods and devices, can solve problems such as unimaginable consequences
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
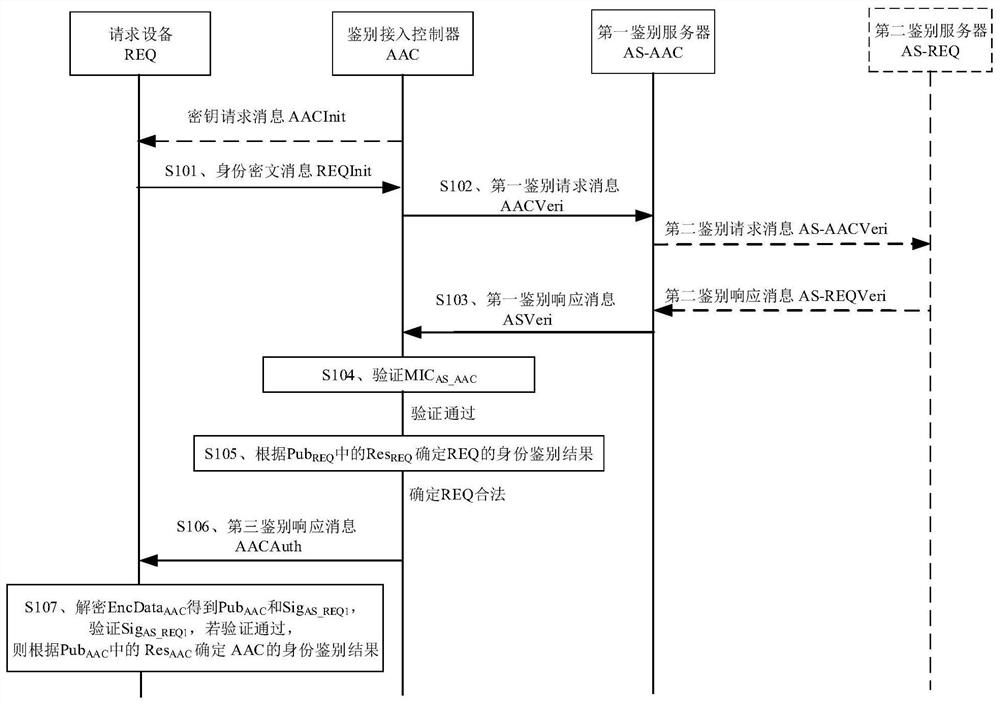
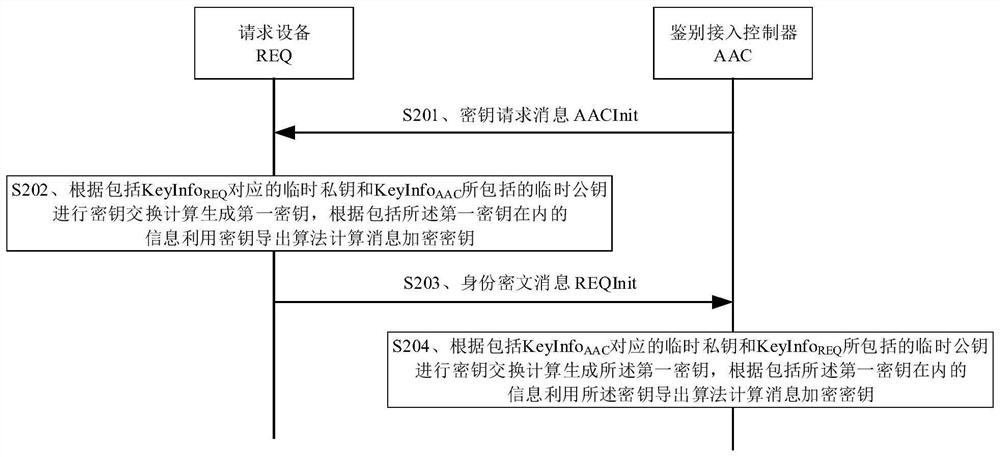
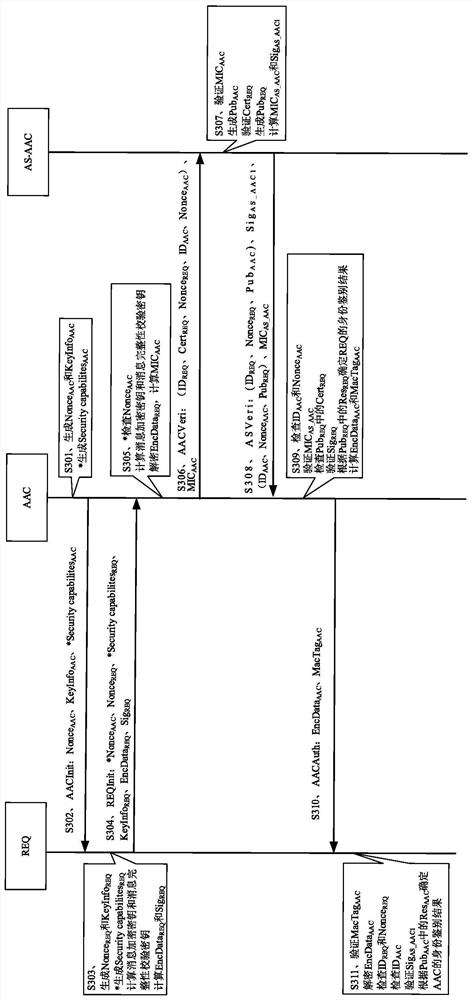
[0047] In a communication network, the requesting device can access the network through the authentication access controller. In order to ensure that the requesting device accessing the network belongs to a legitimate user and the network that the requesting device accesses is a legitimate network, the authentication between the access controller and the requesting device needs to be performed. Mutual Identity Authentication (MIA).
[0048] Taking the current wireless communication and mobile communication scenarios as an example, in the scenario where the requesting device accesses the wireless network through the authentication access controller, the requesting device may be a mobile phone, a personal digital assistant (PDA), a tablet computer, etc. The terminal device, the authentication access controller can be a network side device such as a wireless access point and a wireless router. In the scenario where the requesting device accesses the wired network through the auth...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - Generate Ideas
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com