Encrypted seal and bar-shaped data secondary encryption method
A technology of secondary encryption and seal, applied in image data processing, image data processing, digital data protection, etc., can solve the problems that enterprises cannot afford, the seal is easy to be forged, and the authenticity of the seal of the stamped document is difficult to verify.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
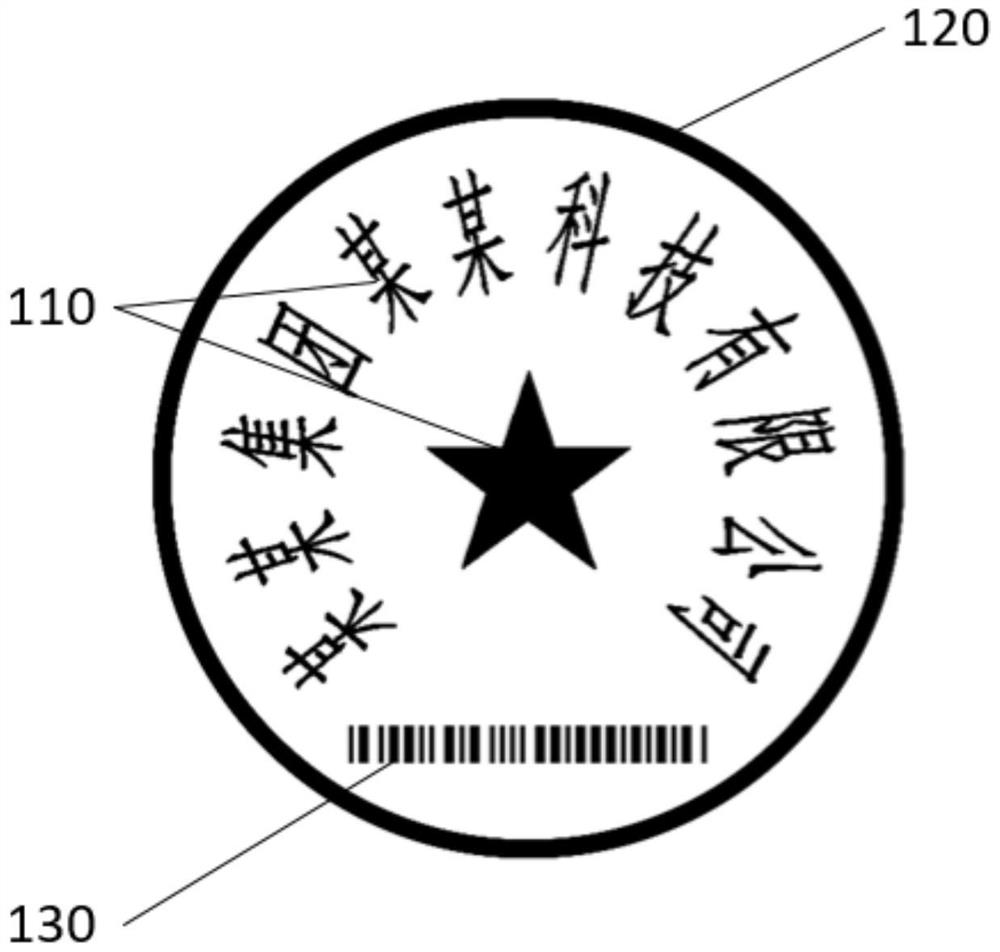
[0066] Such as figure 2 As shown, the seal of the present invention includes circle, ellipse and square, and the seal frame that present embodiment adopts is circular, and a kind of encrypted seal that present embodiment provides, comprises picture and text area 110, seal frame 120 and bar figure Encryption area 130, picture-text area 110 and bar-shaped digital encryption area 130 are all arranged in seal frame 120, and in the bar-shaped digital encryption area 130, be filled with encryption code, the shape of the bar-shaped digital encryption area of the present embodiment is strip in addition When receiving the seal request, the encryption code is generated, and the seal information of the stamped file is loaded on the encryption code. Different seal files will correspond to different encryption codes. In addition, the bar-shaped digital encryption area 130 A blank area is set between the graphic area 110 and the stamp frame 120 .
[0067] The encryption codes of the pre...
Embodiment 2
[0089] Such as Figure 8 As shown, the difference between the present embodiment and Embodiment 1 is that what the bar-shaped digital encryption area adopts is an arc-shaped digital encryption area, and the enciphered code-colored stamp frame 120 in the bar-shaped digital encryption area is arranged in an arc, which can satisfy different requirements. The requirements of customers or different requirements for the shape vision of the encrypted area.
Embodiment 3
[0091] Such as Figure 10 As shown, the difference between this embodiment and Embodiment 2 is that the encryption code in the bar-shaped digital encryption area 130 adopts a character string formed by a combination of numbers and letters. In this embodiment, the stamping information of the stamped document is recorded in the string of "FD16414F123184FSS15", and the steps for secondary encryption are as follows:
[0092] Obtain the string to be processed, including obtaining the pixel information of the string to be processed;
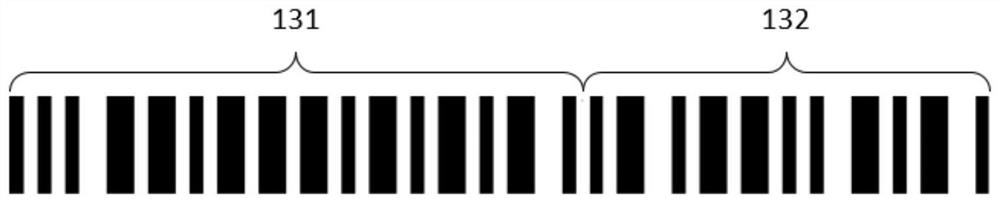
[0093] Split the character string to be processed, randomly select a position on the string as the split point and record the position information of the split point. In this embodiment, the randomly selected split point is located between the 10th character "5" and the 11th character Between characters "F", such as Figure 4 with Figure 5 As shown, the string to be processed is split into a first segment 131 and a second segment 132 to form two se...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - Generate Ideas
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com