Method and system for full-time dynamic supervision of codes and data in computer operation
A running, computer technology, applied in computer security devices, computing, digital data protection, etc., can solve the problems of difficult to implement technical solutions, difficult for regulators, impossible to review in real time, etc.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
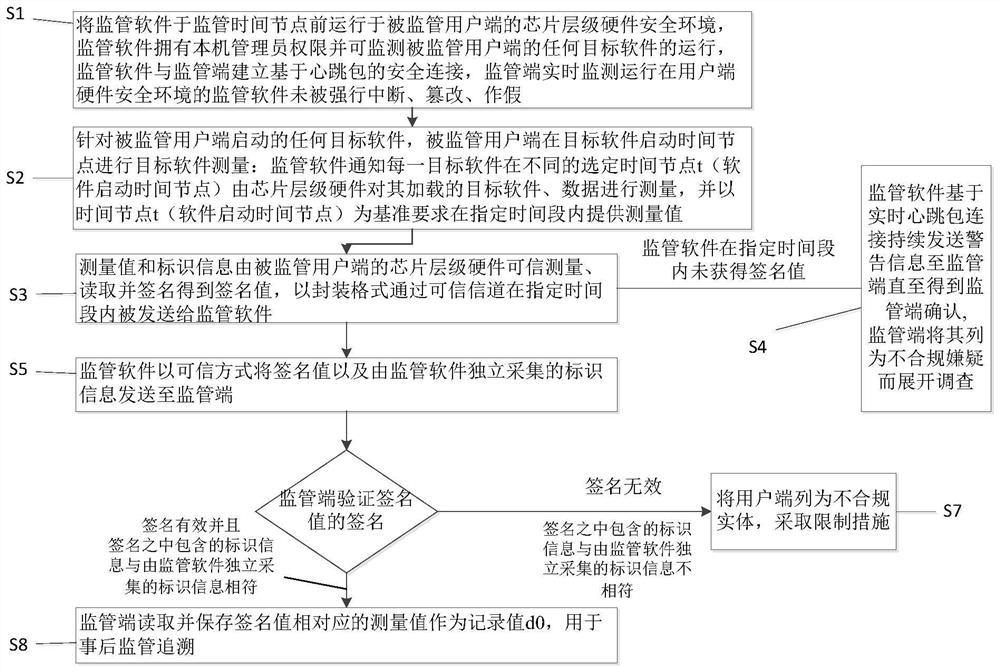
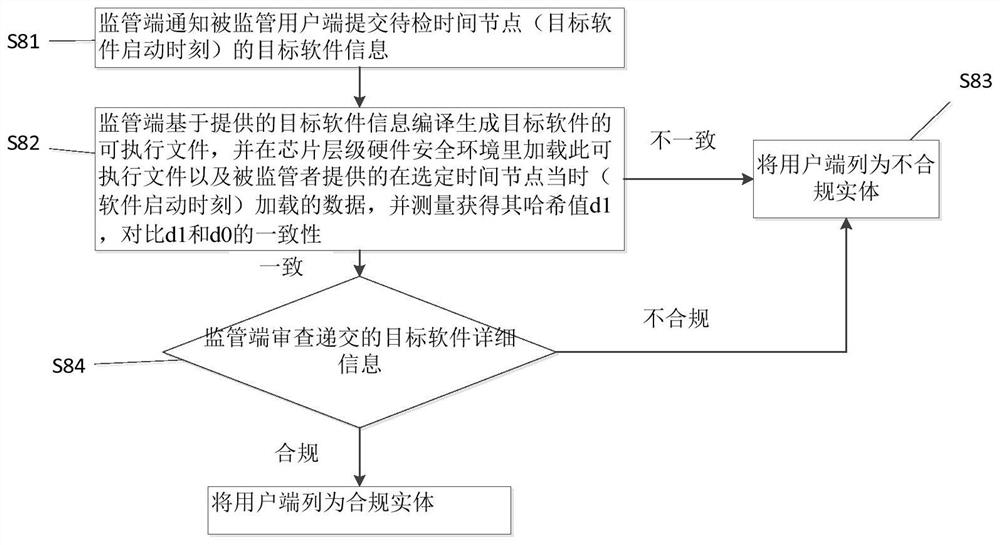
[0054] A method for dynamic supervision of code and data in computer operation at all times, such as figure 1 As shown, the method includes the following steps:
[0055] S1. Run the supervision software in the chip-level hardware security environment of the supervised client before the supervision time node. The supervision software has local administrator rights and can monitor the operation of any target software on the supervised client. The supervision software and the supervision terminal are based on With the secure connection of heartbeat packets, the supervisory terminal monitors in real time that the supervisory software running in the hardware security environment of the client has not been forcibly interrupted, tampered with, or falsified; the typical chip-level hardware security environment is a trusted execution environment based on Intel SGX, and the supervisory terminal can pass The remote authentication mechanism of Intel SGX remotely verifies the credibility a...
Embodiment 2
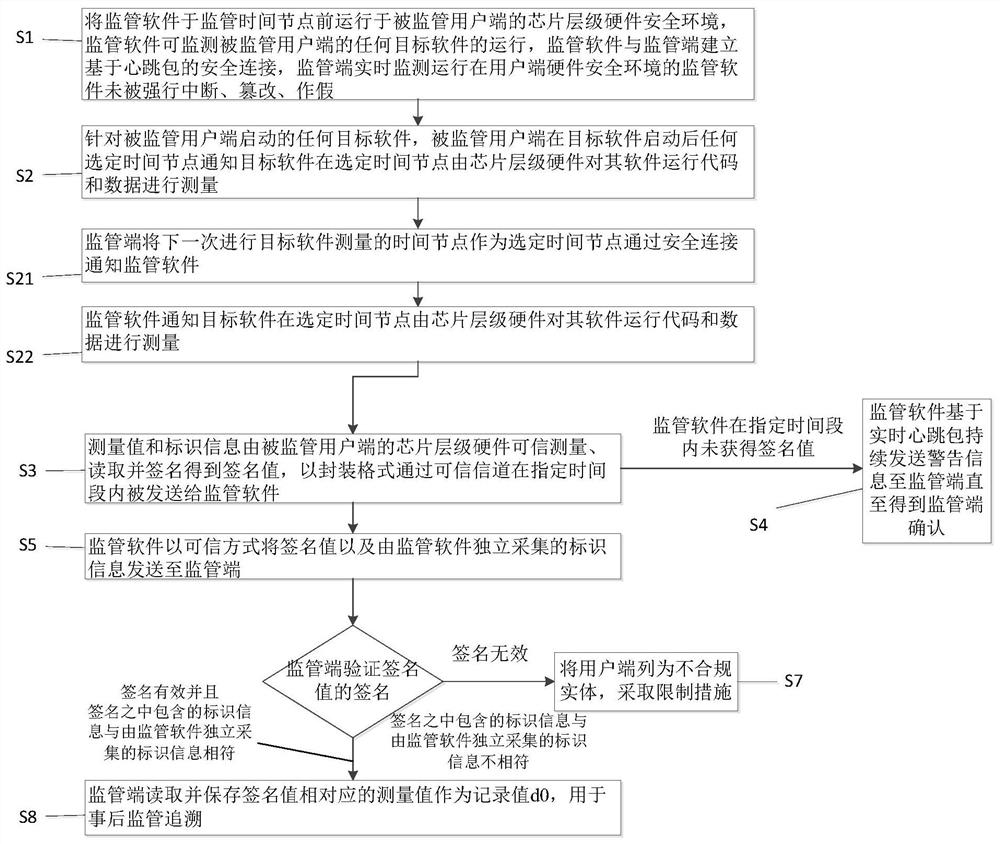
[0073] A method for dynamic supervision of code and data in computer operation at all times, such as image 3 As shown, the method includes the following steps:
[0074] S1. Run the supervision software on the chip-level hardware security environment of the supervised client before the supervision time node. The supervision software can monitor the operation of any target software on the supervised client. The supervision software and the supervision terminal establish a secure connection based on heartbeat packets. The terminal monitors in real time that the supervisory software running in the hardware security environment of the user terminal has not been forcibly interrupted, tampered with, or falsified; a typical chip-level hardware security environment is a trusted execution environment based on Intel SGX, and the supervisory terminal can remotely authenticate through the Intel SGX remote authentication mechanism. Verify the credibility and integrity of regulatory softwar...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D Engineer
- R&D Manager
- IP Professional
- Industry Leading Data Capabilities
- Powerful AI technology
- Patent DNA Extraction
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2024 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com