Processor transient attack defense method based on cache random invalidation
A cache management and caching technology, which is applied in the computer field, can solve problems such as changes in the cache layout and difficulty for attackers to accurately detect the cache layout, and achieve the effect of preventing secret values
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0036] In order to make the object, technical solution and advantages of the present invention clearer, the present invention will be further described in detail below through specific embodiments in conjunction with the accompanying drawings. It should be understood that the specific embodiments described here are only used to explain the present invention, not to limit the present invention.
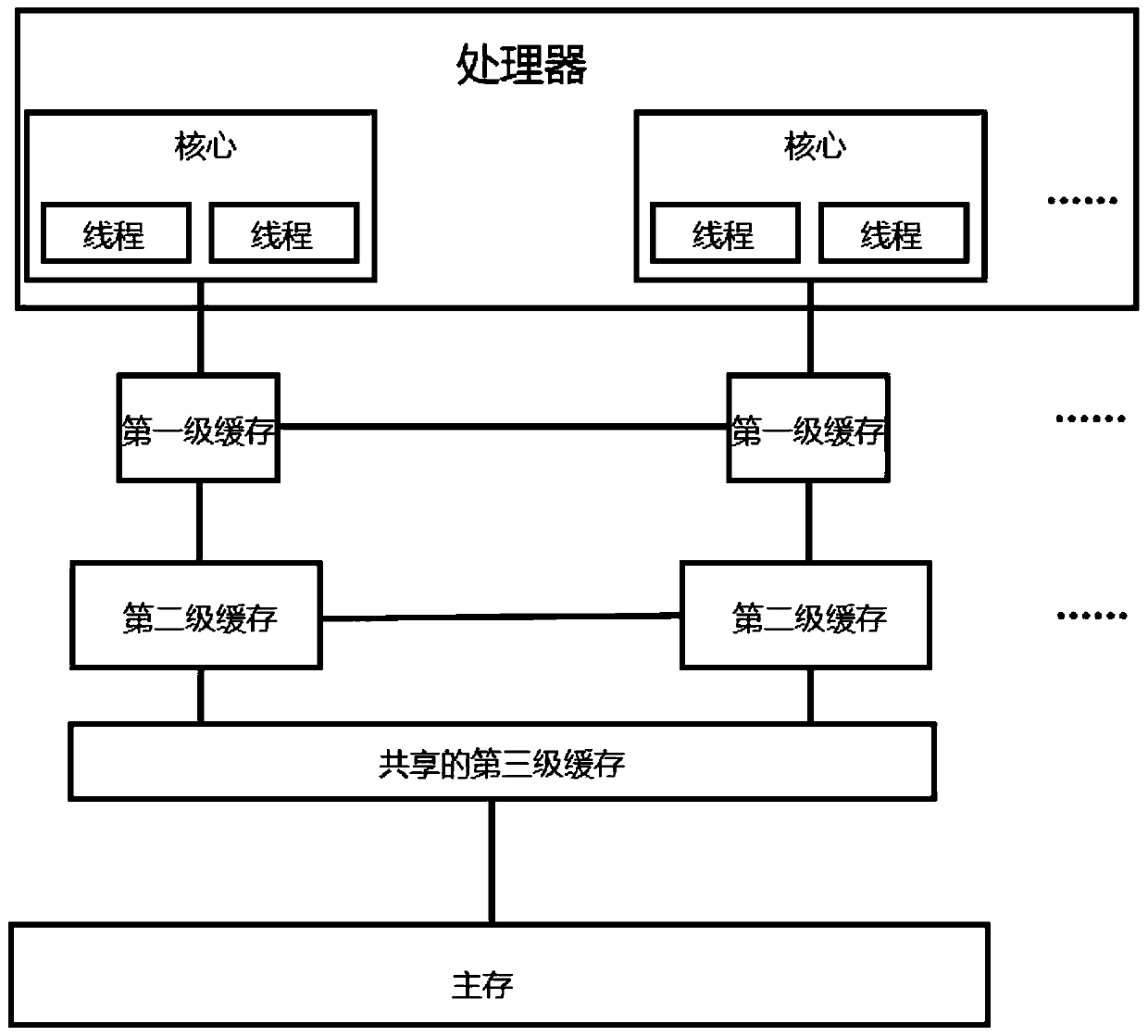
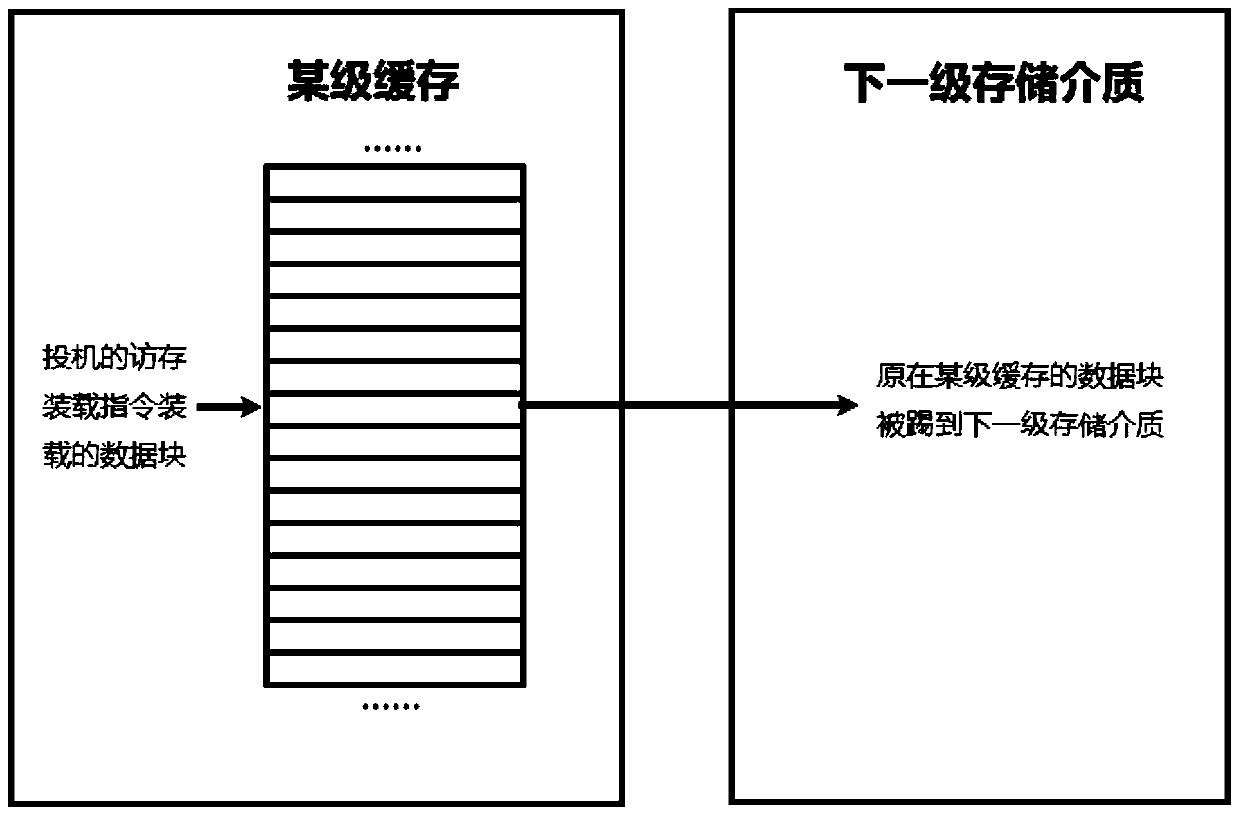
[0037] As mentioned in the background technology section, modern processors have hardware loopholes, and the cache architecture of the processor needs to be modified to better defend against such attacks as meltdown attacks and ghost attacks. The main problem of this type of attack is that the attacker uses out-of-bounds speculative execution to change the cache layout, and then obtains the secret through side channel detection. For example, see figure 2 , the attacker loads the data block (the secret value can be deduced through its address, because the address is the secret value m...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com