Key backup and recovery method based on integrated encryption technology
A recovery method and encryption algorithm technology, applied in the field of information security, can solve problems such as imperfect key storage methods
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
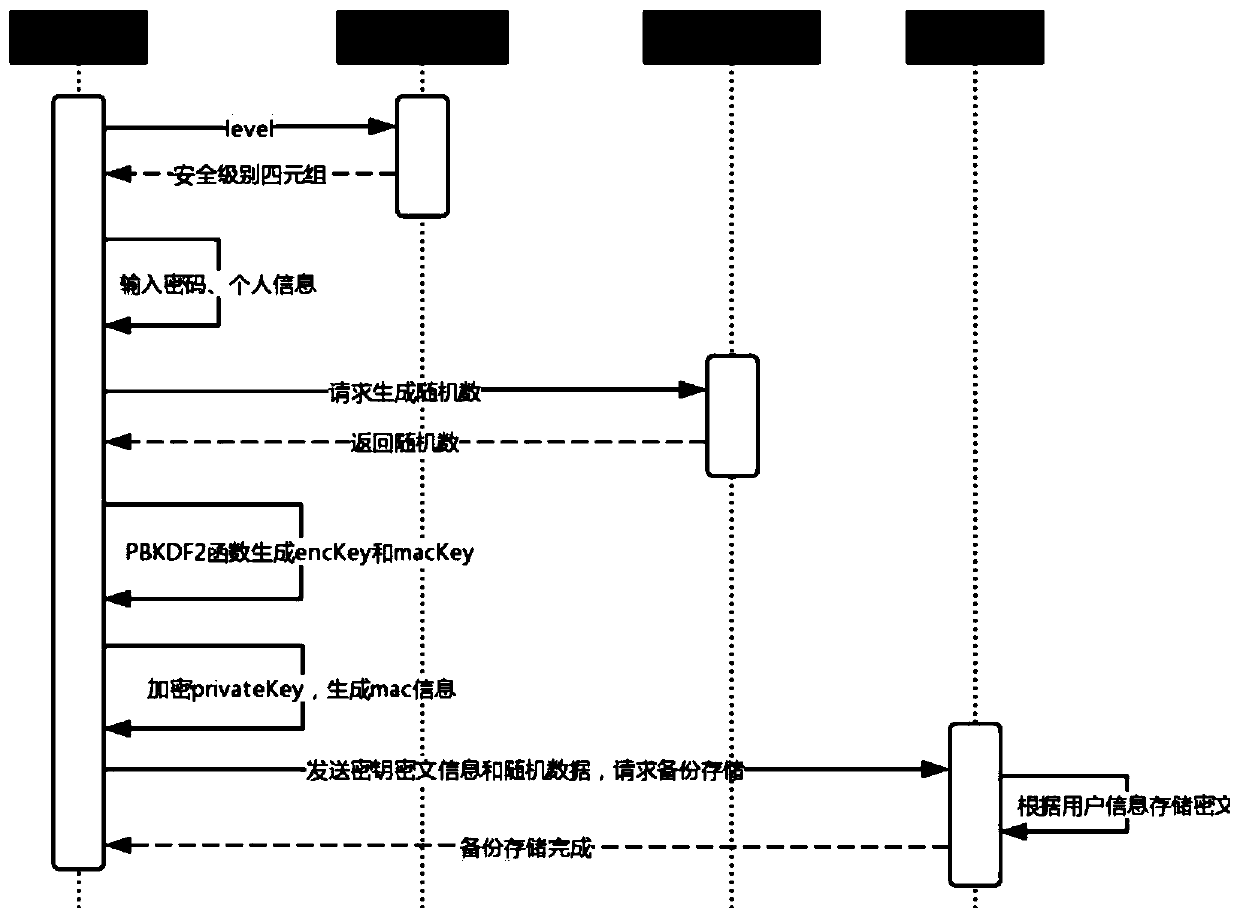
[0033] Specific embodiments of the present invention will be described in detail below in conjunction with the accompanying drawings. Implementation is carried out on the premise of the technical solution of the present invention, so that those skilled in the art can better understand the technical characteristics and functional characteristics of the present invention, but the protection scope of the present invention is not limited to the following examples.
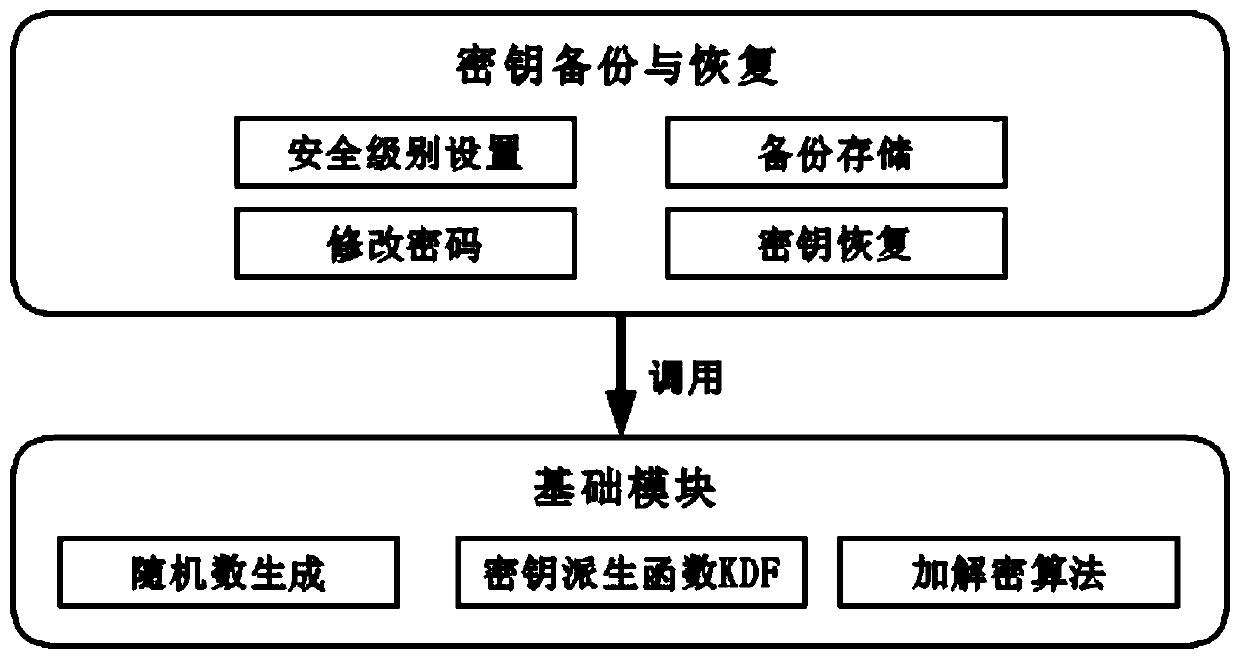
[0034] In this embodiment, the encrypted key is stored in a third-party escrow institution, and the escrow institution provides key storage and recovery services. The custodian provides functions such as user registration, key backup, key recovery, and password change.
[0035] First, the custodian agency provides a registration interface. Users register an account with the custodian agency. The account contains an account number and password. With an account, they can use the key backup and key recovery functions of t...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D Engineer
- R&D Manager
- IP Professional
- Industry Leading Data Capabilities
- Powerful AI technology
- Patent DNA Extraction
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2024 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com