Key factor generation method of root key
A root key and key technology, applied in the field of information security cryptography, can solve problems such as danger, insecure key transmission, and insecurity, and achieve the effect of improving security and avoiding malicious use.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment
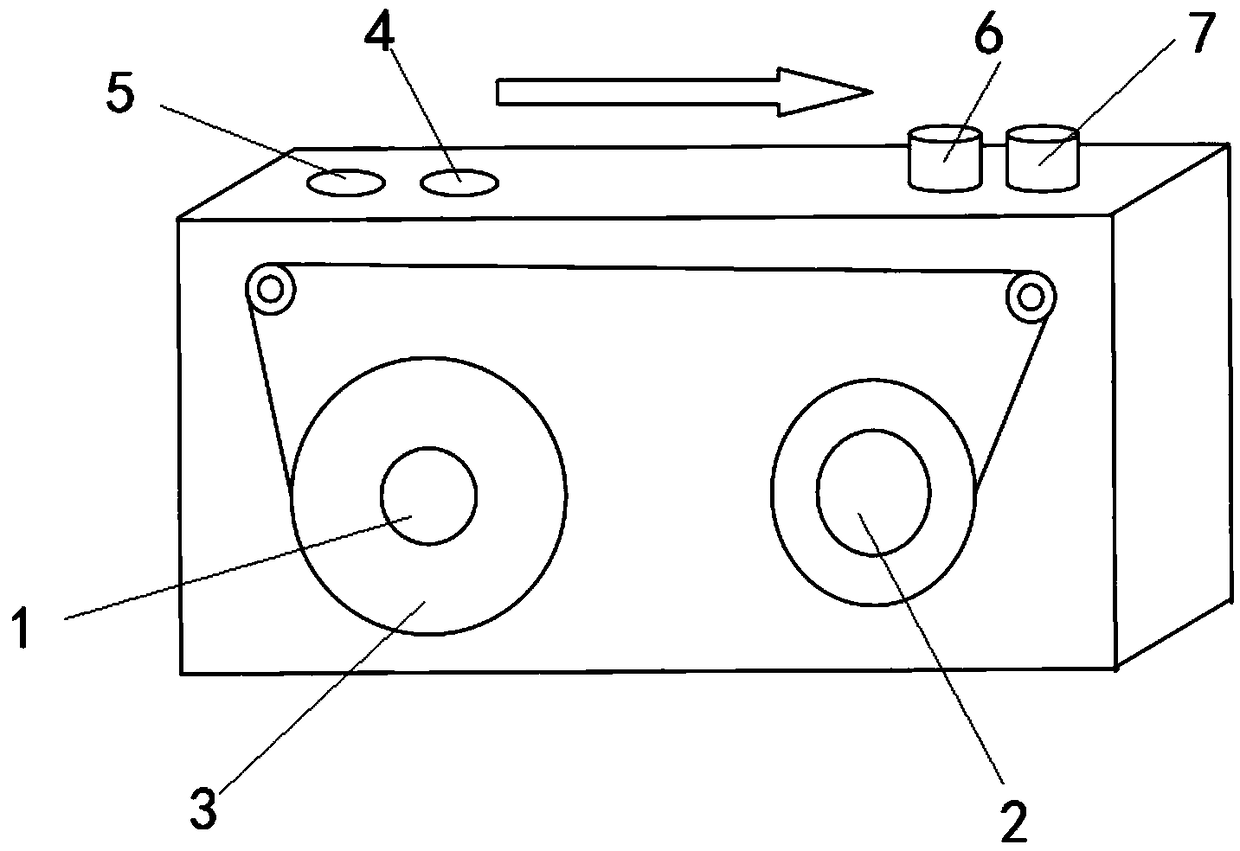
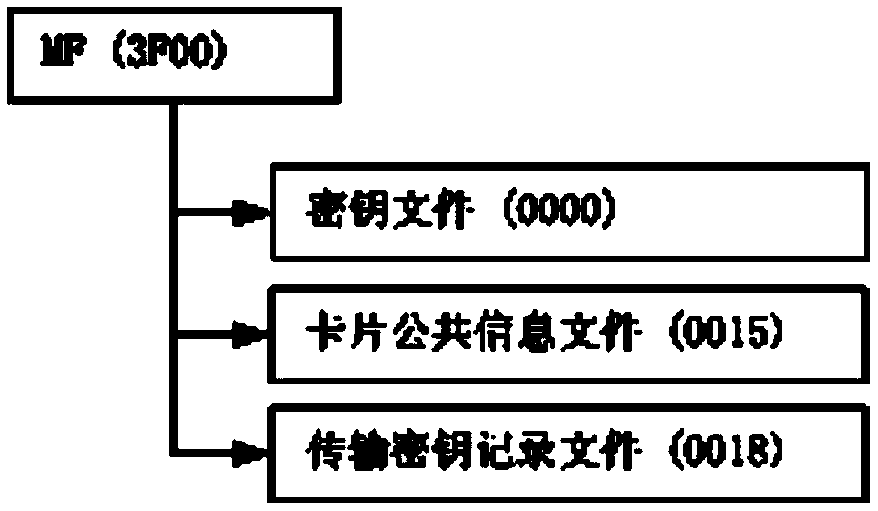
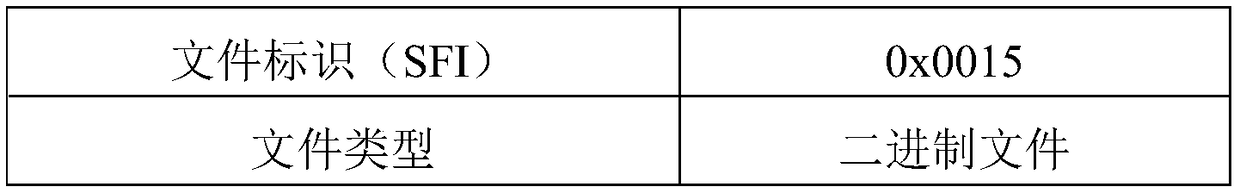
[0045] In this embodiment, three levels of equipment asset management are taken as an example to illustrate the application process of the method of the present invention. When there are more levels, the application idea is the same. The SAM card that controls the read and write permissions of asset electronic tags is placed in the readers held by the operation and maintenance personnel at each level. The SAM card can read and write the electronic tags of the current level and the lower level, but cannot read and write the electronic tags of the upper level. The important basic information commonly used in the operation and maintenance of the equipment is placed in each equipment asset electronic label, including the configuration information of the network to which the equipment belongs, the manufacturer information of the equipment, and the past operation and maintenance records of the equipment.
[0046] In this embodiment, the equipment asset electronic tags of a typical en...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com