Cloud computing matrix determinant secure outsourcing computation encryption method
An encryption method and security outsourcing technology, which is applied in the field of security outsourcing computing and encryption, to reduce time complexity and improve efficiency
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0024] Below in conjunction with accompanying drawing and embodiment the present invention is described in detail:
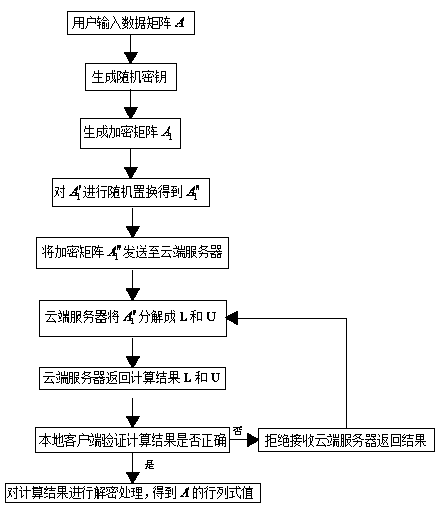
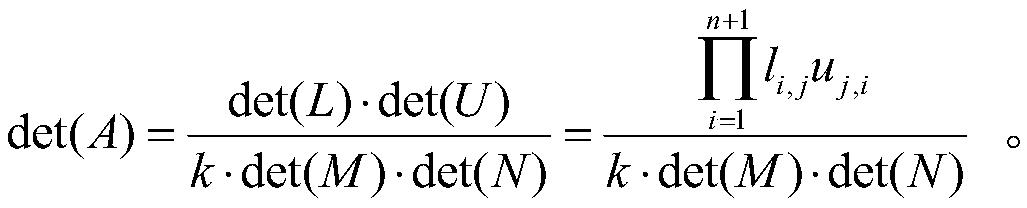
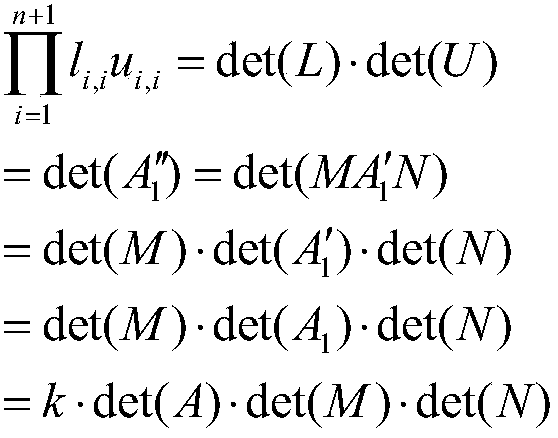
[0025] Such as figure 1 As shown, a secure outsourcing calculation and encryption method of a matrix determinant in cloud computing according to the present invention includes a key module, an encryption module, a calculation module, a verification module and a decryption module, wherein the key module, the encryption module, and the verification module The decryption module and the decryption module are set on the user's local client, and the calculation module is set on the cloud server, which includes the following steps in turn:
[0026] A: The local client reads the data entered by the user and forms a matrix A:
[0027] Matrix A is a square matrix of order n; where n is a positive integer;
[0028] B: The local client preprocesses matrix A to generate encrypted matrix A 1 "":
[0029] Step B includes the following specific steps:
[0030] B1: A set ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D Engineer
- R&D Manager
- IP Professional
- Industry Leading Data Capabilities
- Powerful AI technology
- Patent DNA Extraction
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2024 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com