Multi-keyword searchable encryption method supporting numerical attribute comparison
A technology of numerical attributes and encryption methods, applied in the field of information security
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
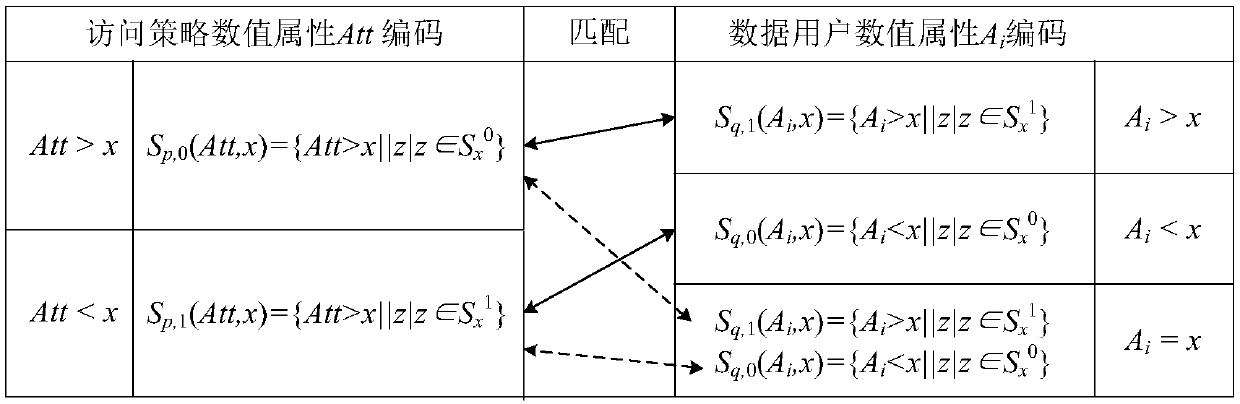
Image
Examples
Embodiment Construction
[0051] The present invention will be further described below in conjunction with the accompanying drawings and specific embodiments.
[0052] Such as figure 1 As shown, the present invention provides a multi-keyword searchable encryption method that supports numerical attribute comparison, comprising the following steps:
[0053] Step 1, system initialization: such as figure 1 As shown in ① in , the third-party trusted entity TTP generates the public parameter pm and the master key msk according to the security parameter k, where:
[0054] Public parameter pm={G,G T ,e,p,g,h 1 ,H 2 , g a , g b , g c}, master key msk={a,b,c};
[0055] where G is the additive cyclic group of order p, g is the generator of G, and G T is the p factorial cyclic group, e is the bilinear map G×G→G T , H 1 Indicates that the collection {0,1} * Hash function mapped to the additive cyclic group G of order p, H 2 Indicates that the collection {0,1} * Mapped to the integer ring Z of order p ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com