Method and an apparatus for realizing network traceless honeypot
A technology of a traceless honeypot and an implementation method, applied in the field of information security, can solve problems such as being easily perceived as a honeypot, and achieve the effect of being easily confused and ensuring concealment
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0029] In order to enable those skilled in the art to better understand the technical solutions in the embodiments of the present invention, and to make the above-mentioned purposes, features and advantages of the present invention more obvious and easy to understand, the technical solutions in the present invention will be further detailed below in conjunction with the accompanying drawings illustrate.
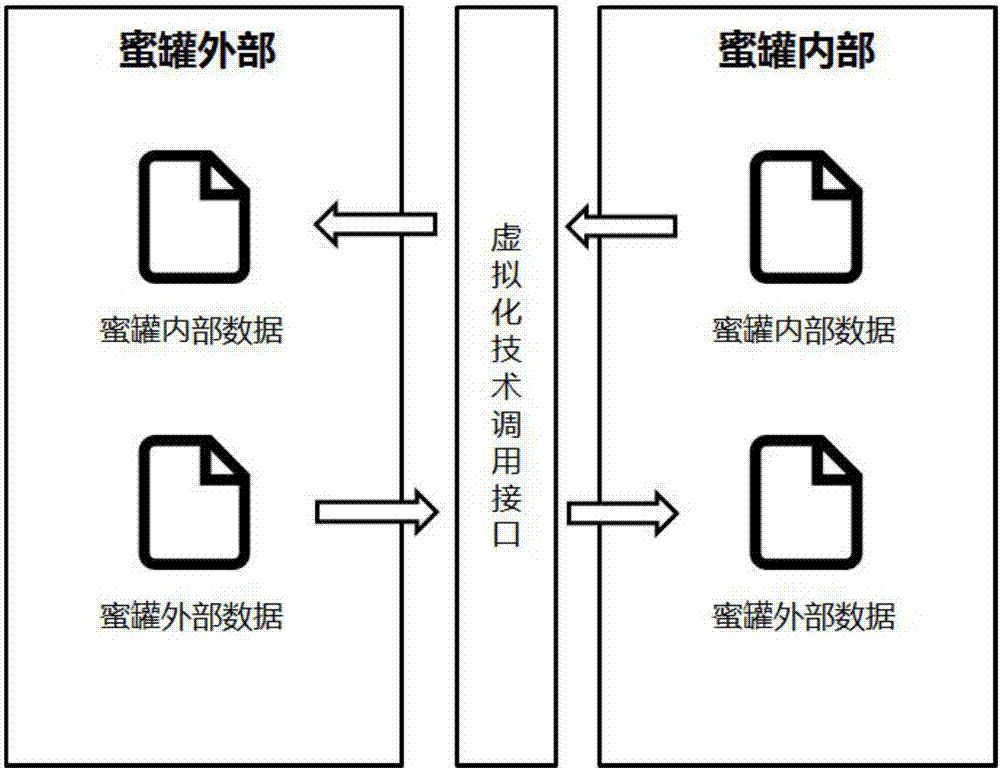
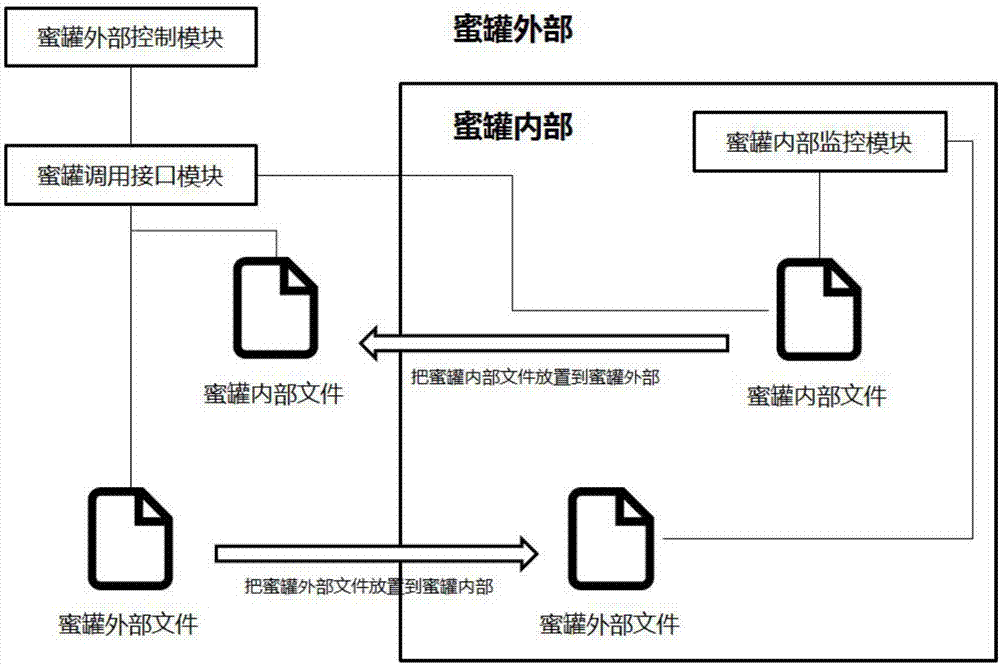
[0030] The present invention provides a method and device for implementing a network traceless honeypot. Through the virtualization technology, two-way data transmission between the outside of the honeypot and the inside of the honeypot is realized. During the process of data transmission, no data is generated inside the honeypot. Network traffic solves the problem in the existing honeypot technology that attackers can easily find out that they are in the honeypot by detecting network traffic, enhances the concealment of the honeypot, and achieves the effect of being traceless...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com