Loophole severity assessment and repair method
A technology of severity and vulnerability, which is applied in the field of vulnerability severity assessment, can solve the problem that the priority of vulnerability repair cannot be determined, and achieve the effect of avoiding major harm and improving security
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0046] The present invention will be further described in detail below in combination with specific embodiments. However, it should not be understood that the scope of the above subject matter of the present invention is limited to the following embodiments, and all technologies realized based on the content of the present invention belong to the scope of the present invention.
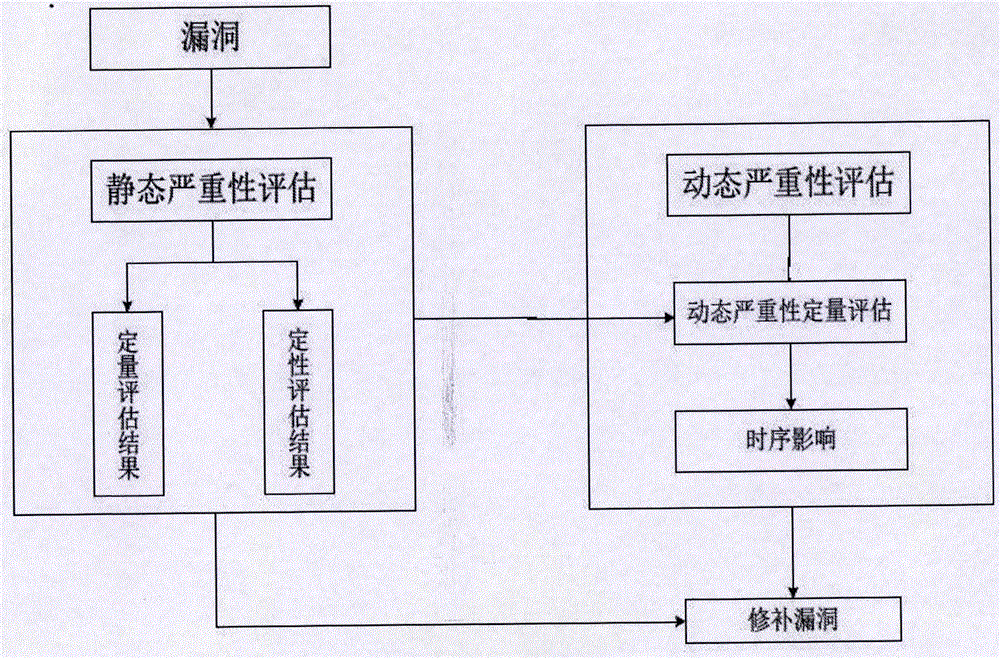
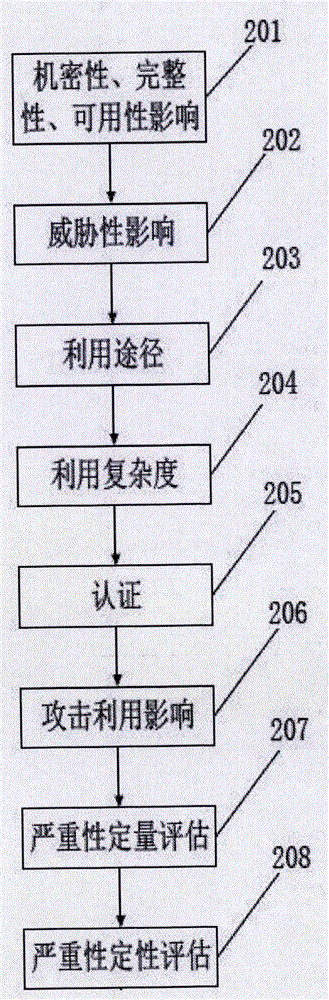
[0047] An embodiment of the present invention shows a schematic diagram of a vulnerability severity assessment method, the method comprising:
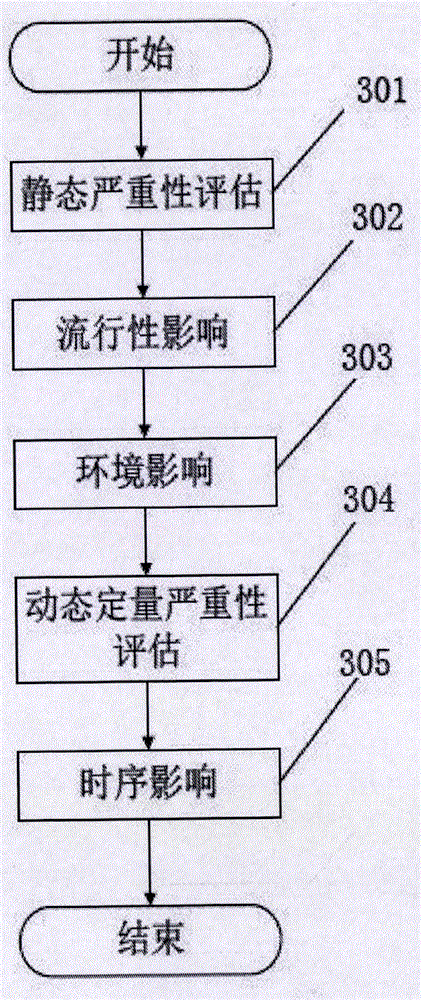
[0048] S101. Extract M vulnerabilities of the target host, and calculate a static severity assessment result of each vulnerability according to at least one important attribute information of each vulnerability;
[0049] S102. When the static severity assessment results of N vulnerabilities among the M vulnerabilities are the same, calculate a dynamic severity quantitative score for each of the N vulnerabilities;
[0050] S103. When the dynamic severity quant...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - Generate Ideas
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com