Structural characteristics-based malicious code heuristic detection method and system
A technology of malicious code and structural characteristics, applied in the field of information security, to achieve high accuracy, fast detection speed, and slow overcoming speed
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0023] In order to enable those skilled in the art to better understand the technical solutions in the embodiments of the present invention, and to make the above-mentioned purposes, features and advantages of the present invention more obvious and easy to understand, the technical solutions in the present invention will be further detailed below in conjunction with the accompanying drawings illustrate.
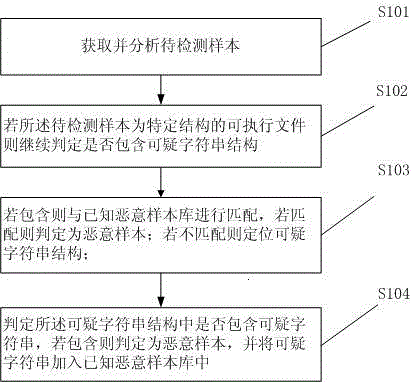
[0024] A heuristic detection method for malicious code based on structural features, such as figure 1 shown, including:
[0025] S101 acquire and analyze the sample to be tested;
[0026] S102, if the sample to be detected is an executable file with a specific structure, continue to determine whether it contains a suspicious character string structure;
[0027] S103, if it is included, it will be matched with the known malicious sample library, if it is matched, it will be determined as a malicious sample, if it does not match, the suspicious string structure will be locate...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - Generate Ideas
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com