Point-to-point elliptic-curve type digital signature algorithm and signature verification method based on the same
An elliptic curve and digital signature technology, applied in the field of information security, can solve problems such as inability to implement man-in-the-middle attacks
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
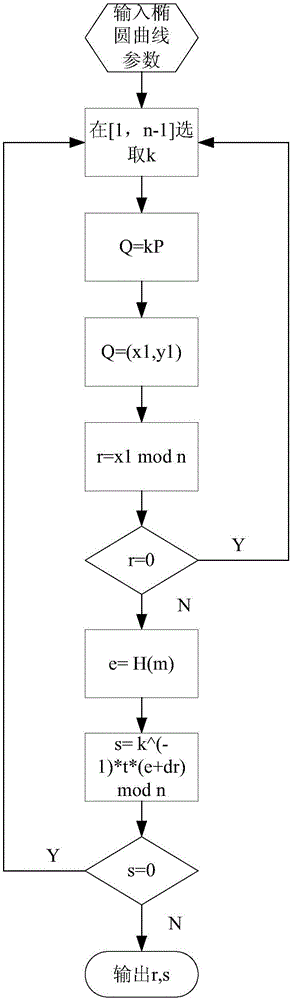
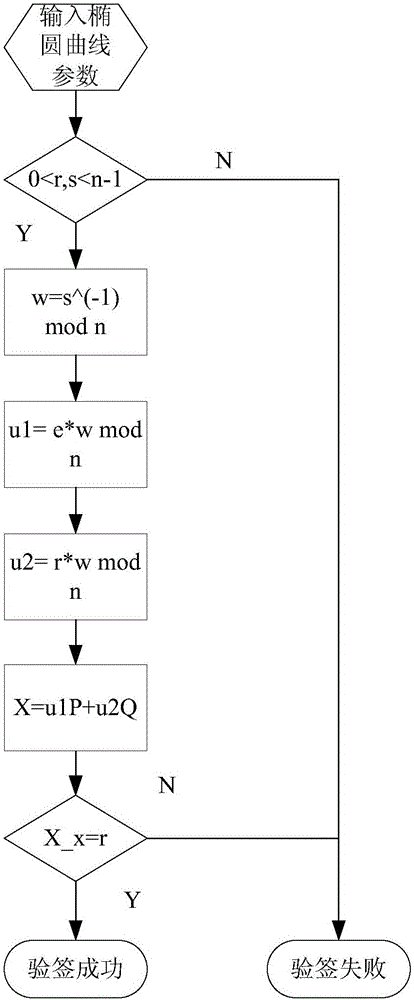
[0051] figure 1 The following flow charts are provided to illustrate specific implementation details of the present invention.
[0052] The National Institute of Standards and Technology (NIST) recommends five sets of parameters for elliptic curve cryptography in the prime field. One set of parameters is adopted in this embodiment, which is as follows:
[0053] In a finite field Fp, there is an elliptic curve E, which is defined as follows:
[0054] E: y 2 =x 3 +ax 2 +b
[0055] in:
[0056] p = 0xFFFFFFFF00000001000000000000000000000000FFFFFFFFFFFFFFFFFFFFFFFF;
[0057]a = 0xFFFFFFFF00000001000000000000000000000000FFFFFFFFFFFFFFFFFFFFFFFC;
[0058] b=0x5ac635d8aa3a93e7b3ebbd55769886bc651d06b0cc53b0f63bce3c3e27d2604b.
[0059] The coordinates of the base point P are,
[0060] [0x6B17D1F2E12C4247F8BCE6E563A440F277037D812DEB33A0F4A13945D898C296,
[0061] 0x4fe342e2fe1a7f9b8ee7eb4a7c0f9e162bce33576b315ececbb6406837bf51f5]
[0062] The order n of the base point is,
...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - Generate Ideas
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com