Method, device, terminal device and system for generating shared key
A shared key and secret key technology, which is applied in the electronic field, can solve the problems of affecting the output of quantum key quantity, unable to generate quantum key, insufficient key distribution, etc.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0174] In the following description, numerous specific details are set forth in order to provide a thorough understanding of the application. However, the present application can be implemented in many other ways different from those described here, and those skilled in the art can make similar promotions without violating the connotation of the present application. Therefore, the present application is not limited by the specific implementation disclosed below.
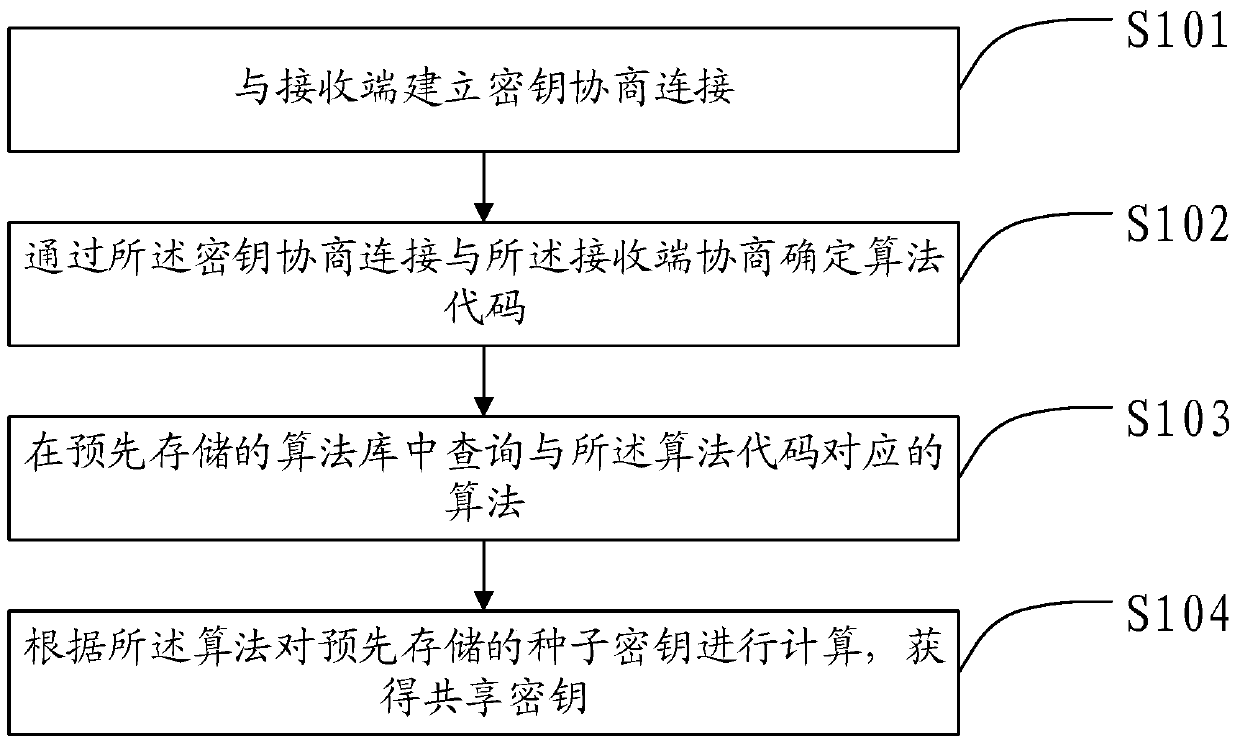
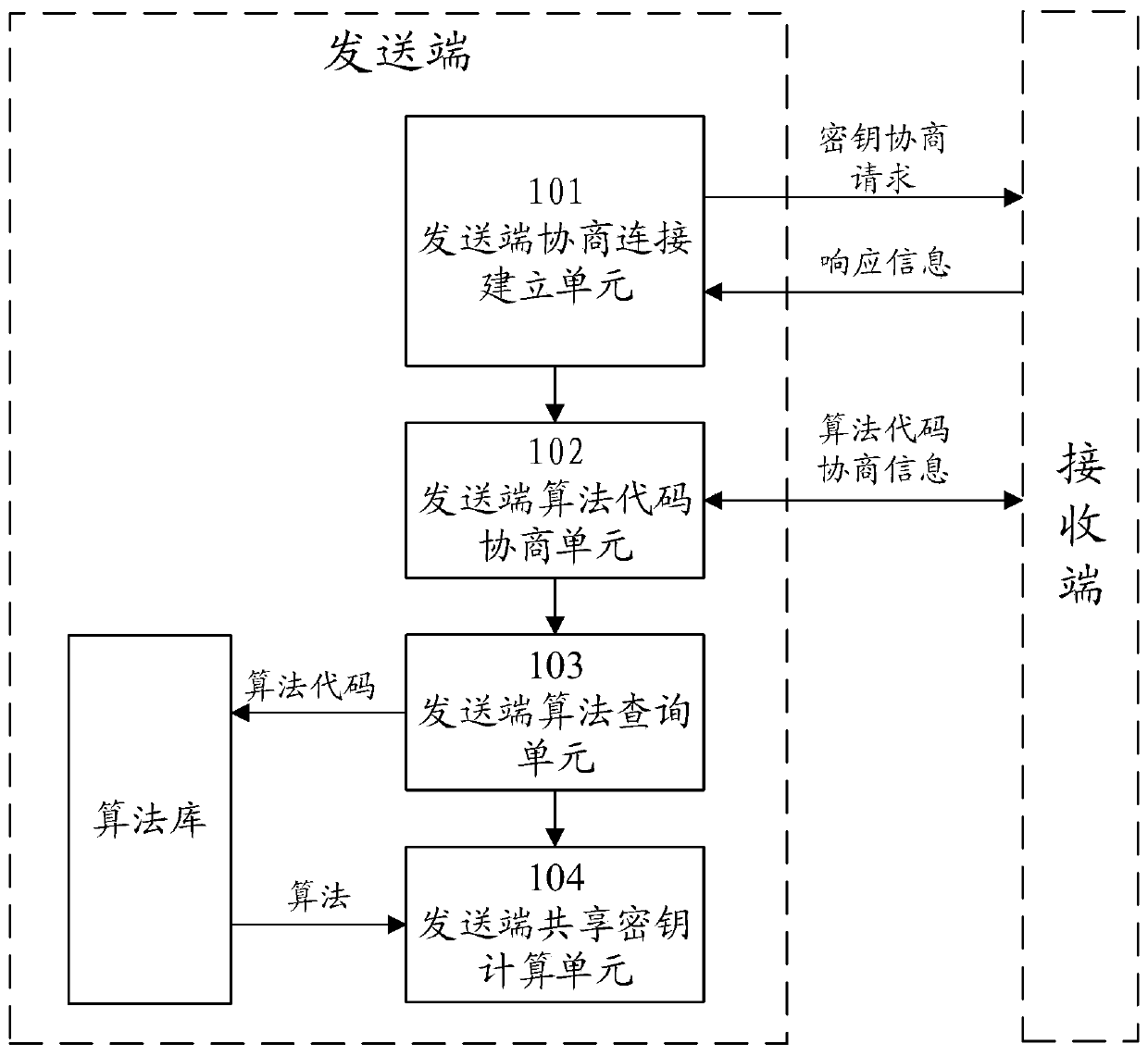
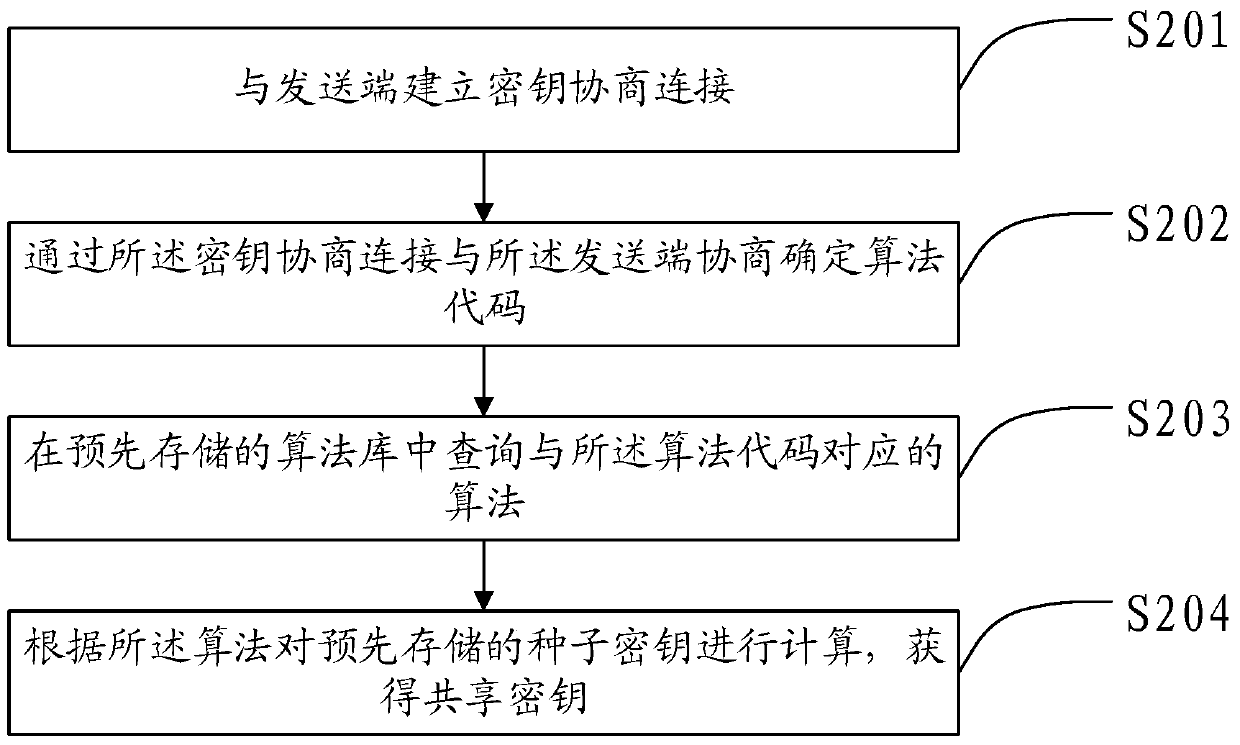
[0175] This application provides a method for generating a shared key at the sending end, a device for generating a shared key at the sending end, and a terminal device for generating a shared key at the sending end, and a terminal device for generating a shared key at the receiving end. A method for generating a shared key at a receiving end, a device for generating a shared key at a receiving end, a terminal device for generating a shared key at a receiving end, and a system for generating a shared key, which are co...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D Engineer
- R&D Manager
- IP Professional
- Industry Leading Data Capabilities
- Powerful AI technology
- Patent DNA Extraction
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2024 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com