Remote authentication protocol method based on password and intelligent card
A remote authentication, smart card technology, applied in the field of information security, can solve the problems of user tracking, failure to protect user anonymity, loss of smart card revocation function, etc.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0052] The present invention will be further described in detail with reference to the accompanying drawings and embodiments.
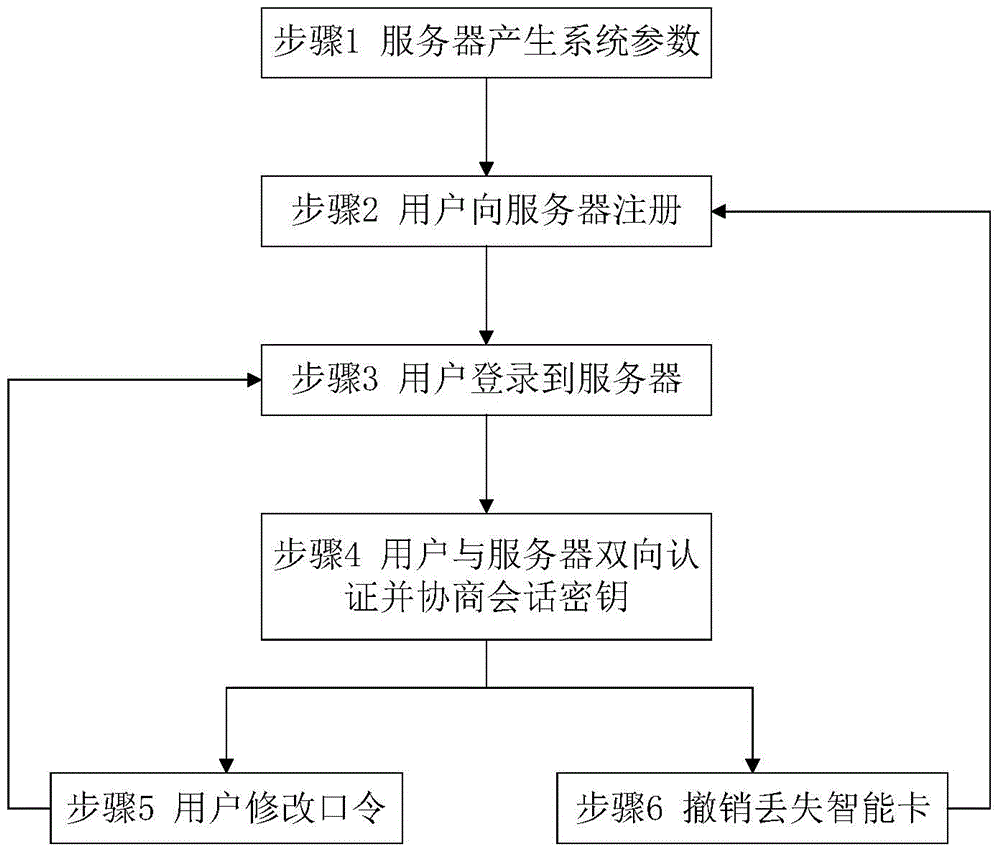
[0053] The security and efficiency of this protocol are mainly reflected in optimizing the elliptic curve point product algorithm in the design, and embedding authentication codes and counting groups in appropriate nodes, which can be specifically applied in online banking and other systems, such as figure 1 The specific operation shown is as follows:
[0054] (1) Initialization phase
[0055] At this stage, server S will generate system parameters through the following steps.
[0056] 1) S selects the elliptic curve E:y 2 ≡x 3 +ux+v (modp), E p (u, v) is the nth-order point addition group of the elliptic curve E, and P is its generator, that is, n·P=O.
[0057] 2) S selection As your own private key and save it, calculate Y=s·P as the public key, and then choose a one-way hash function
[0058] 3) S keeps s secret, and announces its system ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com