Method and system for intercepting, encrypting and decrypting data
A data interception, encryption and decryption technology, which is applied in the fields of data interception, encryption and decryption and systems, can solve problems such as being difficult to rest assured, and achieve the effect of strong security
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
no. 1 example
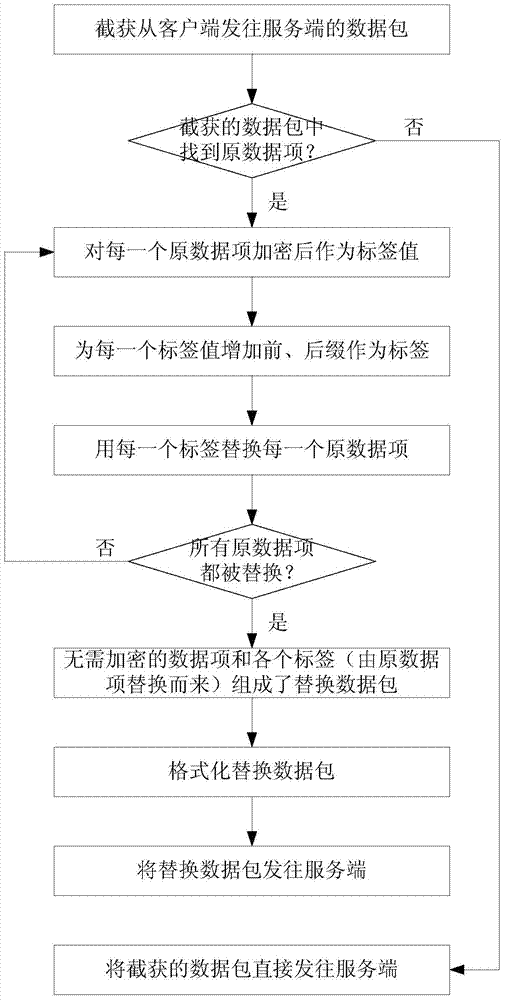
[0038] See figure 1 , The first embodiment of the method for intercepting and encrypting uplink data of this application includes the following steps:
[0039] Step a1, intercept the data packet sent from the client to the server;
[0040] Step a2, find the data item that needs to be encrypted from the intercepted data packet, that is, the original data item; if no original data item is found, send the intercepted data packet directly to the server; if one or more original data are found Item, go to step a3;
[0041] Step a3, for each original data item, encrypt the original data item as a label value; add prefix and suffix before and after each label value to form a label; replace each original data with each label item;
[0042] The intercepted data packet usually consists of two parts: the data item that needs to be encrypted (original data item) and the data item that does not need to be encrypted; after all the original data items in the intercepted data packet are replaced with...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com