Protecting method and protecting system for authentication server software copyright
An authentication server, copyright protection technology, applied in transmission systems, instruments, electrical components, etc., can solve problems such as troublesome license upgrades, and achieve the effect of protecting intellectual property rights and simple maintenance
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
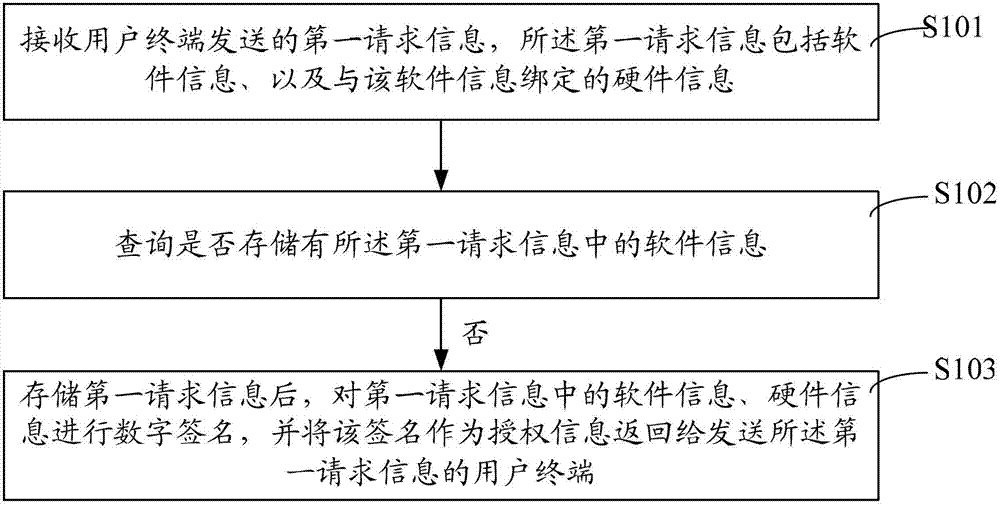
[0019] see figure 1 As shown, it is a schematic flowchart of a method for protecting software copyright of an authentication server according to an embodiment of the present invention, as shown in FIG. figure 1 As shown, the authentication server software copyright protection method in this embodiment includes requesting authorization, and the requesting authorization includes the following steps:
[0020] Step S101: Receive the first request information sent by the user terminal, where the first request information includes software information and hardware information bound to the software information, and enter step S102, wherein the authentication server is for the Internet terminal and network access The device provides access to the authentication server. The main functions include user authentication, user service authorization, user information management, etc. The first request information is generally transmitted through the network, and the software information in t...
Embodiment 2
[0036] According to the authentication server software copyright protection method of the present invention, the present invention also provides an authentication server software copyright protection system. figure 2 A schematic structural diagram of an authentication server software copyright protection system according to an embodiment of the present invention is shown in , including a copyright management server 201 and a database 202, wherein:
[0037] The copyright management server 201 is configured to receive first request information sent by a user terminal, where the first request information includes software information and hardware information bound to the software information, and is used to query whether the first request information is stored in the database If the software information in the request information is not stored, then after the first request information is stored in the database, digitally sign the software information and hardware information in t...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - Generate Ideas
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com