Monitoring method and monitoring device on basis of service operation
A business operation and business model technology, applied in the field of data security, can solve problems such as the inability to find logical anomalies and the inability to intuitively represent business logic relationships
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0044] It should be understood that the specific embodiments described here are only used to explain the present invention, not to limit the present invention.
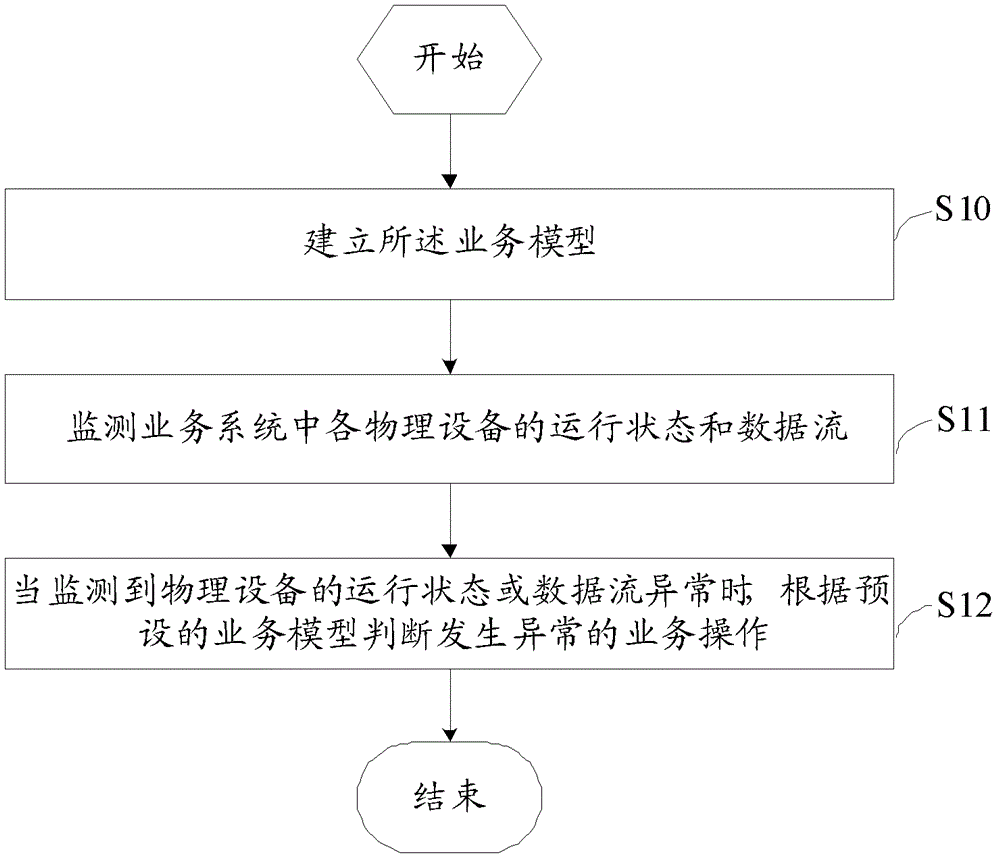
[0045] refer to figure 2 , propose an embodiment of a method for monitoring based on business operation of the present invention, comprising steps:
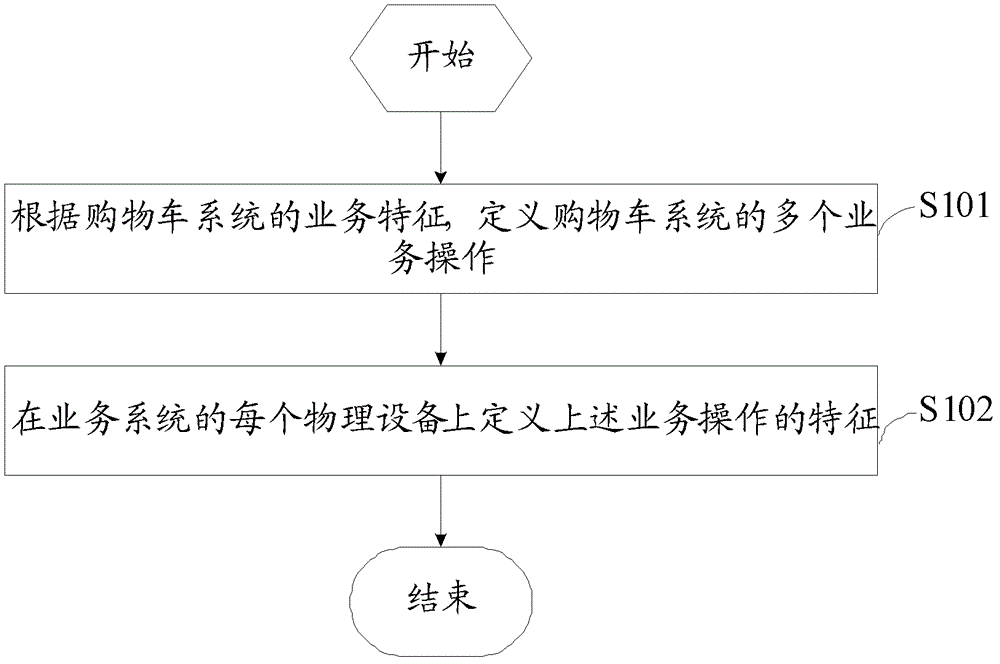
[0046] S10. Establish the business model;
[0047] In this embodiment, the monitoring of the application performance of the business system not only monitors the status of each physical device in the business system, but also models the business logic process, generates a business model, that is, a business logic topology, and intuitively feeds back the operation of the entire IT resource in business operations. The running status of the process, and when an abnormality occurs in a certain business operation, it can also intuitively show the running status of the logical process of the business operation.
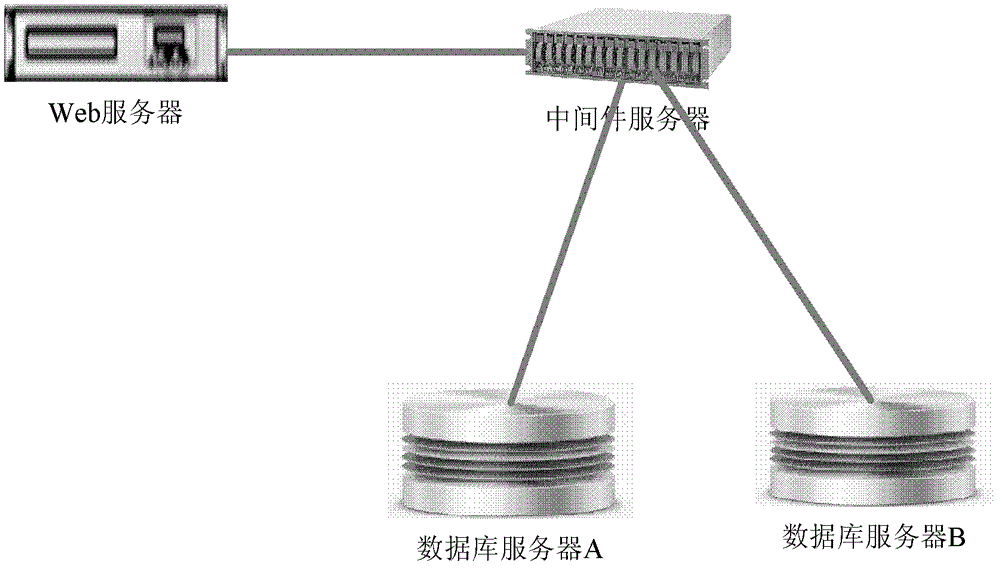
[0048] First, a business model is established. For the conven...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D Engineer
- R&D Manager
- IP Professional
- Industry Leading Data Capabilities
- Powerful AI technology
- Patent DNA Extraction
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2024 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com