An information security comprehensive audit system and method
An information security and remote desktop technology, applied in the field of security access, can solve the problems of audit engine occupying system resources, huge workload caused by deployment, and normal operation of server-side computer systems, so as to simplify deployment tasks and avoid system resources. Effect
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
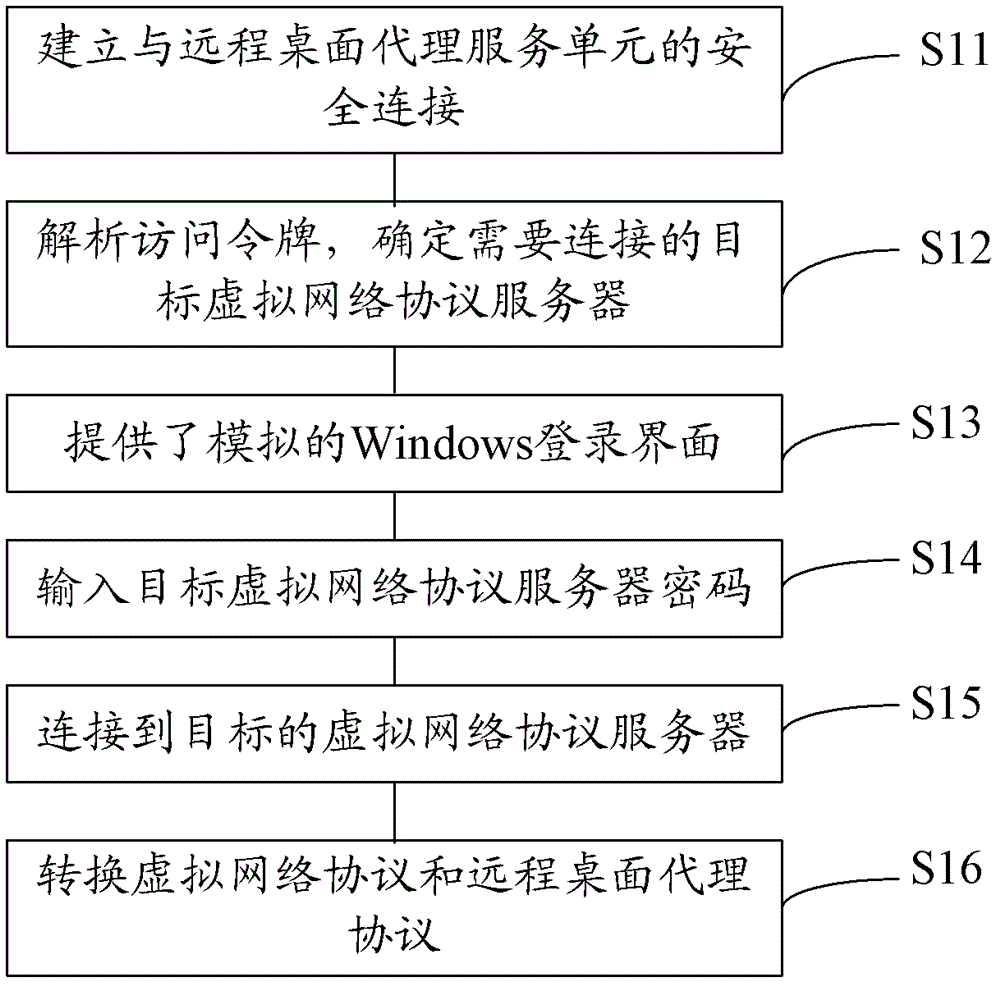
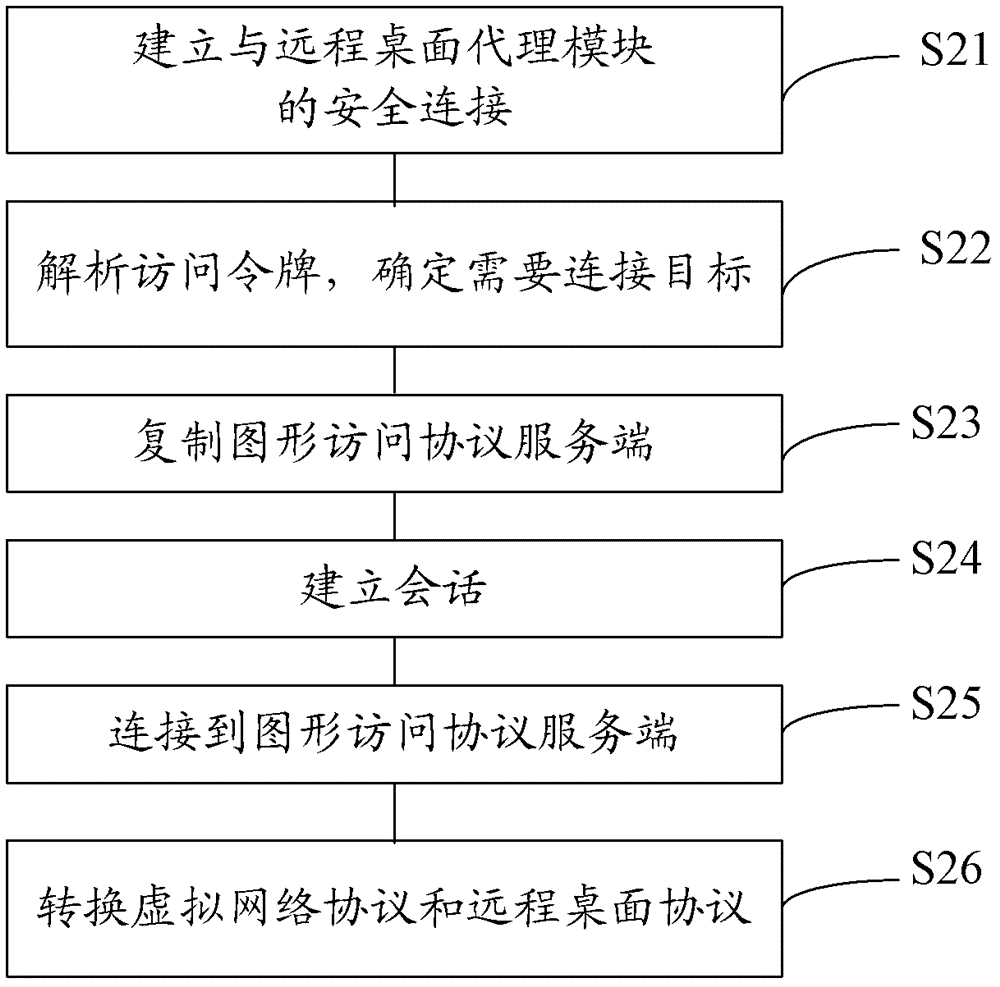
[0044] The following will clearly and completely describe the technical solutions in the embodiments of the present invention with reference to the accompanying drawings in the embodiments of the present invention. Obviously, the described embodiments are only some, not all, embodiments of the present invention. Based on the embodiments of the present invention, all other embodiments obtained by persons of ordinary skill in the art without making creative efforts belong to the protection scope of the present invention.
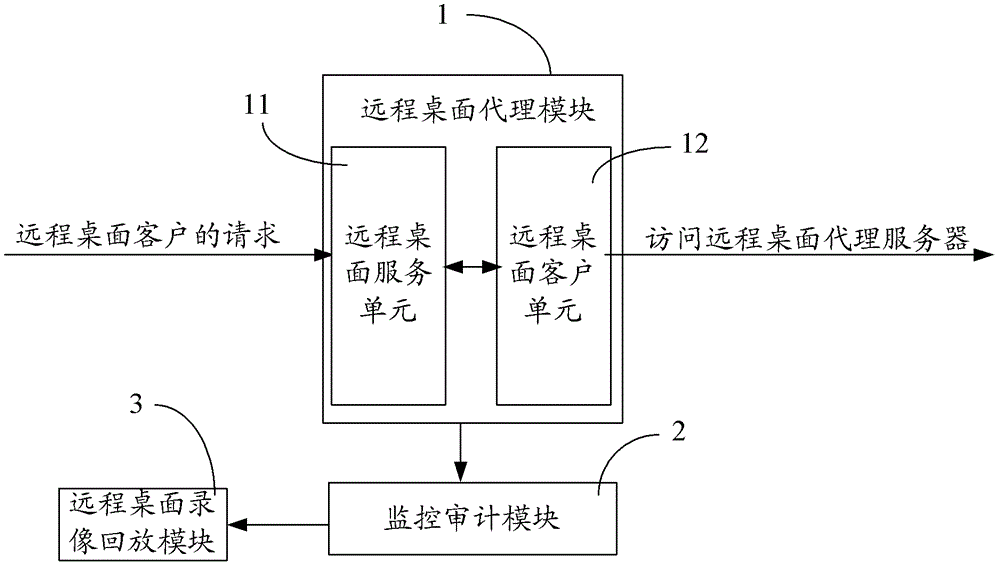
[0045] In order to reduce the workload during deployment and avoid the resource occupation of the server-side computer, the embodiment of the present invention provides an information security comprehensive audit system, such as figure 1 shown, including:
[0046] The remote desktop proxy module 1 is used to receive the request from the remote desktop proxy client, after the remote desktop proxy request is authenticated, realize the data exchange between the r...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com