Network flow recovery method
A network traffic and traffic technology, applied in the Internet field, can solve the problems of restoration bottlenecks, invisible real-time traffic collection of transmitted data, etc.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
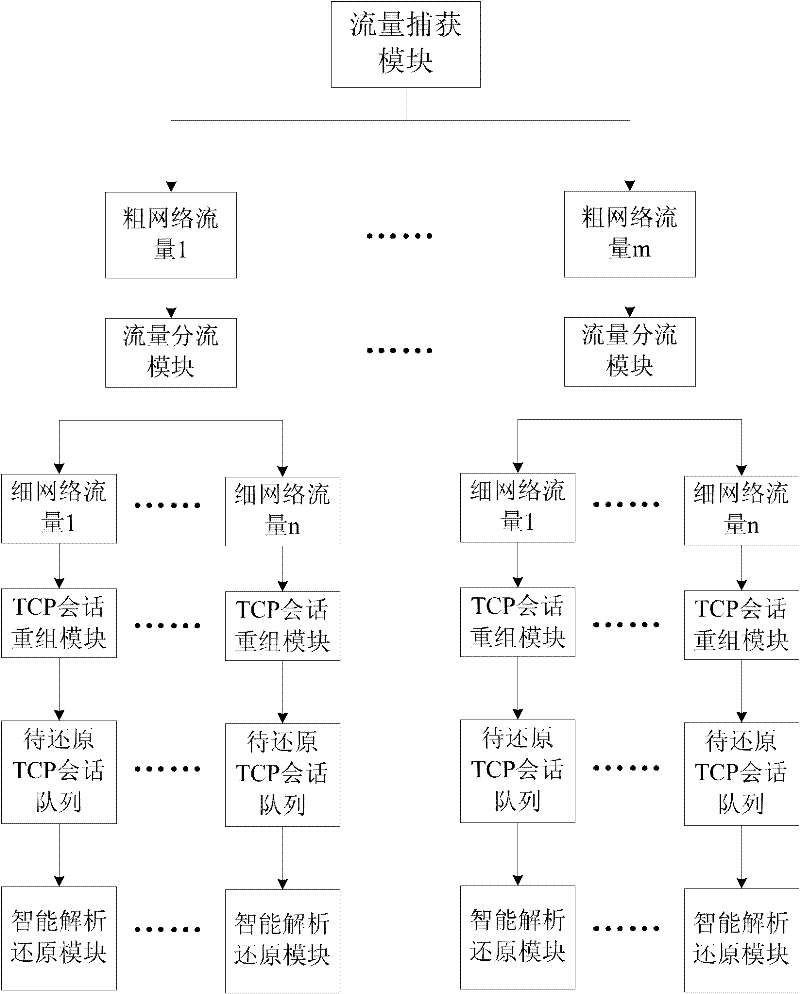
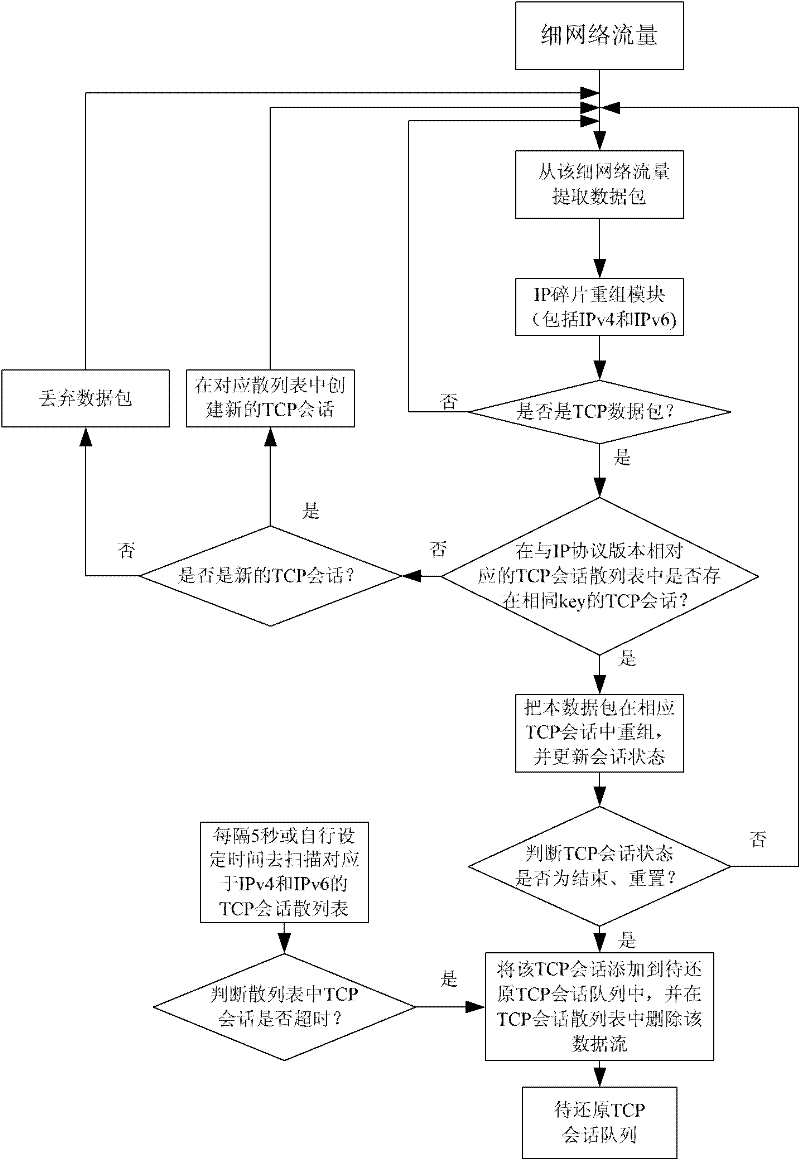
[0040] see figure 1 , is the overall process of the present invention.
[0041] First, use the traffic capture module to intercept the original data packets from the backbone network and perform protocol filtering and distribution. Since the experimental server CPU is a quad-core processor, the number of coarse (network) traffic is set to 4, then at this time figure 1 The rough (network) flow number m in is 4. First filter the original network traffic to extract IP data packets (including IPv4 and IPv6 data packets), and then use the hash algorithm to realize the distribution of the extracted IP data packets. This algorithm uses the source MAC (SMAC) and destination MAC (DMAC) in the IP data packets ) to perform an XOR operation, and then use the result of the operation result as a hash value. The specific XOR operation is to split the source (destination) MAC into 3 values of 16 bits (2 bytes), and then put The 16-bit values (units) are sequentially subjected to XOR ope...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - Generate Ideas
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com