User bound portable trusted mobile device
A mobile device and portable technology, applied in computer security devices, user identity/authority verification, instruments, etc., can solve the problems of complex key migration and authorization, inconvenient use of TPM, etc.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
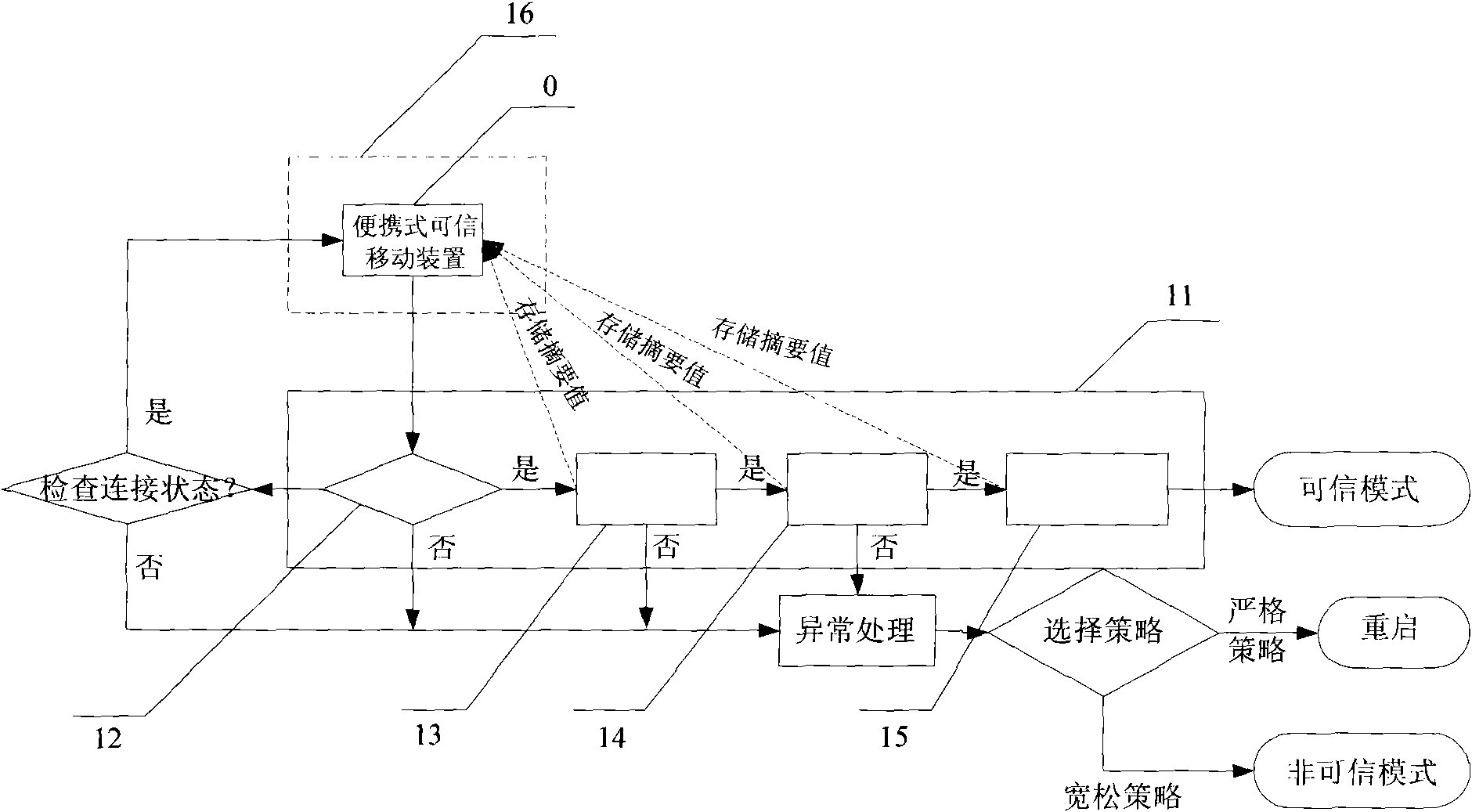
[0047] Below in conjunction with accompanying drawing and embodiment the present invention is described in detail:
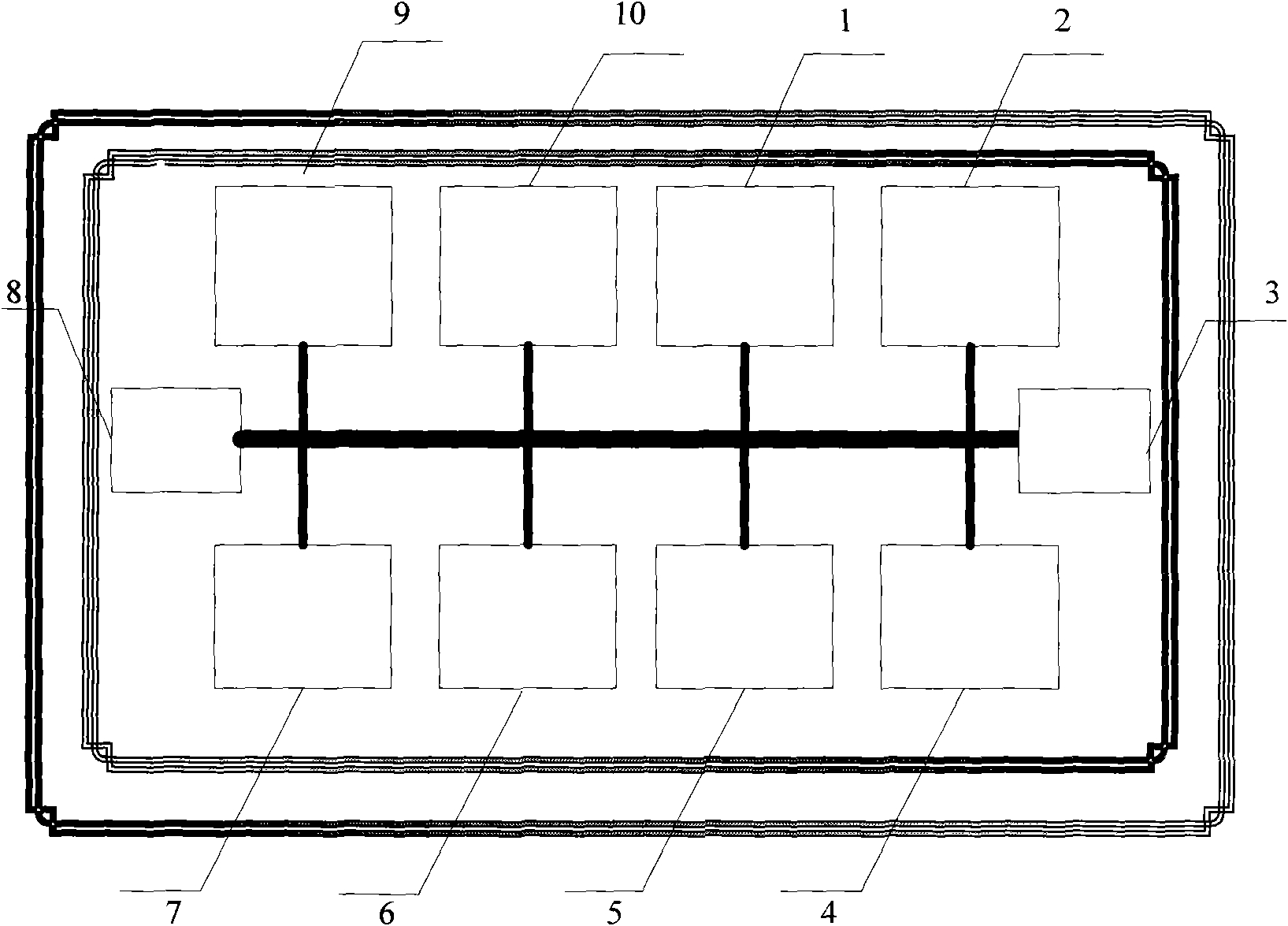
[0048] figure 1 It is a structural diagram of a portable trusted mobile device according to a specific embodiment of the present invention. Such as figure 1 As shown, the portable trusted mobile device includes the following components:
[0049] 1. On-chip service device for secure computing and management
[0050] The on-chip service device for secure computing and management establishes an independent computing and management environment, which is provided by a single-chip chip with security protection capabilities. According to an embodiment of the present invention, the single-chip chip preferably adopts, for example, ZTE integrated Z32U chip. It should be clear to those skilled in the art that the single-chip chip with security protection capability is not limited to this kind of chip.
[0051] Such as figure 1 As shown, the on-chip service device for...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D Engineer
- R&D Manager
- IP Professional
- Industry Leading Data Capabilities
- Powerful AI technology
- Patent DNA Extraction
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2024 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com