E-mail enciphered transmission method
An encrypted transmission and e-mail technology, which is applied in the field of e-mail encrypted transmission, can solve the problems of inconvenient use and achieve the effect of improving security, simple and easy method, and meeting the needs of encrypted e-mail transmission
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
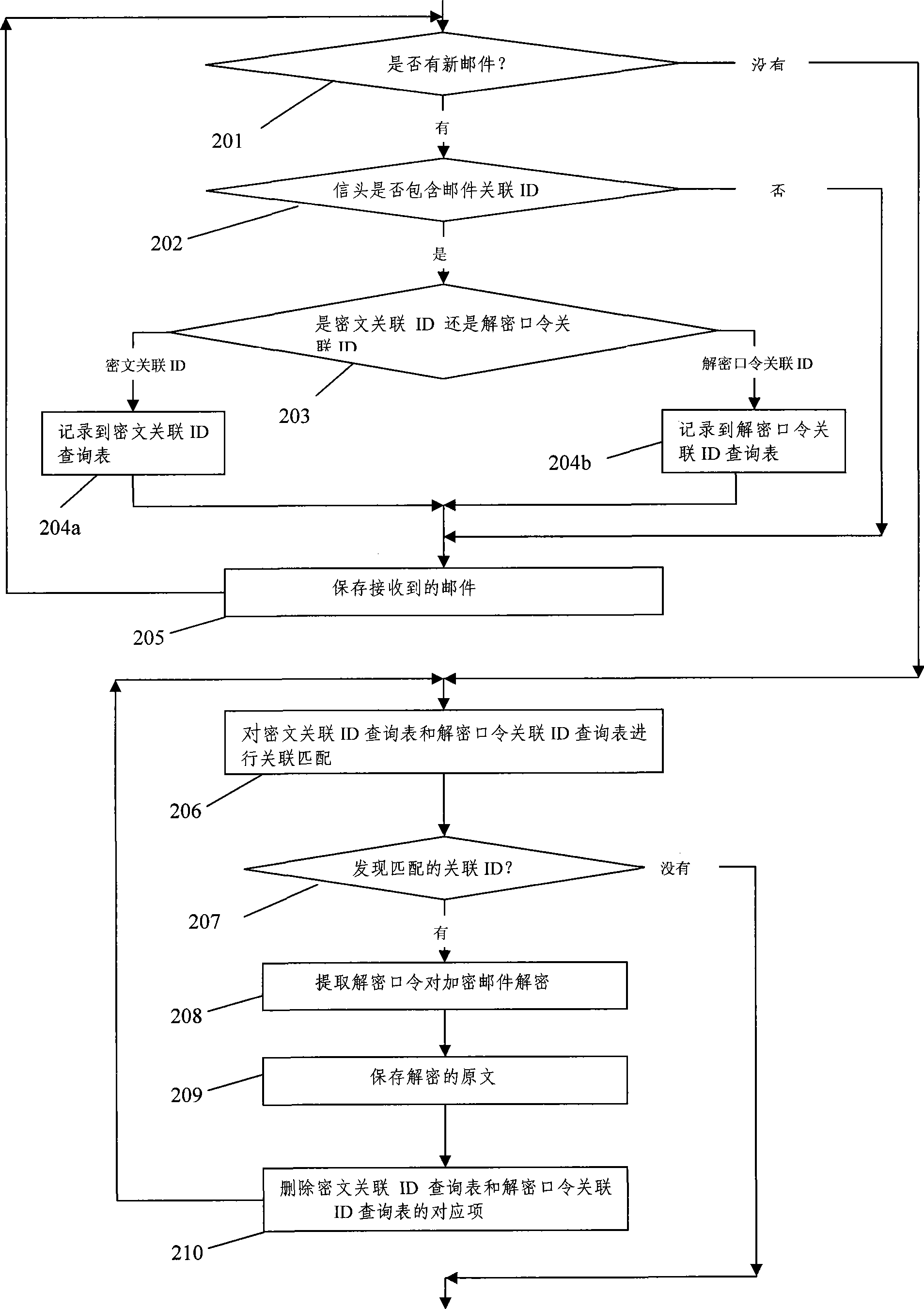
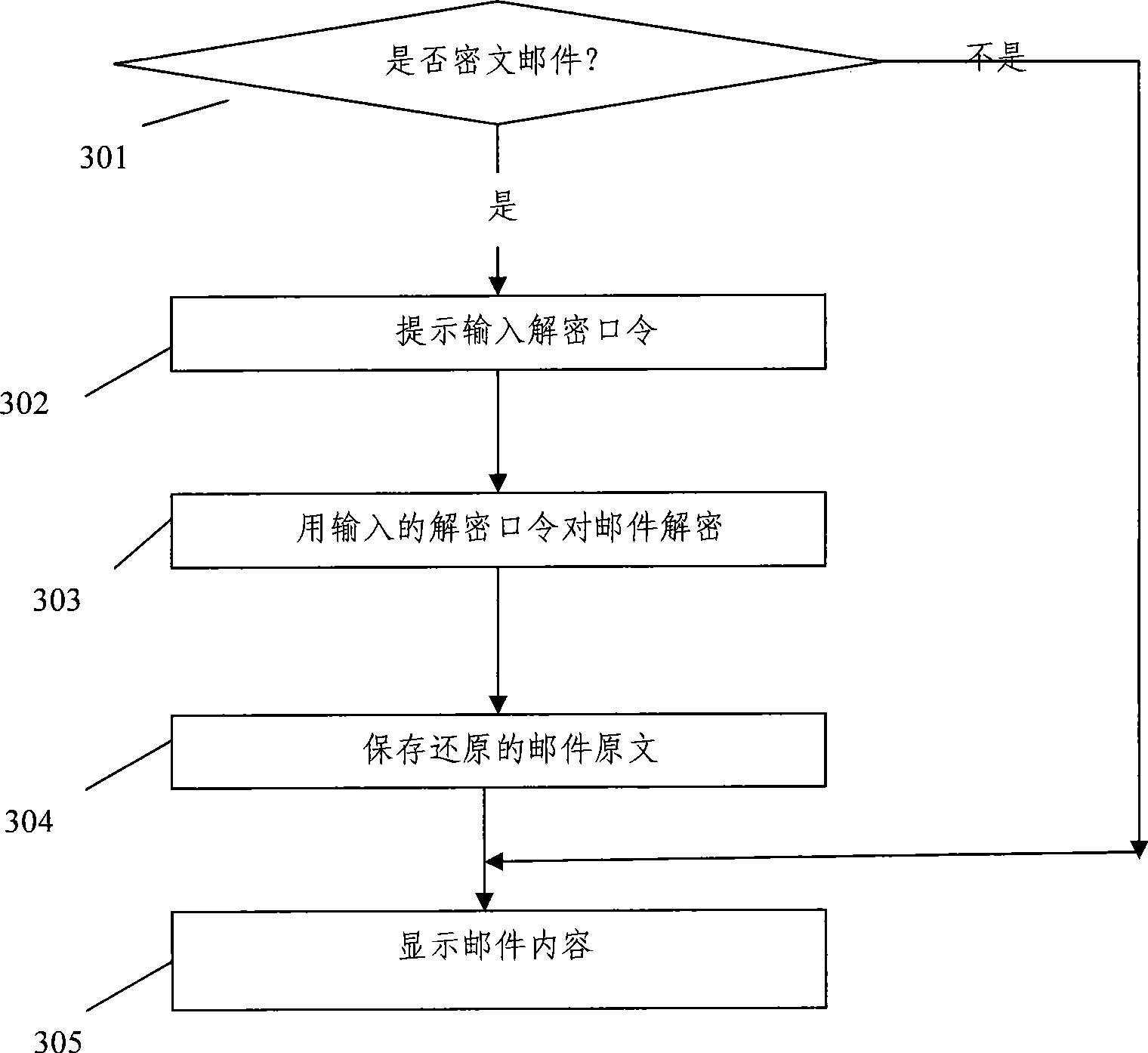
[0026] The present invention will be described in further detail below in conjunction with the accompanying drawings.
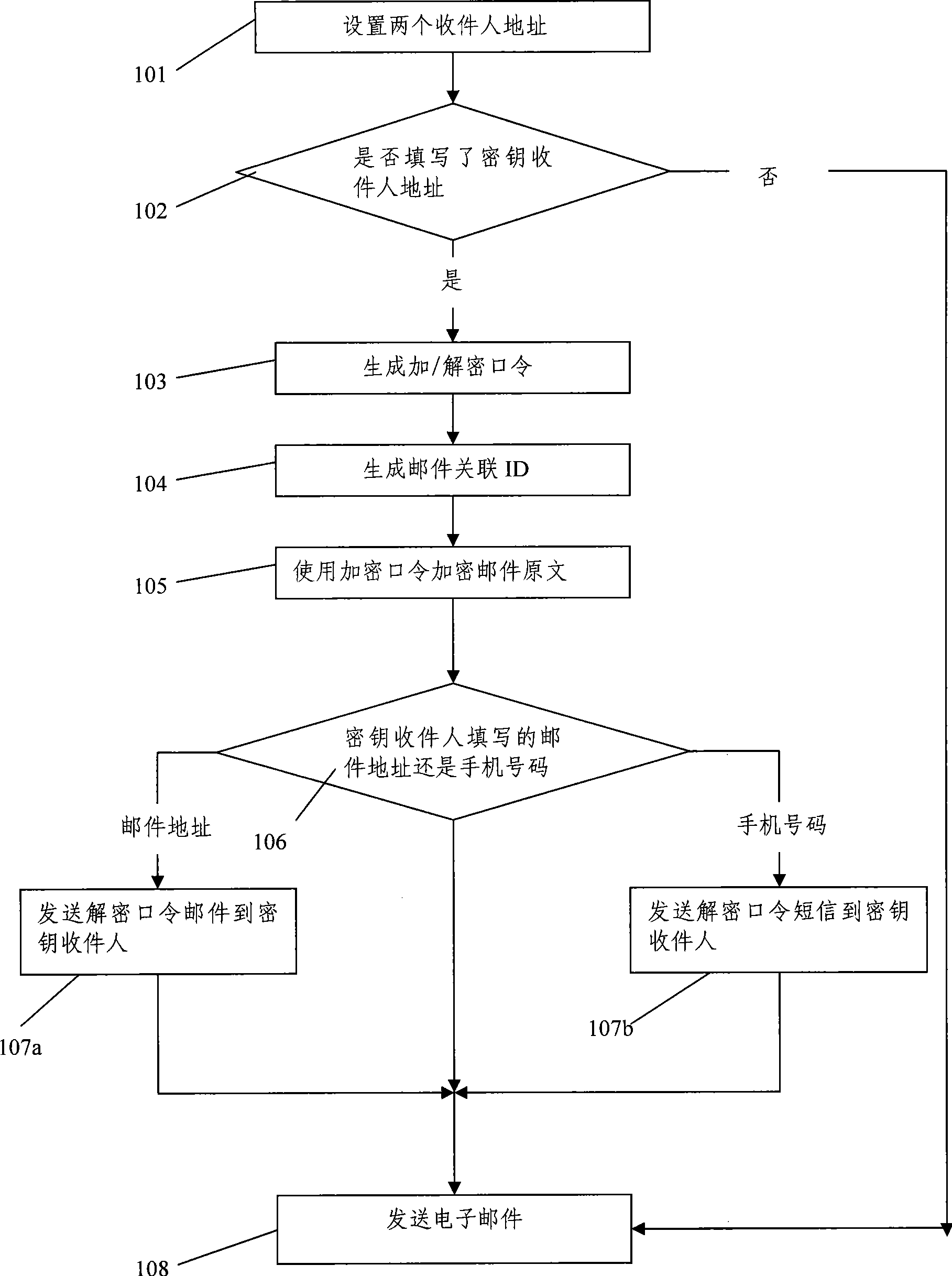
[0027] The email encrypted transmission method of the present invention specifically includes the email sending process, receiving process and reading process. Such as figure 1 As shown, the email sending process includes the following steps:
[0028] Step 101: Set the addresses of two recipients: one is the email recipient address, and the other is the key recipient address; here, the key recipient address can be an email address different from the mail recipient address, It can also be a mobile phone number.
[0029] Step 102: The email sending client judges whether the address of the key recipient is filled in, and if it is filled in, then go to step 103; if it is not filled in, send the original text of the email directly as sending an ordinary email, and then end the processing flow.
[0030] Step 103: the email sending client generates an encryption / ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com