Method for supporting access to closed network, UE, base station and readable storage medium
A base station and network technology, applied in the field of supporting access to closed networks, base stations and computer-readable storage media
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
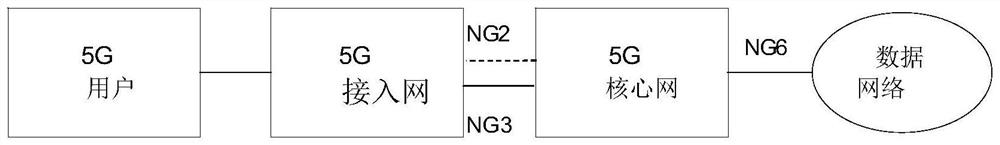
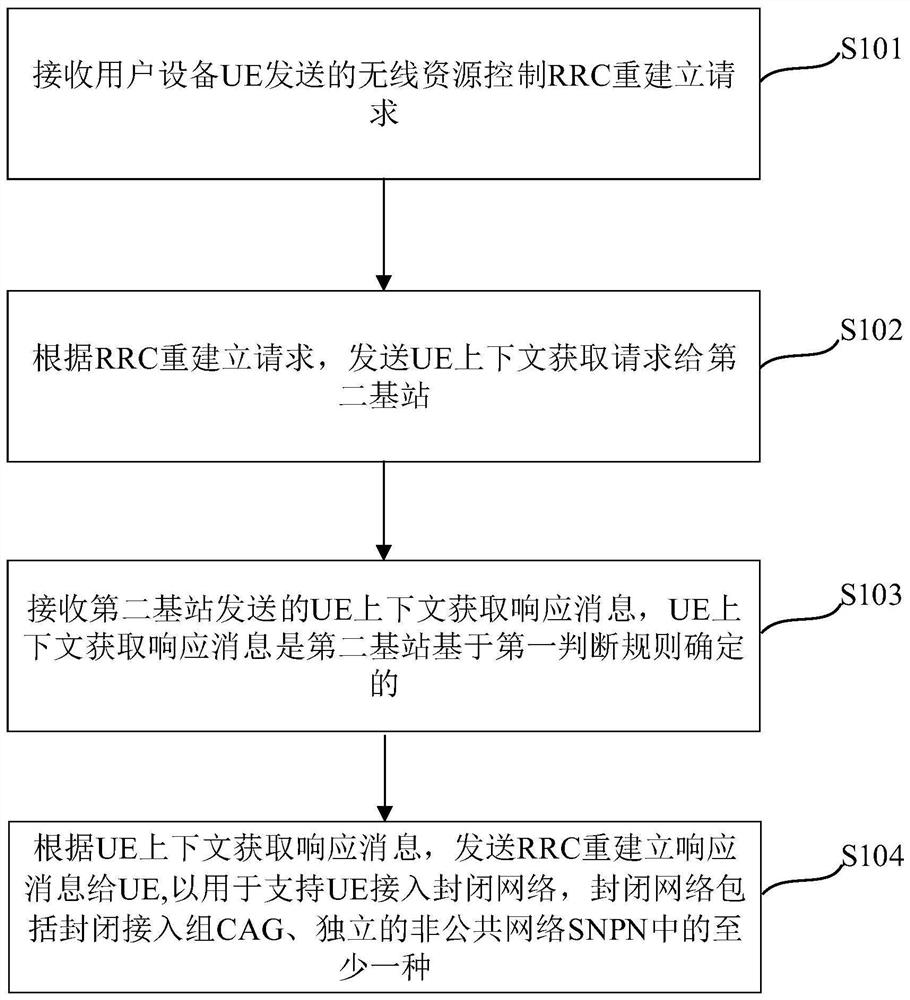
[0116] An embodiment of the present application provides a method for supporting access to a closed network, which is applied to the first base station. The schematic flow chart of the method is shown in image 3 As shown, the method includes:
[0117] Step S101, receiving a radio resource control RRC re-establishment request sent by a user equipment UE.
[0118] Step S102, sending a UE context acquisition request to the second base station according to the RRC re-establishment request.
[0119] Step S103, receiving a UE context acquisition response message sent by the second base station, where the UE context acquisition response message is determined by the second base station based on the first judgment rule.
[0120] Step S104, obtain a response message according to the UE context, and send an RRC re-establishment response message to the UE to support the UE to access a closed network, and the closed network includes at least one of a closed access group CAG and an indepe...
Embodiment 2
[0177] The method for supporting access to a closed network in the first embodiment of the present application is fully and detailedly introduced through the following embodiments:
[0178] Figure 9 It is a schematic diagram of the process of establishing an interface provided by the embodiment of this application. The base station is divided into a base station centralized control unit CU and a base station distribution unit DU. One DU is connected to multiple CUs, and one CU can be connected to multiple DUs. The base station can be a 5G base station, or an LTE base station, or a base station of other access modes. This embodiment takes a 5G base station as an example. If it is used in other systems, the corresponding interface and message name will also be changed accordingly. Such as Figure 9 Shown:
[0179] Step 901: DU sends F1 establishment request message to CU.
[0180] The F1 establishment request message contains information of a group of cells, the information...
Embodiment 3
[0305] Based on the same inventive concept as the foregoing embodiments 1 and 2, this embodiment of the present application also provides a first base station. The schematic structural diagram of the device is as follows Figure 15 As shown, the first base station 150 includes a first processing module 1501 , a second processing module 1502 , a third processing module 1503 and a fourth processing module 1504 .
[0306] The first processing module 1501 is configured to receive a radio resource control RRC re-establishment request sent by the user equipment UE;
[0307] The second processing module 1502 is configured to send a UE context acquisition request to the second base station according to the RRC re-establishment request;
[0308] The third processing module 1503 is configured to receive a UE context acquisition response message sent by the second base station, where the UE context acquisition response message is determined by the second base station based on the first j...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com