Port scanning method and device
A port scanning, port technology, applied in the network field
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
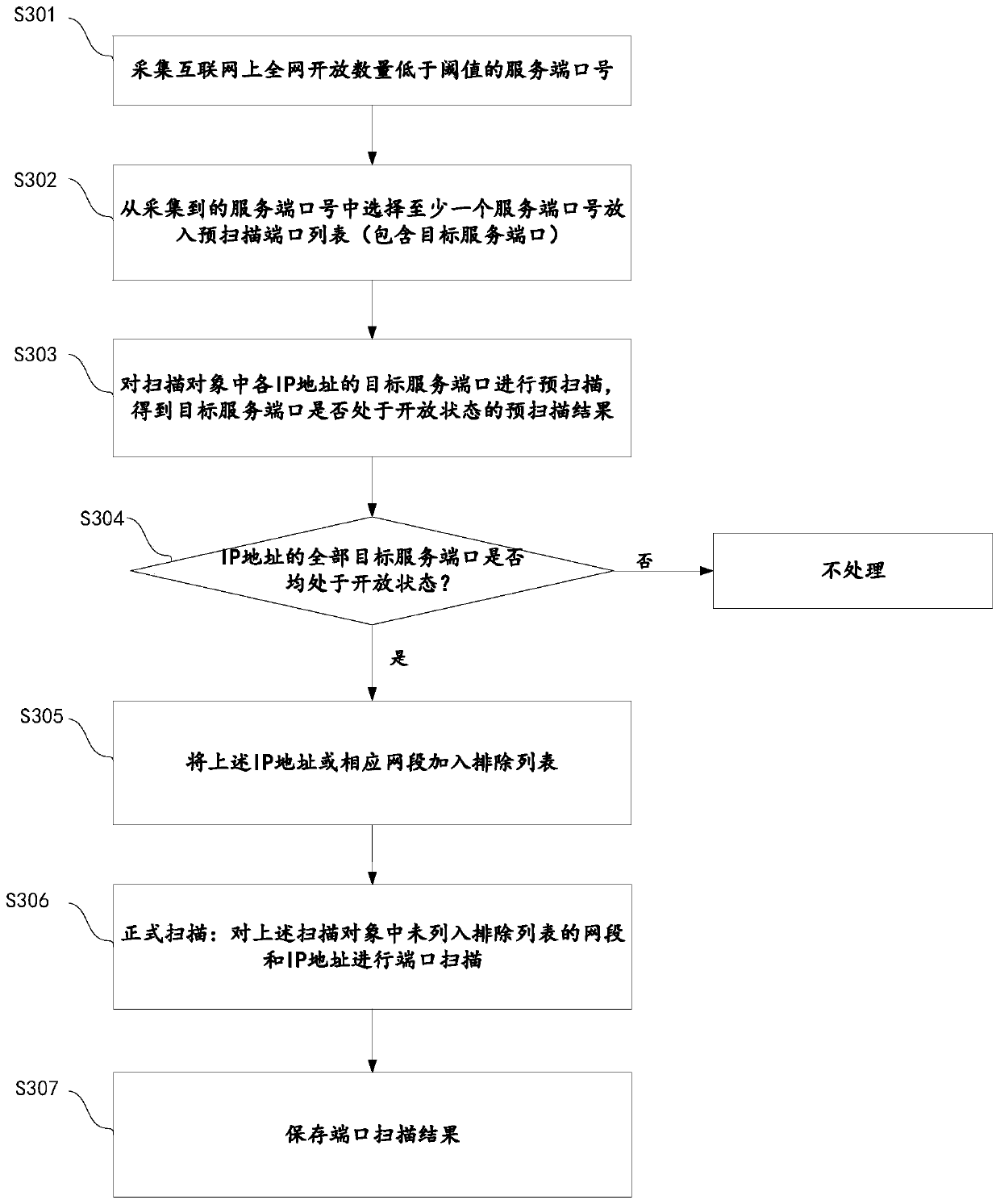
[0037] For reference and clarity, technical terms, abbreviations or abbreviations used hereinafter are summarized as follows:
[0038] Nmap: Network Mapper, Nmap was originally a network scanning and sniffing toolkit under Linux;
[0039] TCP / IP: Transmission Control Protocol / Internet Protocol, Transmission Control Protocol / Internet Protocol;
[0040] SYN: Synchronize Sequence Numbers, synchronization sequence number, SYN is the handshake signal used when TCP / IP establishes a connection;
[0041] ACK: Acknowledgment, confirmation character. In data communication, a transmission-type control character sent by the receiver to the sender, indicating that the sent data has been confirmed to be received correctly;
[0042] Nginx: engine x. Nginx is a high-performance HTTP and reverse proxy web server, and also provides IMAP / POP3 / SMTP services;
[0043] Vulnerability scanning: Vulnerability scanning refers to a security detection (penetration attack) behavior that detects the se...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - Generate Ideas
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com