Personalized position privacy protection method based on position k-anonymization
A privacy protection and privacy technology, applied in the privacy protection field of network information security, can solve the problems of inability to achieve k-anonymity, vulnerable to reverse attacks, etc., achieve powerful computing and storage capabilities, improve security, and improve the effect of service quality
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment
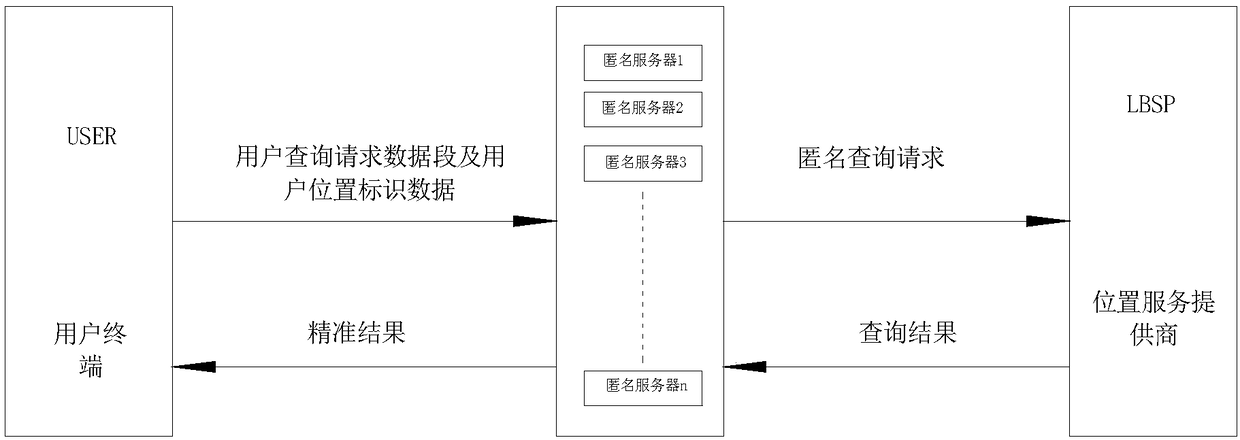
[0041] The present invention adopts a system framework of multiple anonymous servers to cooperate, solves the semi-trusted problem of third-party anonymous servers, realizes the security protection of user location privacy and improves service quality, and uses the specific implementation method to describe the specific process of the present invention in detail below.
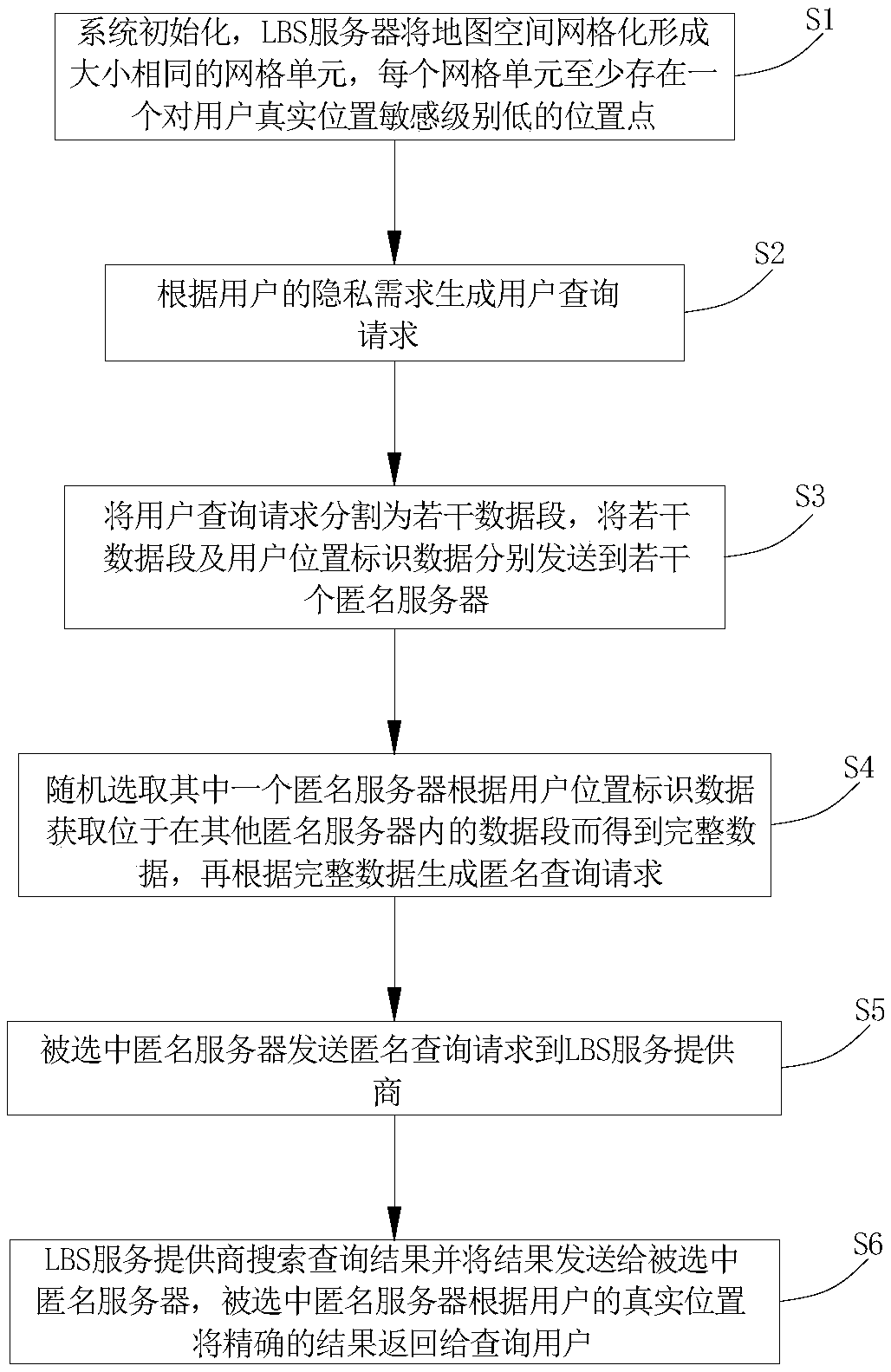
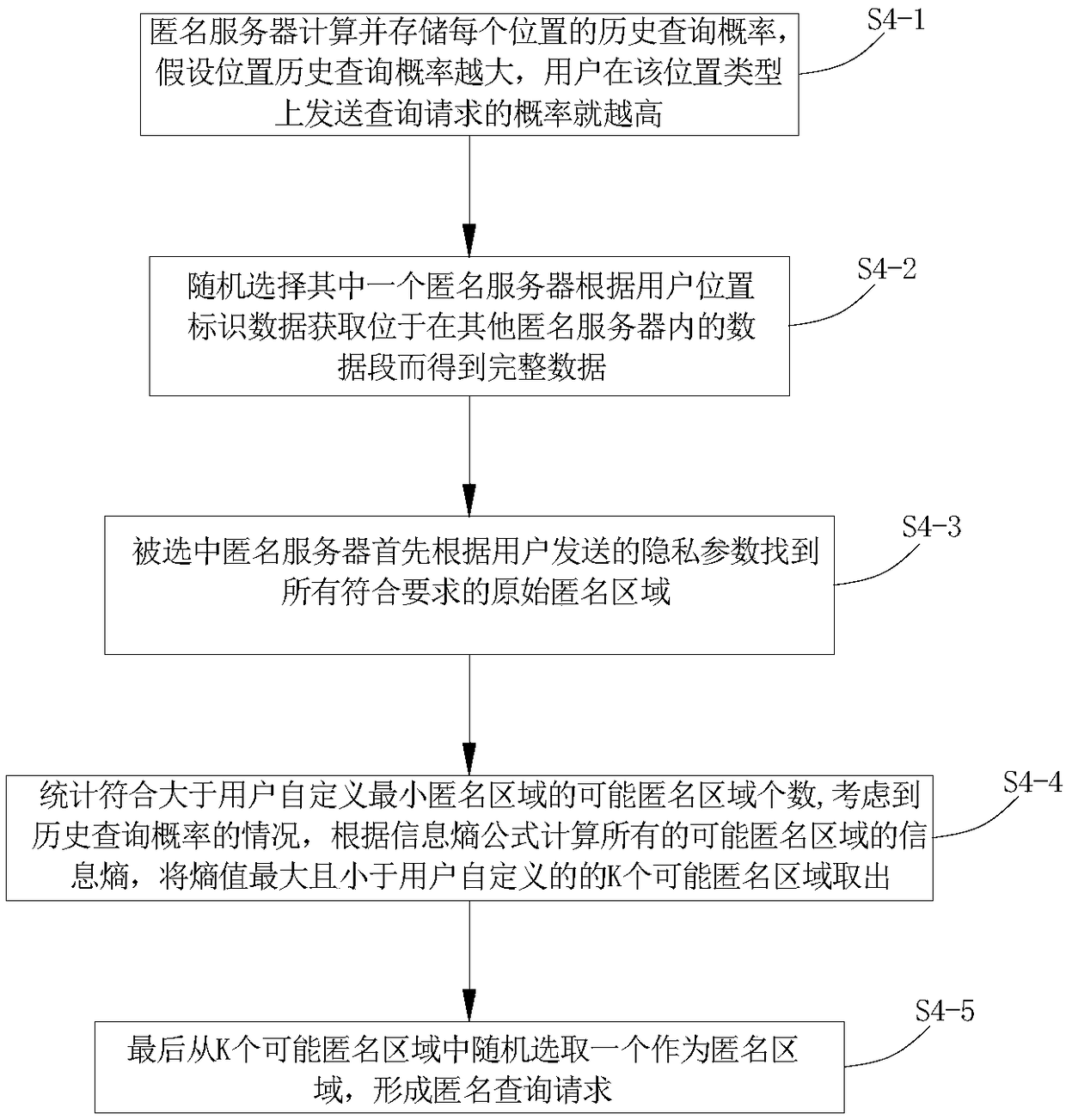
[0042] Please refer to figure 1 and figure 2 , a personalized location privacy protection method based on location k-anonymity, including the following steps:
[0043]S1. System initialization. The LBS server grids the map space to form grid units of the same size. Each grid unit has at least one location point that is less sensitive to the user's real location.
[0044] S2. Generate a user query request Q according to the user's privacy requirements u ,
[0045] The specific process includes the following sub-steps:
[0046] S2-1. Query users First, generate the privacy requirements of the user's locatio...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D Engineer
- R&D Manager
- IP Professional
- Industry Leading Data Capabilities
- Powerful AI technology
- Patent DNA Extraction
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2024 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com