Fuzz testing-based industrial control system vulnerability mining method and apparatus, and vulnerability restoration method
An industrial control system and fuzzy testing technology, applied in computer security devices, instruments, electrical digital data processing, etc.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0028] The specific embodiments of the present invention will be further described below in conjunction with the accompanying drawings. It should be noted here that the descriptions of these embodiments are used to help understand the present invention, but are not intended to limit the present invention. In addition, the technical features involved in the various embodiments of the present invention described below may be combined with each other as long as they do not constitute a conflict with each other.
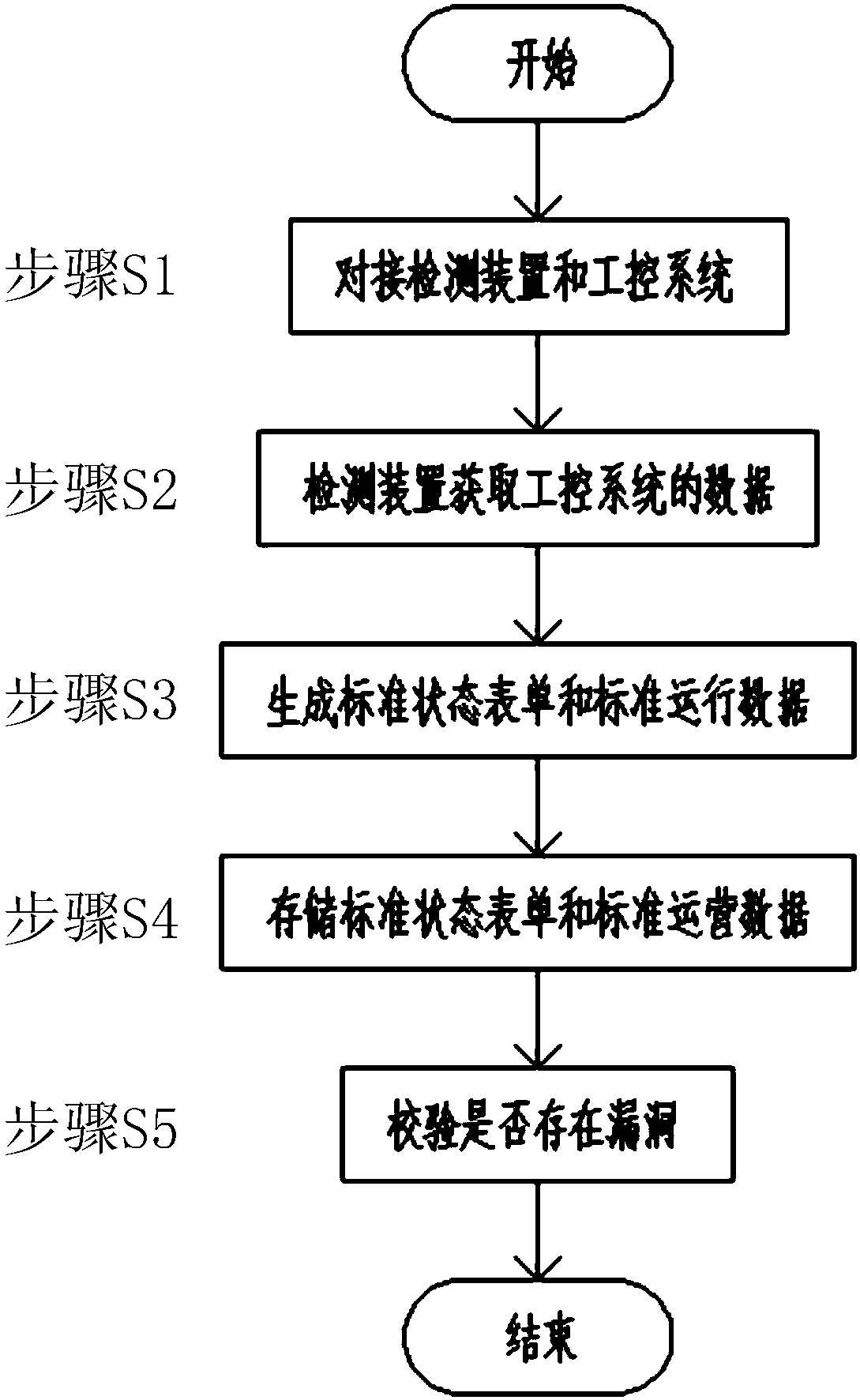
[0029] As the first embodiment of the present invention, a method for mining vulnerabilities in industrial control systems based on fuzz testing is proposed, such as figure 1 As shown, including: first after the industrial control system runs stably, the detection device is connected to the industrial control system (step S1). In this embodiment, a detection device with a data transmission interface is used, such as a PC host with detection software; the detection device...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D Engineer
- R&D Manager
- IP Professional
- Industry Leading Data Capabilities
- Powerful AI technology
- Patent DNA Extraction
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2024 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com