Method, client and server for authenticating webpage request
A web request and server technology, applied in the field of data security, can solve the problem of high client computing overhead
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0102] In order to make the above objects, features and advantages of the present application more obvious and comprehensible, the present application will be further described in detail below in conjunction with the accompanying drawings and specific implementation methods.
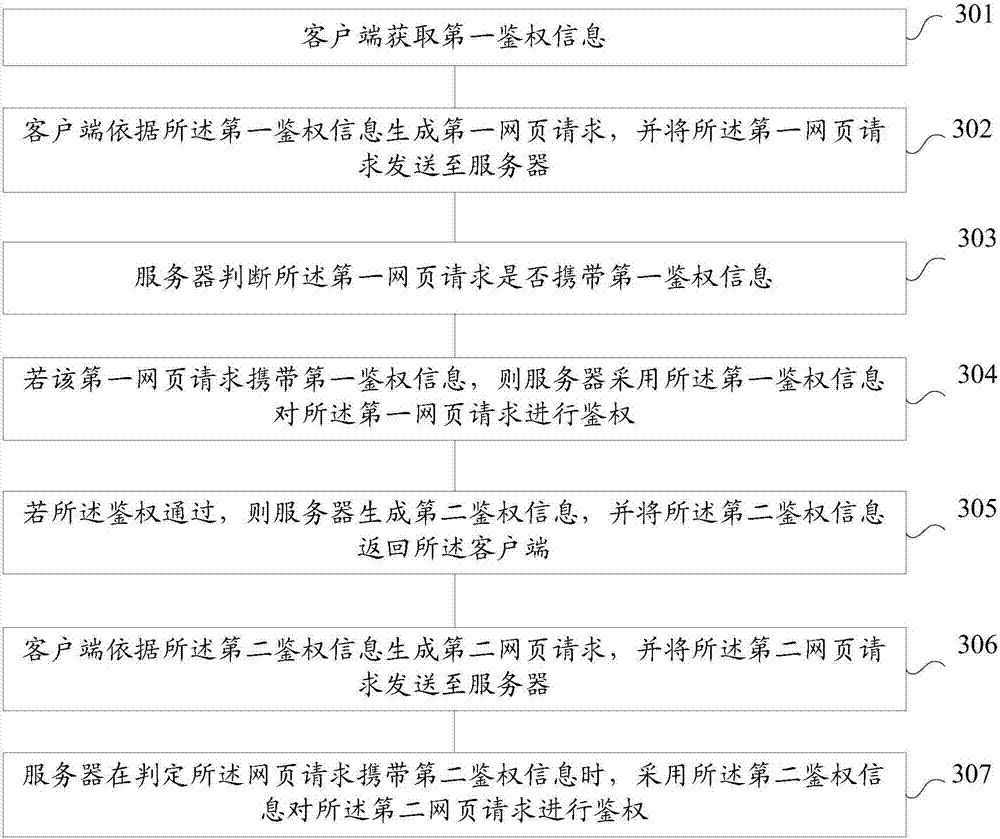
[0103] refer to figure 1 , which shows a flow chart of the steps of Embodiment 1 of a method for authenticating a web page request of the present application, the method may include the following steps:
[0104] Step 101, the server receives the web page request sent by the client;
[0105] In a specific implementation, the client and the server may communicate through an HTTP protocol (HTTP-Hypertext transfer protocol, hypertext transfer protocol).
[0106] The HTTP protocol defines how a browser (that is, a World Wide Web client process, client) requests a World Wide Web document from a World Wide Web server, and how the server transmits the document to the browser. From a hierarchical point of view,...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com