A centralized t‑box information security protection system
A technology for information security and protection systems, applied in transmission systems, digital transmission systems, electrical components, etc., can solve problems such as personal privacy risks and non-existent loophole detection
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0023] The present invention is further described below in conjunction with embodiment.
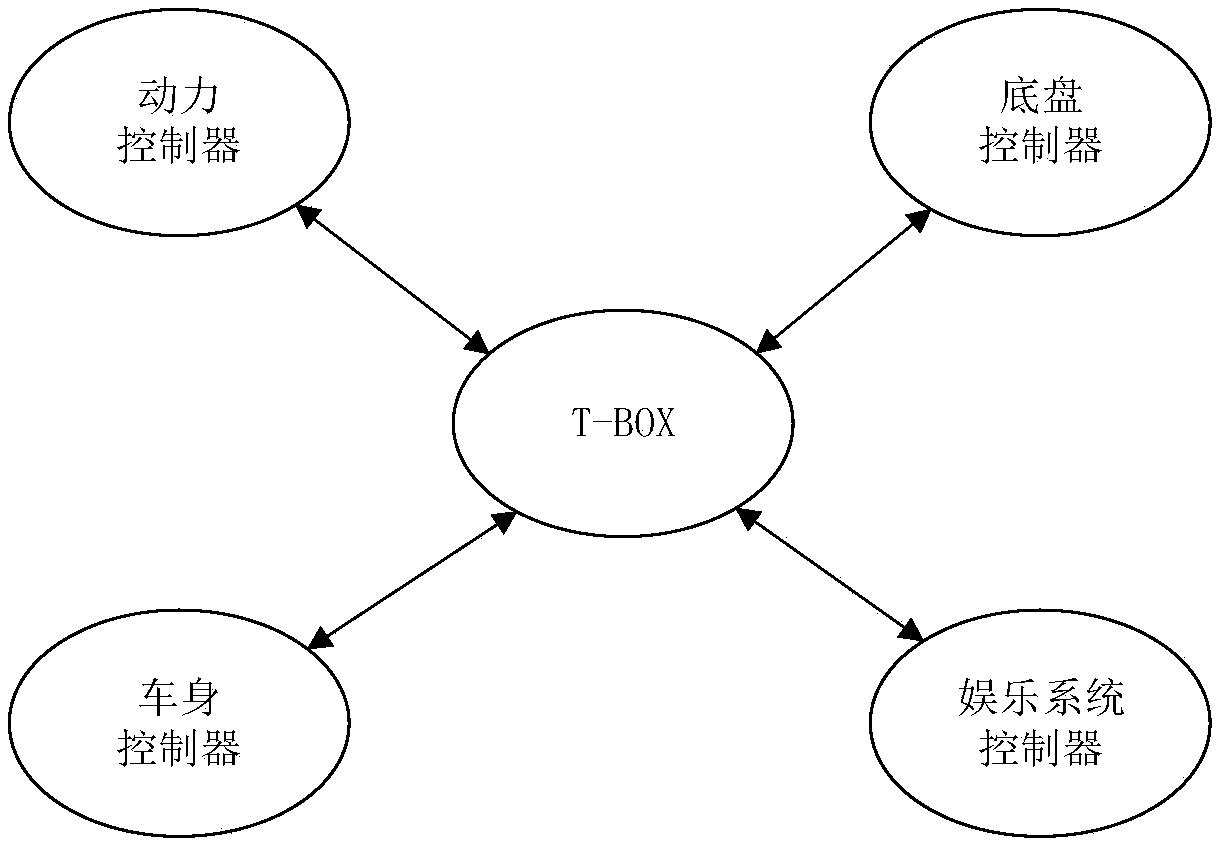
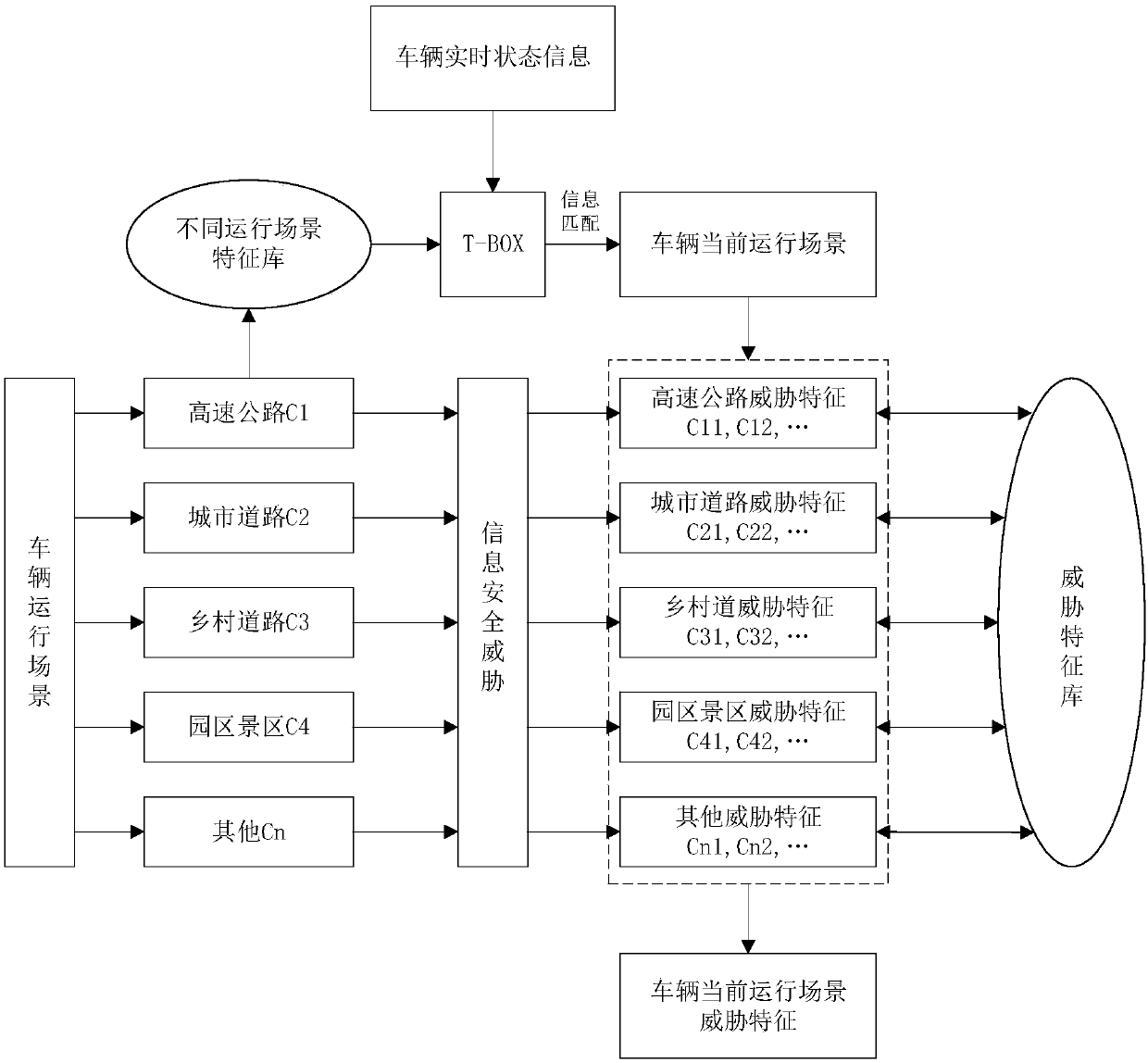
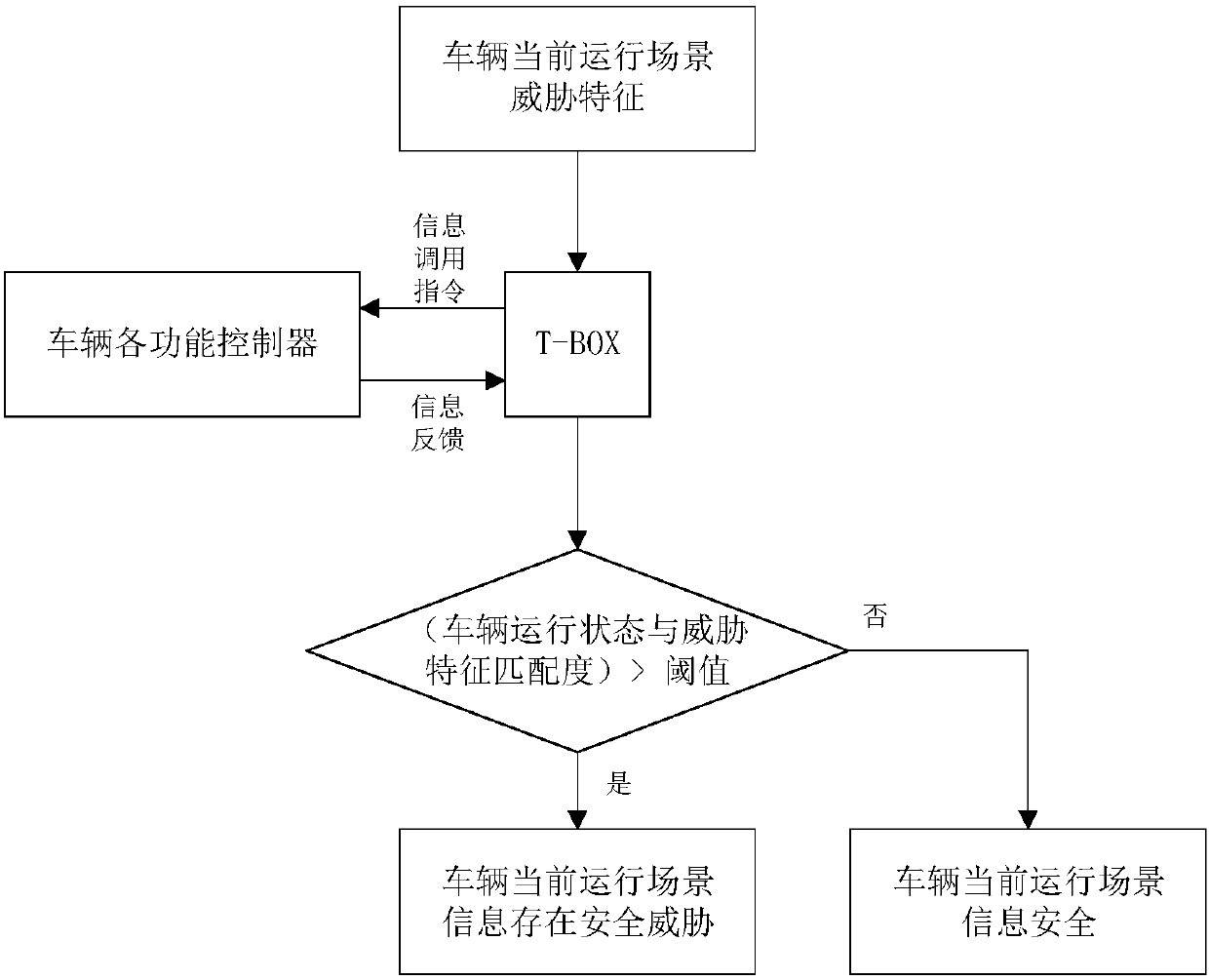
[0024] A centralized T-BOX information security protection system first establishes a centralized T-BOX information security protection architecture, such as figure 1 As shown, the architecture mainly includes T-BOX, power controller, chassis controller, body controller and entertainment system controller, among which T-BOX is responsible for the collection and management of all external transmission data of the vehicle, and through the information security protection system. The data of each functional domain is protected in real time. Then extract threat features for different operating scenarios of the vehicle, establish a threat feature library, and then determine the threat information encountered by the vehicle during operation through threat feature matching. Finally, based on the T-BOX centralized information security protection architecture, real-time and effective protection is...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D Engineer
- R&D Manager
- IP Professional
- Industry Leading Data Capabilities
- Powerful AI technology
- Patent DNA Extraction
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2024 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com