System and method for website attack defense verification
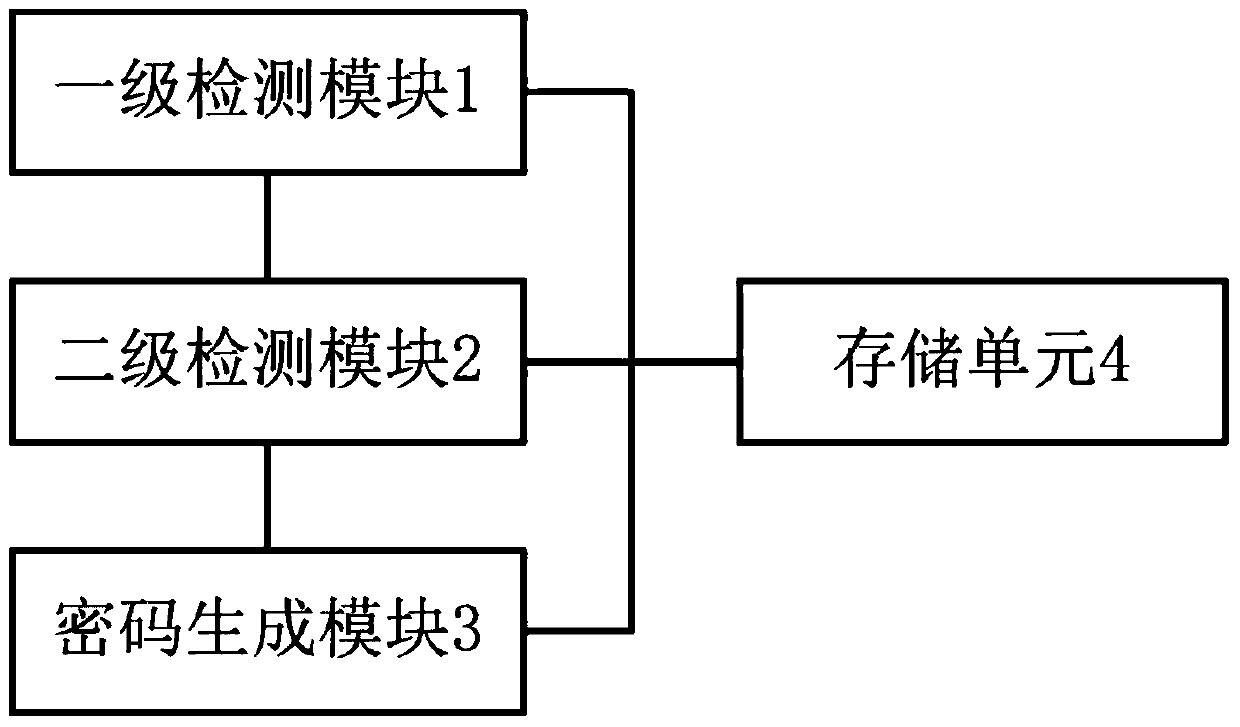
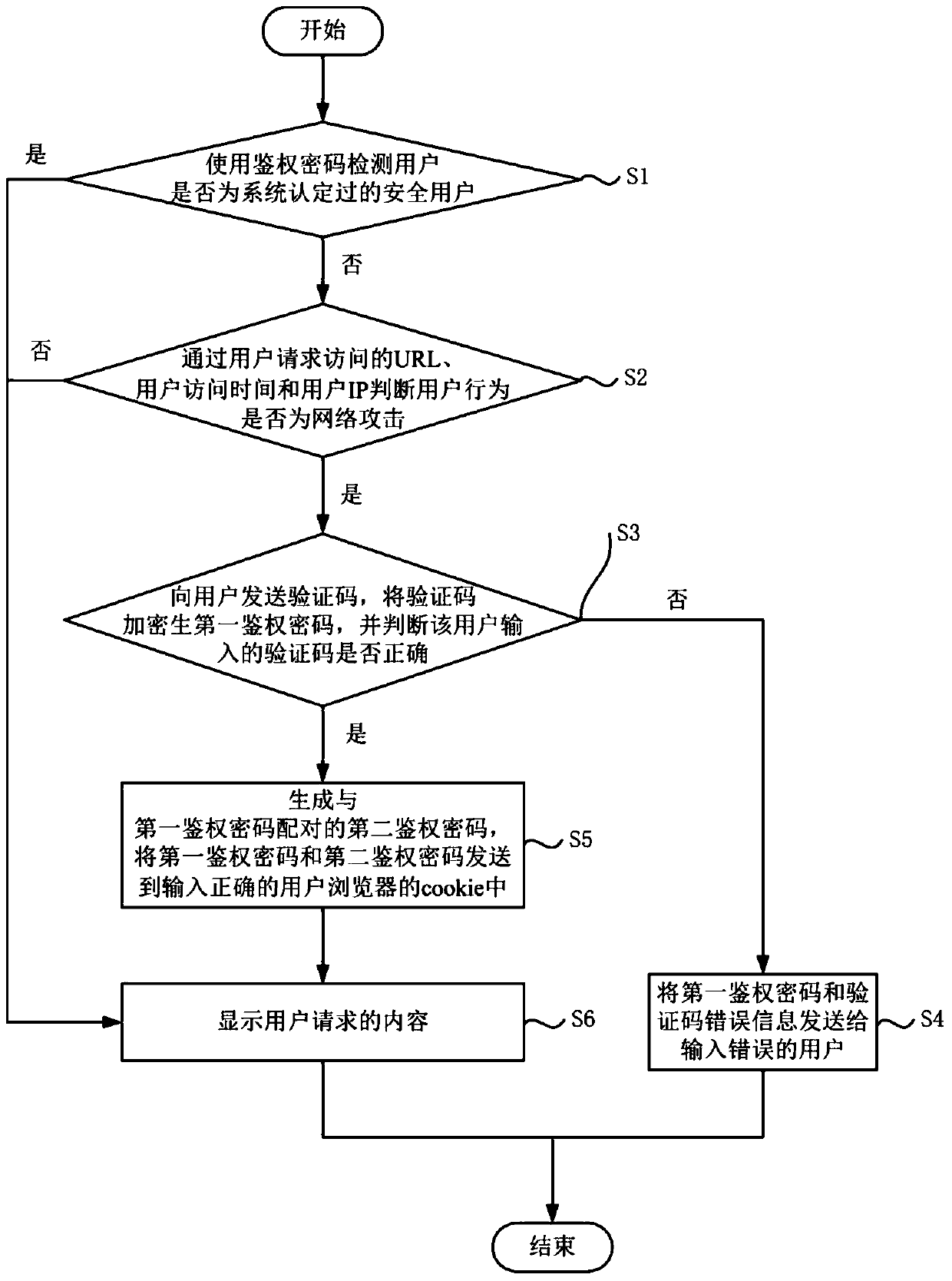
A verification system and verification method technology, applied in the field of website attack prevention verification system, to achieve high security, ensure safe operation, and prevent illegal requests and network attacks
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0033] Terminology Explanation:
[0034] Lua is a scripting language embedded in the server.
[0035] Nginx is a lightweight web server, reverse proxy server and email (IMAP / POP3) proxy server.
[0036] The verification code is a user identification picture for behavior verification.
[0037] TCP (Transmission Control Protocol Transmission Control Protocol).
[0038] MD5 (Message Digest Algorithm Fifth Edition) is a hash function widely used in the field of computer security to provide message integrity protection.
[0039] HMAC (Hash-based Message Authentication Code) is a key-related hash operation message authentication code. HMAC operation uses a hash algorithm, takes a key and a message as input, and generates a message digest as output.
[0040] HMACMD5 is a keyed hash algorithm constructed from the MD5 hash function and is used as a hash-based message authentication code. This HMAC process mixes a key with the message data, hashes the result of the mix using a hash ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com