Method and device for controlling traffic of encrypted data flow
A flow control and data flow technology, applied in the field of network communication, which can solve the problems of lack of versatility, inability to identify and analyze, and unsystematic identification methods.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0018] In order to make the purpose, technical solutions and advantages of the present invention more clear, the solutions of the present invention will be further described in detail below with reference to the accompanying drawings.
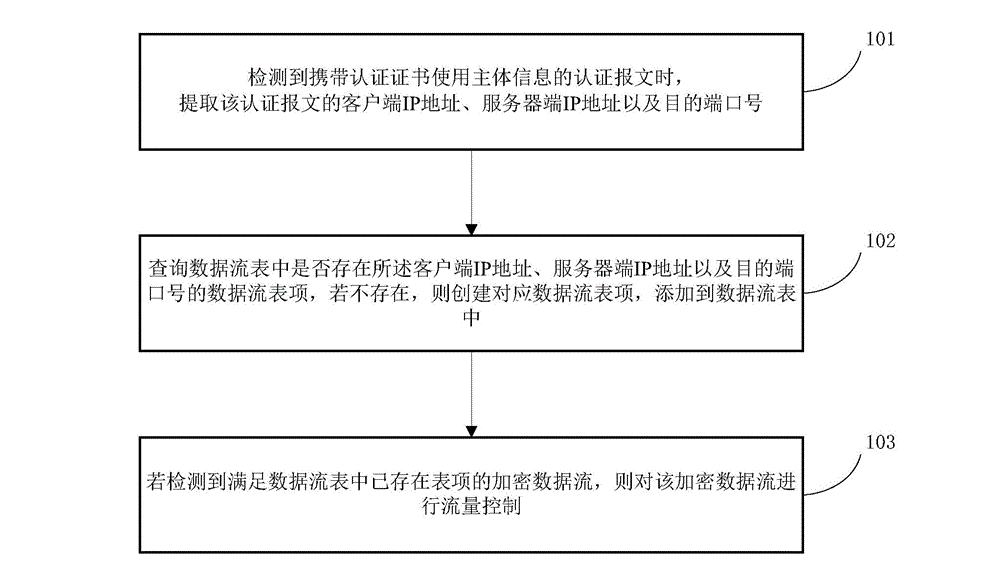
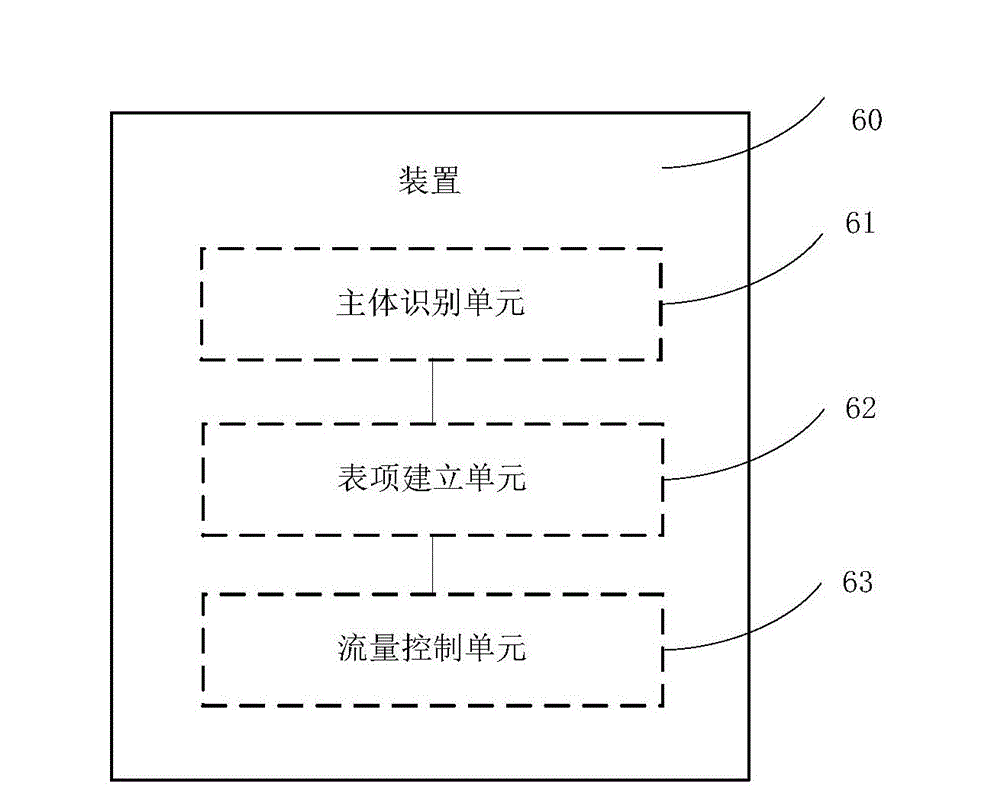
[0019] The invention realizes the purpose of identifying the encrypted data flow by identifying the authentication process of the encryption protocol, thereby realizing the flow control of the encrypted data flow. The present invention takes the TLSv1 protocol as an example, introduces the identification process of the encryption protocol, so as to complete the control of the encrypted data flow of the protocol.
[0020] The TLSv1 protocol includes two protocol groups: the record protocol and the handshake protocol. In the handshake protocol, the certificate authentication part is included. Such as figure 1 As shown, when the TLSv1 protocol is used for single data stream transmission, the information transfer between the client (client) and t...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D Engineer
- R&D Manager
- IP Professional
- Industry Leading Data Capabilities
- Powerful AI technology
- Patent DNA Extraction
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2024 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com