Android application vulnerability detection method and Android application vulnerability detection system
A vulnerability detection and vulnerability technology, applied in the direction of instruments, electrical digital data processing, platform integrity maintenance, etc., can solve the problems of attack, time-consuming and labor-intensive, increase the false positive rate of vulnerability detection, and achieve the effect of avoiding false positives
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
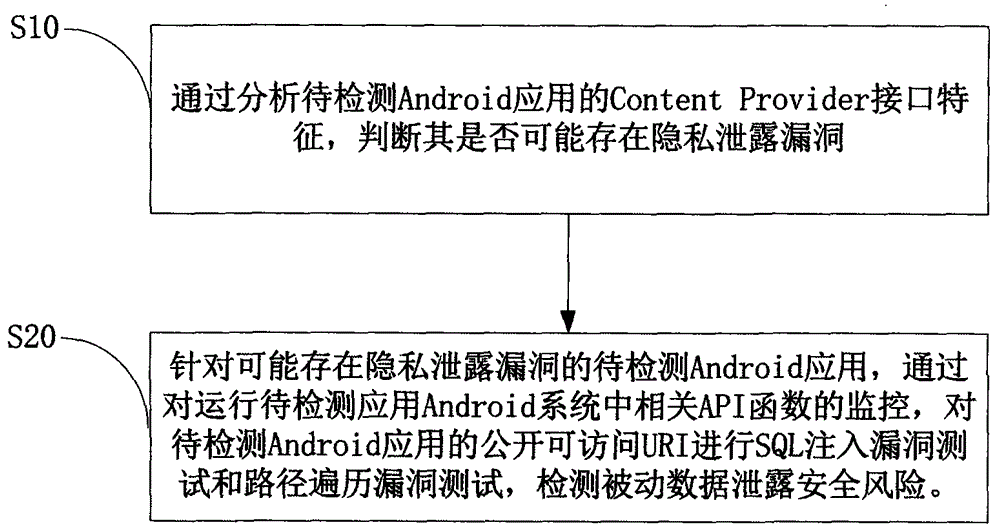
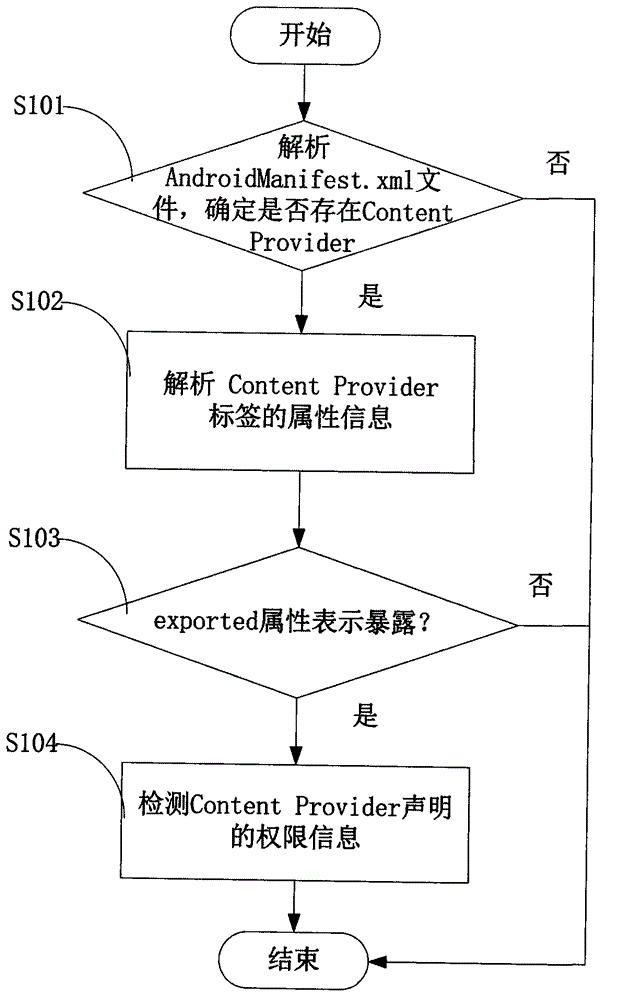
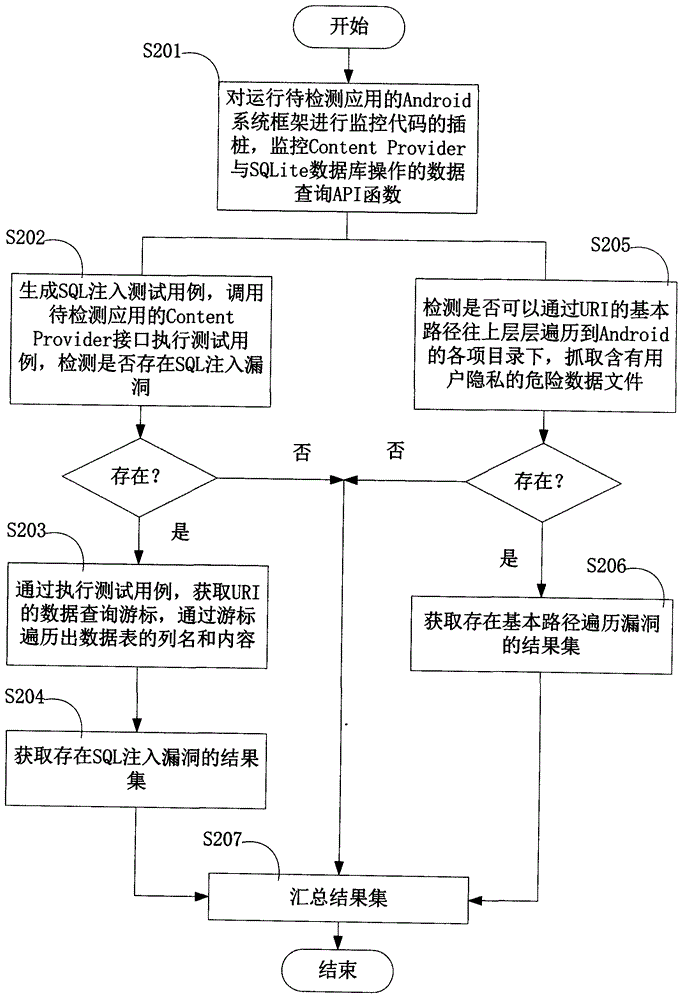
Method used
Image
Examples
Embodiment Construction
[0027] In order to make the object, technical solution and advantages of the present invention clearer, the present invention will be further described in detail below in conjunction with the accompanying drawings. It should be understood that the specific embodiments described here are only used to explain the present invention, not to limit the present invention.
[0028] Definition of Terms:
[0029] English terms / abbreviations
Chinese
Accessible URIs Problem
Public URI Access Vulnerability
Uniform Resource Identifier (URI)
Passive Content Leaks
Passive Content Leakage
Content Pollution
content pollution
Content Leak
content leak
SQL Injection Problem
SQL injection vulnerability
Traversal Problem
path traversal vulnerability
[0030] The inventor found through research that: precisely because of the openness of the Content Provider, it is easy to pas...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com