A Second-Order Side Channel Energy Analysis Method for SM4 Cipher Algorithm
An energy analysis and cryptographic algorithm technology, applied in the direction of encryption device with shift register/memory, etc., can solve the problem of second-order energy analysis without systematic analysis method, etc., and achieve the effect of strong practicability
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
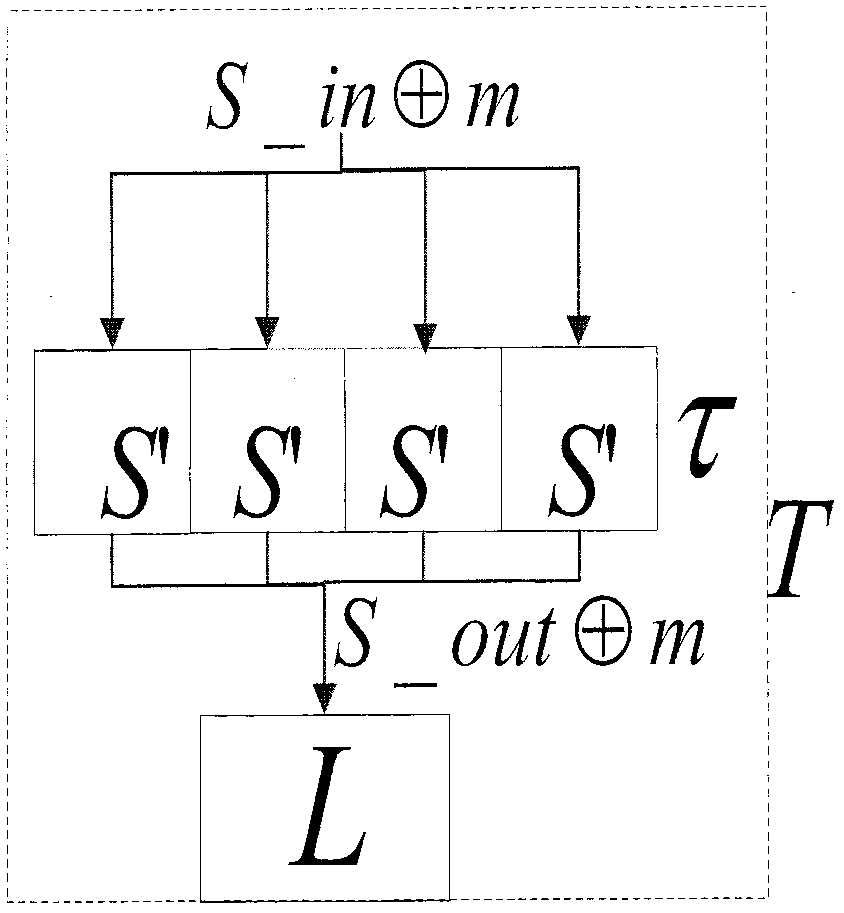
[0056] The technical solution of the present invention is described in detail below. First, the SM4 cryptographic algorithm with the same input and output middle mask value of the S box is used for CPA analysis to illustrate the technical solution of the present invention. A typical implementation of the first-order mask defense method of the SM4 algorithm is as follows: image 3 As shown, both the input value S_in and the output value S_out of the S box are XORed with the mask value m=(m 0 , m 1 , m 2 , m 3 ). The newly constructed S′ box is j is sequentially 0, 1, 2, 3, x j Indicates the j-th byte in 32-bit x. For the first-order mask defense method of the SM4 algorithm, XOR the input and output of the S-box to eliminate the mask:
[0057] Among them, j is 0, 1, 2, 3 in sequence
[0058]
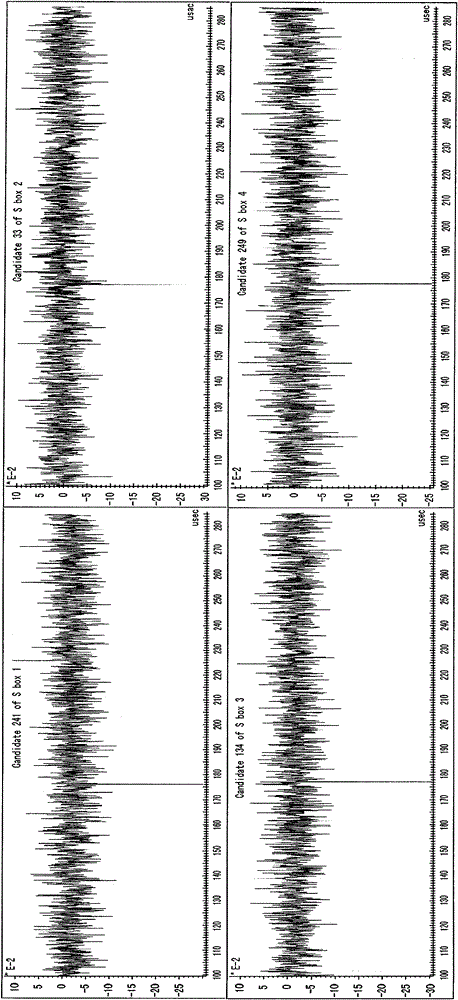
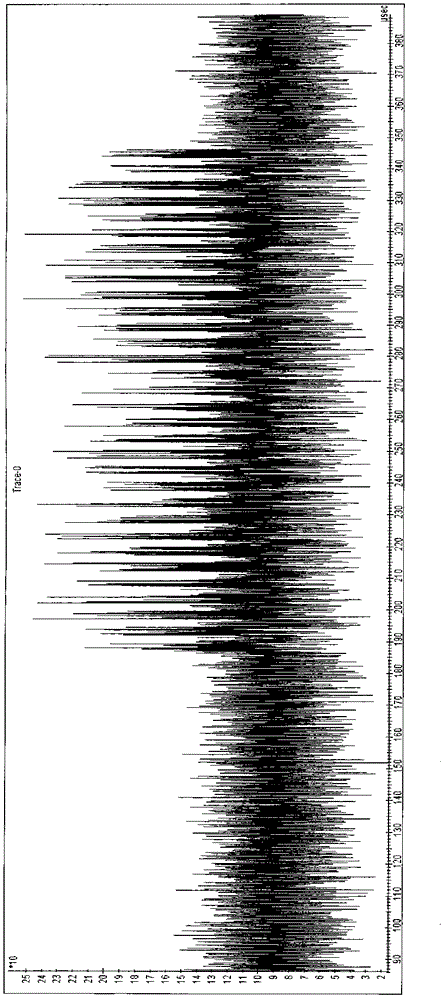
[0059] Therefore, the XOR S_InXorOut of the input and output of the S-box is used as the attack point, and the second-order side channel energy analysis is performed. The s...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com