Vitualization environment data security partition method and system
A virtualization environment and data security technology, applied in the field of data security isolation in a virtualization environment, can solve the problems of virtual machine image data isolation and inability to guarantee user data security, etc.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0025] The present invention will be described below in conjunction with the accompanying drawings.
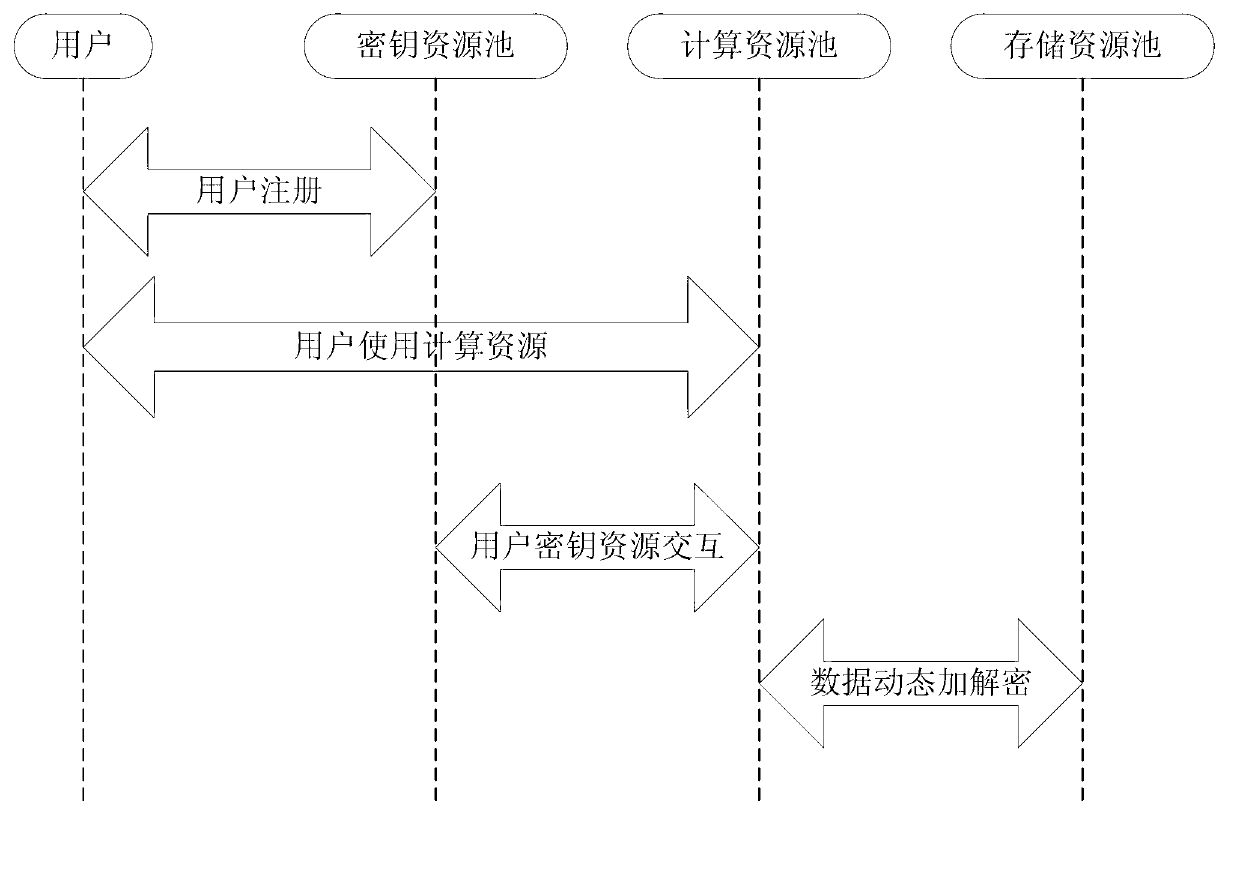
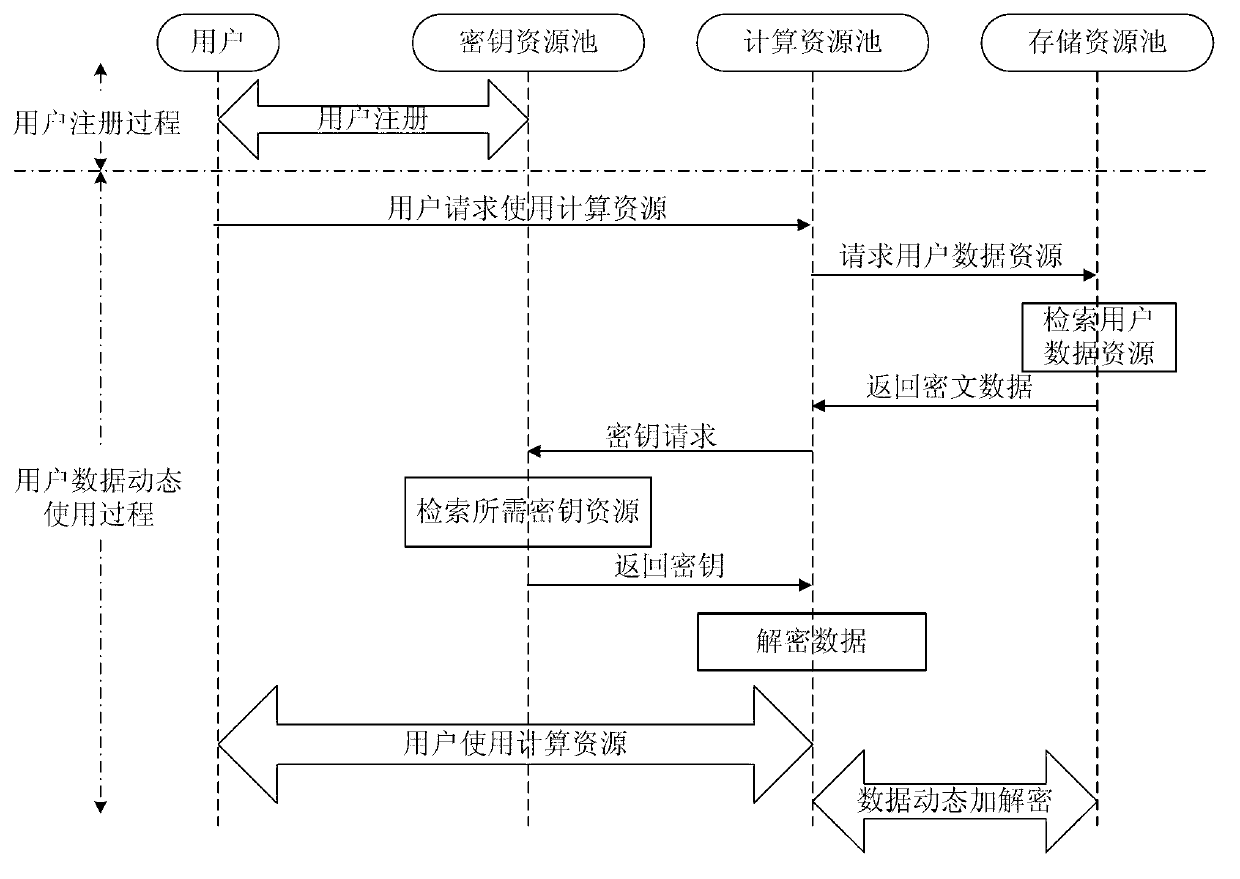
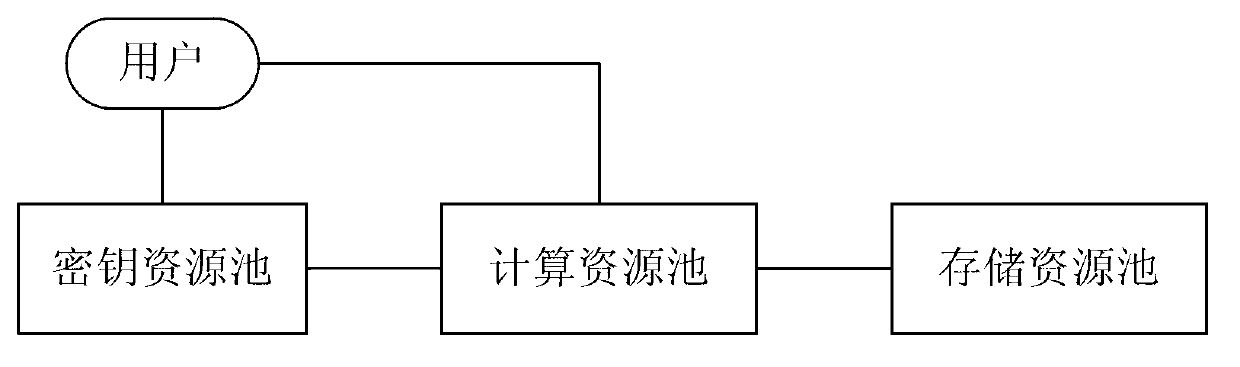
[0026] The present invention relates to a virtualized environment data security isolation method, the principle of which is as follows: figure 1 As shown, the method uses key resource pool 2 to store user information and provide users with key resource generation and management services, and computing resource pool 3 provides computing resources for users and uses data dynamic transparent encryption and decryption technology and key resource pool 2 interaction, the computing resource pool 3 uses the key resource generated by the key resource pool 2 to dynamically decrypt the stored user's virtual machine image data before use, and encrypts the data after the computing resource is operated, and stores it as a storage resource in the storage resource pool4. figure 1 The user 1 shown in is the virtual machine user of the cloud computing platform; the key resource pool 2 is used ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com