Safe access method of cloud storage system
A cloud storage system and secure access technology, applied in the field of computer storage technology and information security, can solve complex key management and distribution problems
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0095] The present invention is further described below in conjunction with embodiment and accompanying drawing.
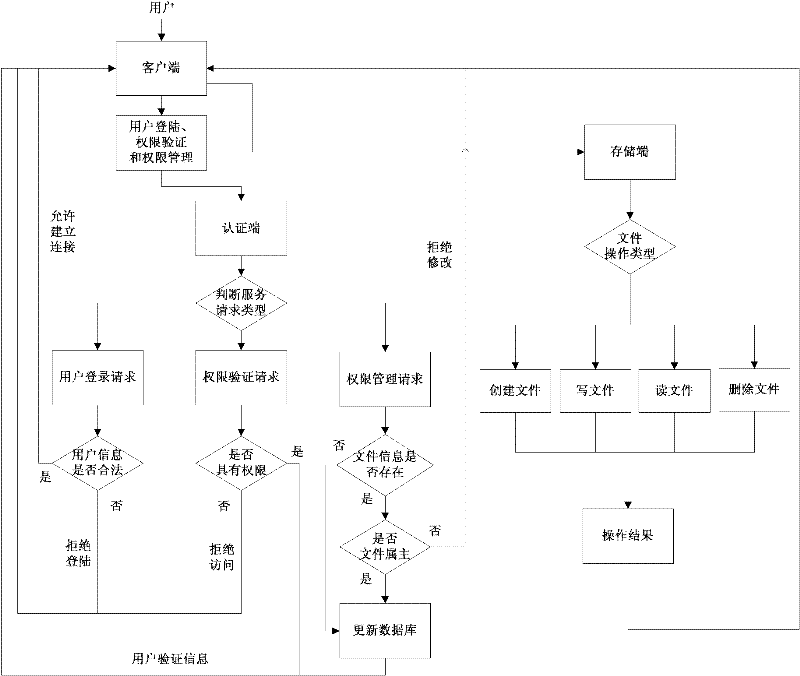
[0096] Such as figure 1 As shown, the embodiment of the present invention includes a client process, an authentication end process, and a storage end process, respectively running on the client host, the authentication end host, and the storage end host of the distributed file system.
[0097] The client generates a unique master key MK and public parameter PK for each user based on the attribute password mechanism; the authenticator loads the user attribute library, file attribute library and attribute key library.
[0098] The specific processing procedures of creating a file request, reading and writing a file request, deleting a file request and rights management request will be further described below in conjunction with the embodiments.
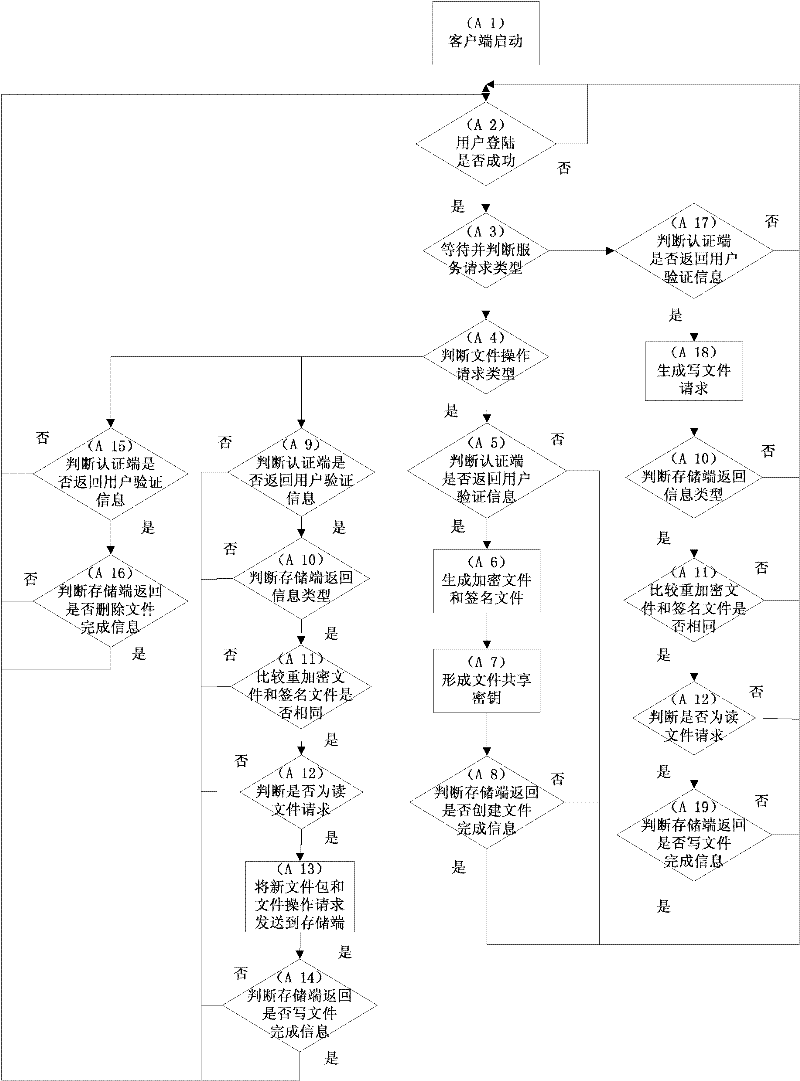
[0099] A. If figure 2 As shown, the client process includes the following steps:
[0100] (A1) The client starts; con...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com