Secret key management method, authorization checking method and device
A technology of key management and authorization code, which is applied in the fields of key management methods, inspection authorization methods and devices, and can solve problems such as RRC connection re-establishment failure and call drop
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0048] In order to make the purpose, technical solutions and advantages of the embodiments of the present invention more clear, the embodiments of the present invention will be further described in detail below in conjunction with the embodiments and the accompanying drawings. Here, the exemplary embodiments and descriptions of the present invention are used to explain the present invention, but not to limit the present invention.
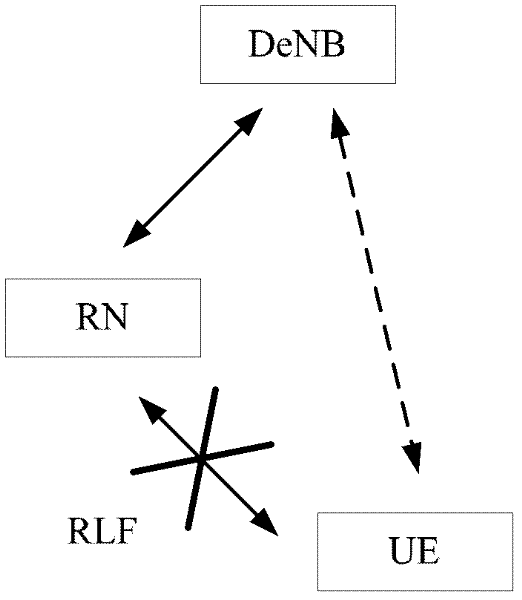
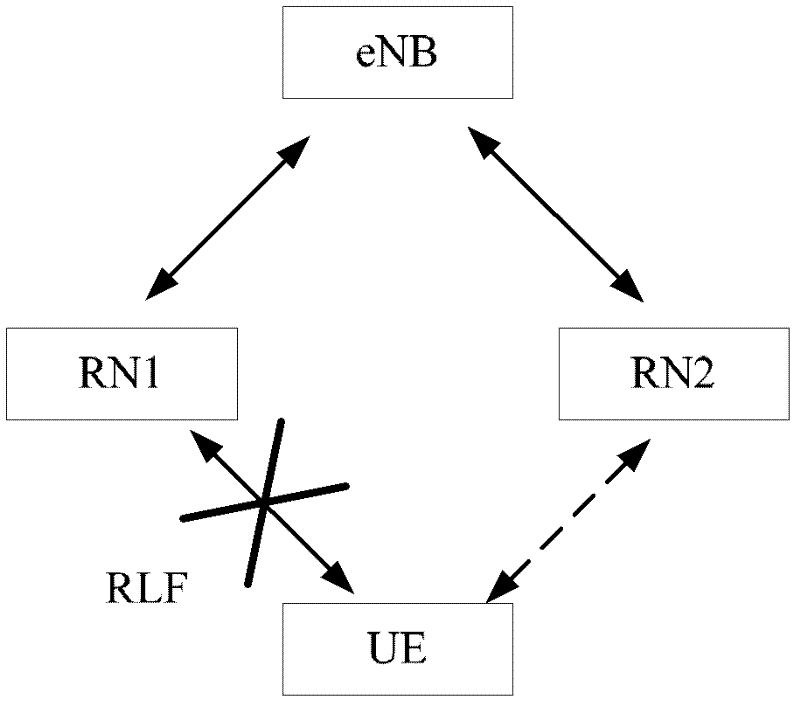
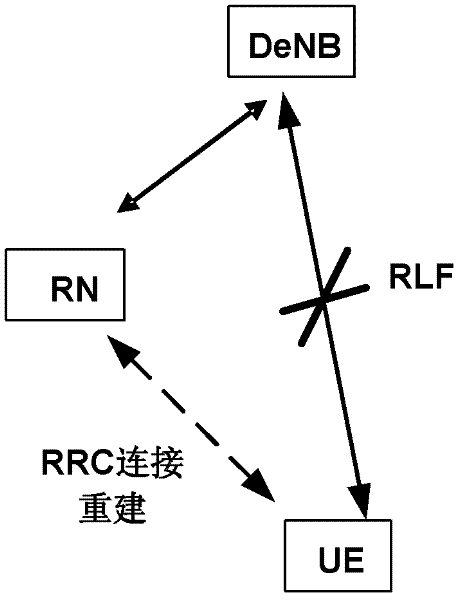
[0049] Figure 1A It is a schematic diagram of selecting a cell under the DeNB for RRC connection reestablishment after the UE under the RN performs cell measurement when RLF occurs to the UE under the RN. Figure 1B It is a schematic diagram for the UE under RN1 to select a cell under RN2 under the same DeNB to perform RRC connection reestablishment after performing cell measurement when RLF occurs to the UE under RN1.
[0050] Please refer to Figure 1A and Figure 1B , during the RRC connection reestablishment process, the RRC Connection Rees...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com