Node identity protection method of mobile wireless sensor network on basis of message time delay condition
A sensor network and mobile wireless technology, applied in wireless communication, network topology, network traffic/resource management, etc., can solve problems such as important messages and key node security hazards
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0054] The present invention will be further described in detail below in conjunction with the accompanying drawings.
[0055] In the present invention, the nodes in the mobile wireless sensor network are divided into three types according to different working states: source nodes, destination nodes and ordinary nodes.
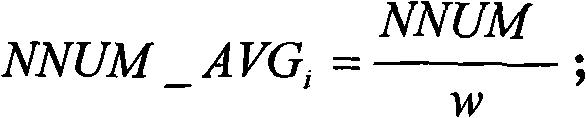
[0056] The source node refers to the message M that is manually input in the mobile wireless sensor network i (M i ={MDATA i , MTIME i}) node, the source node can receive the message M i Carry out segment packaging and transmit to the destination node and / or common node. In the present invention, any source node in the mobile wireless sensor network is denoted as N i .
[0057] The destination node refers to the message M that is manually input in the mobile wireless sensor network i The prior information M_TRA i node, denoted as N t , the destination node N t able to respond to the message M i Make effective use of it. In the present invention, th...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D Engineer
- R&D Manager
- IP Professional
- Industry Leading Data Capabilities
- Powerful AI technology
- Patent DNA Extraction
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2024 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com