Two-stage monthly transaction security check method based on extreme scene
A security check and scene technology, applied in data processing applications, system integration technology, finance, etc., can solve problems such as changes in pre-clearing results, impact of monthly transaction check results, fairness doubts, etc.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0073] Hereinafter, preferred embodiments of the present invention will be described in detail with reference to the accompanying drawings. It should be understood that the preferred embodiments are only for illustrating the present invention, but not for limiting the protection scope of the present invention.
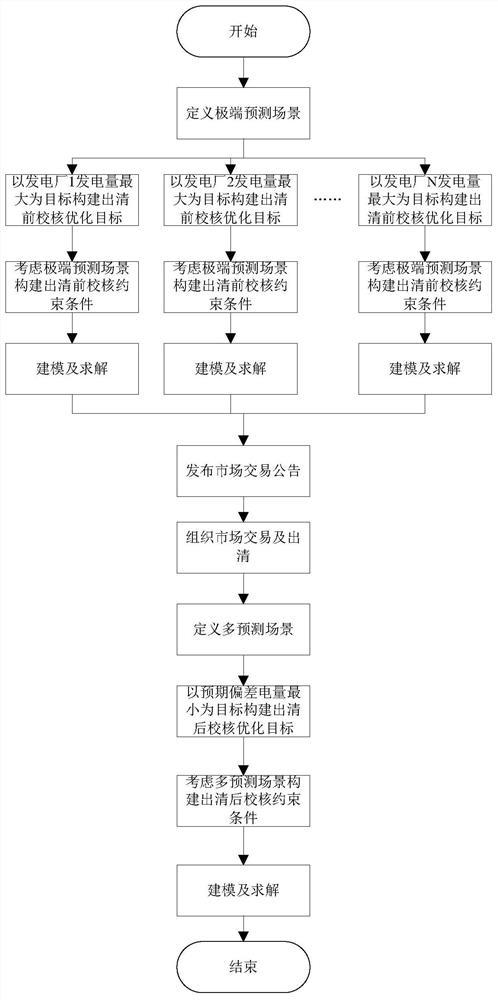
[0074] like figure 1 As shown, a two-stage monthly transaction security verification method based on extreme scenarios of the present invention includes the following steps:
[0075] Step S1: Define the extreme forecast scenario: the extreme forecast scenario in the present invention refers to the combination of scenarios that have the greatest impact on the power plant's transaction volume in the multi-scenario forecast of new energy and load. The impact mechanism of new energy power generation and load power consumption on the power generation capacity of power plants is different. The increase in new energy power generation will occupy a larger market share of powe...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com