Network attack destruction capability quantitative evaluation method and system
A technology of network attack and quantitative evaluation, applied in transmission systems, electrical components, etc.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0089] The preferred embodiments of the present invention will be described in detail below in conjunction with the accompanying drawings, so that the advantages and features of the present invention can be more easily understood by those skilled in the art, so as to define the protection scope of the present invention more clearly.
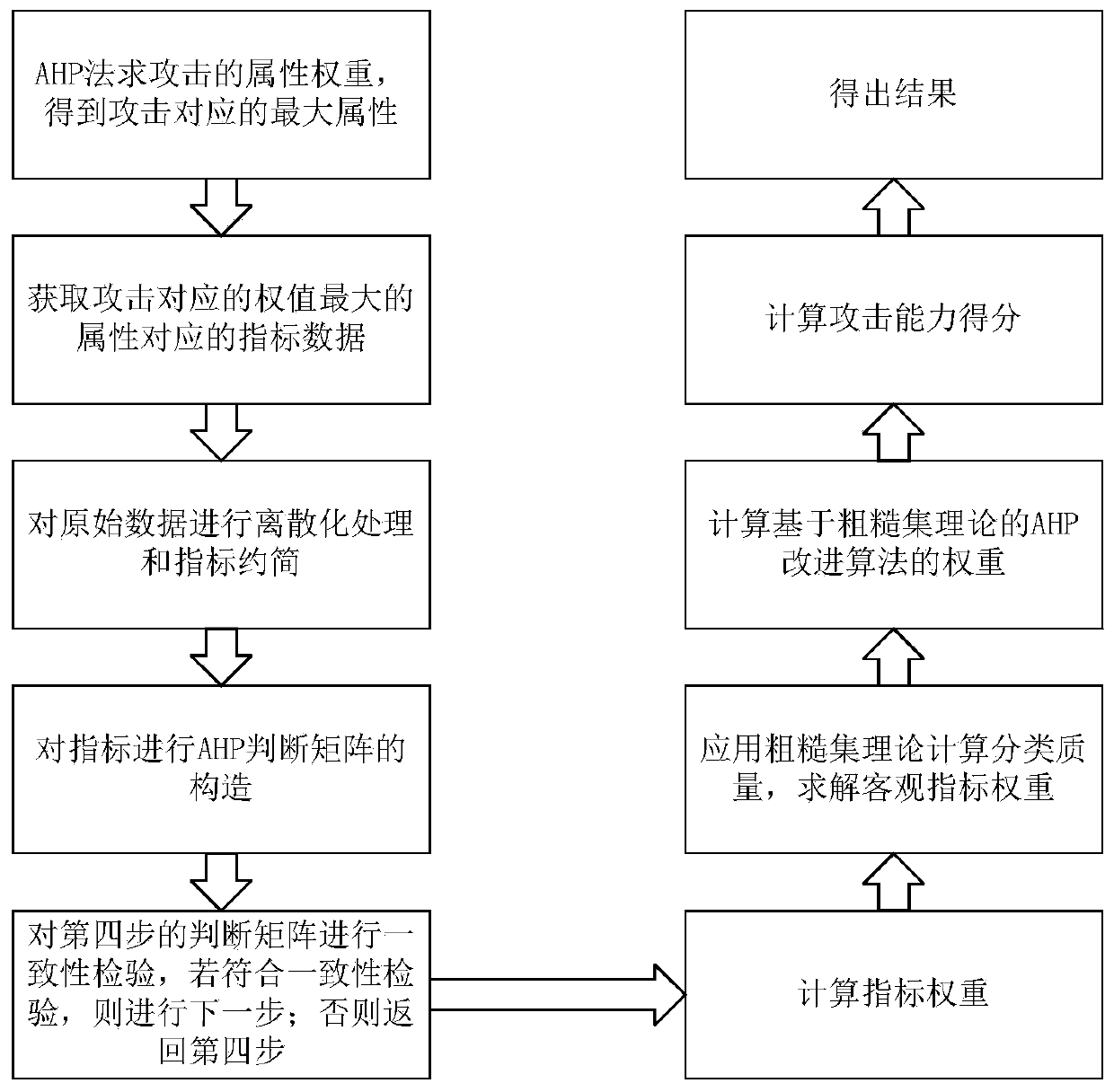
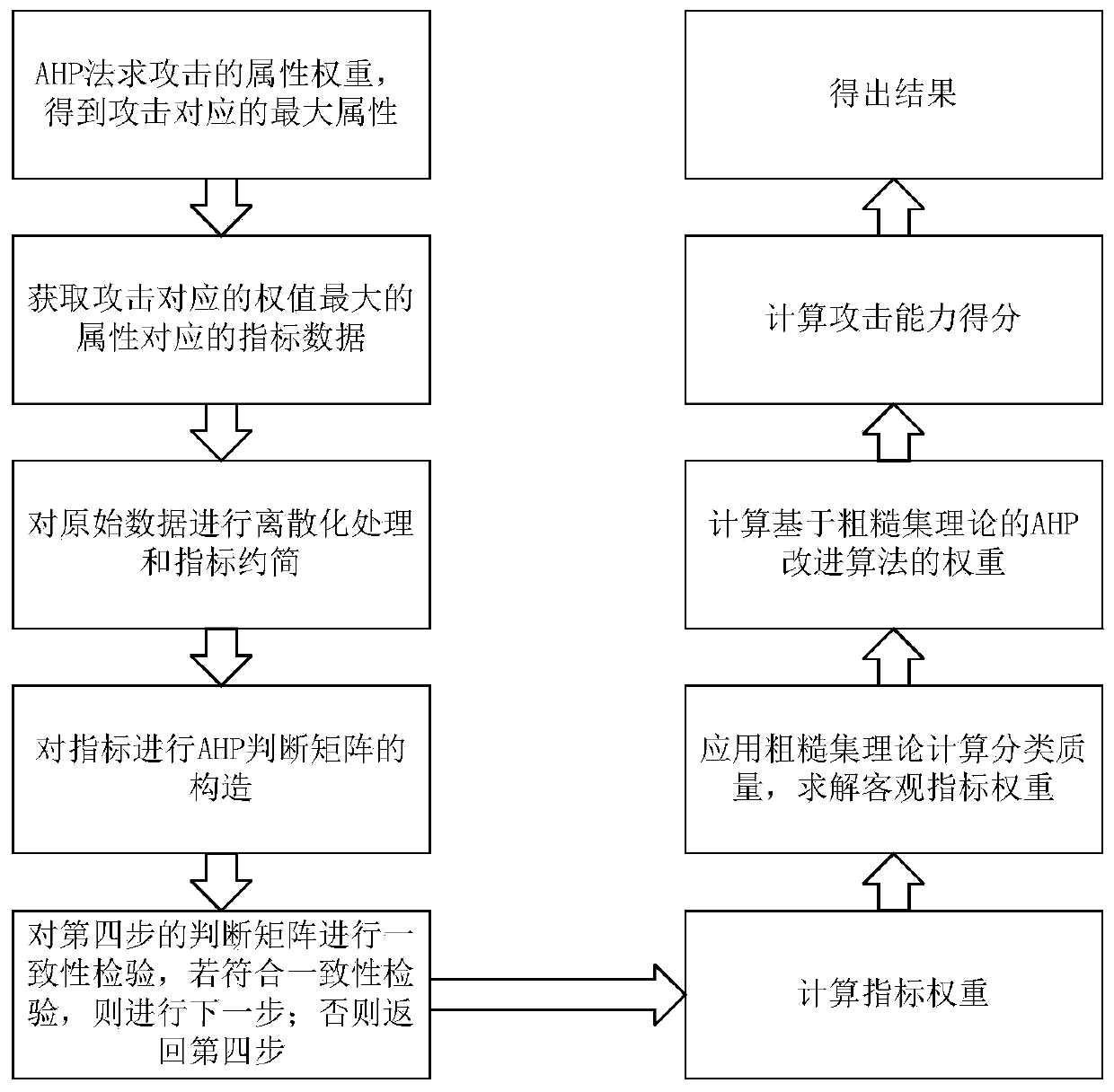
[0090] see figure 2 , the embodiment of the present invention includes:
[0091] A method for quantitatively assessing the destructive capability of common network attacks, comprising the following steps:
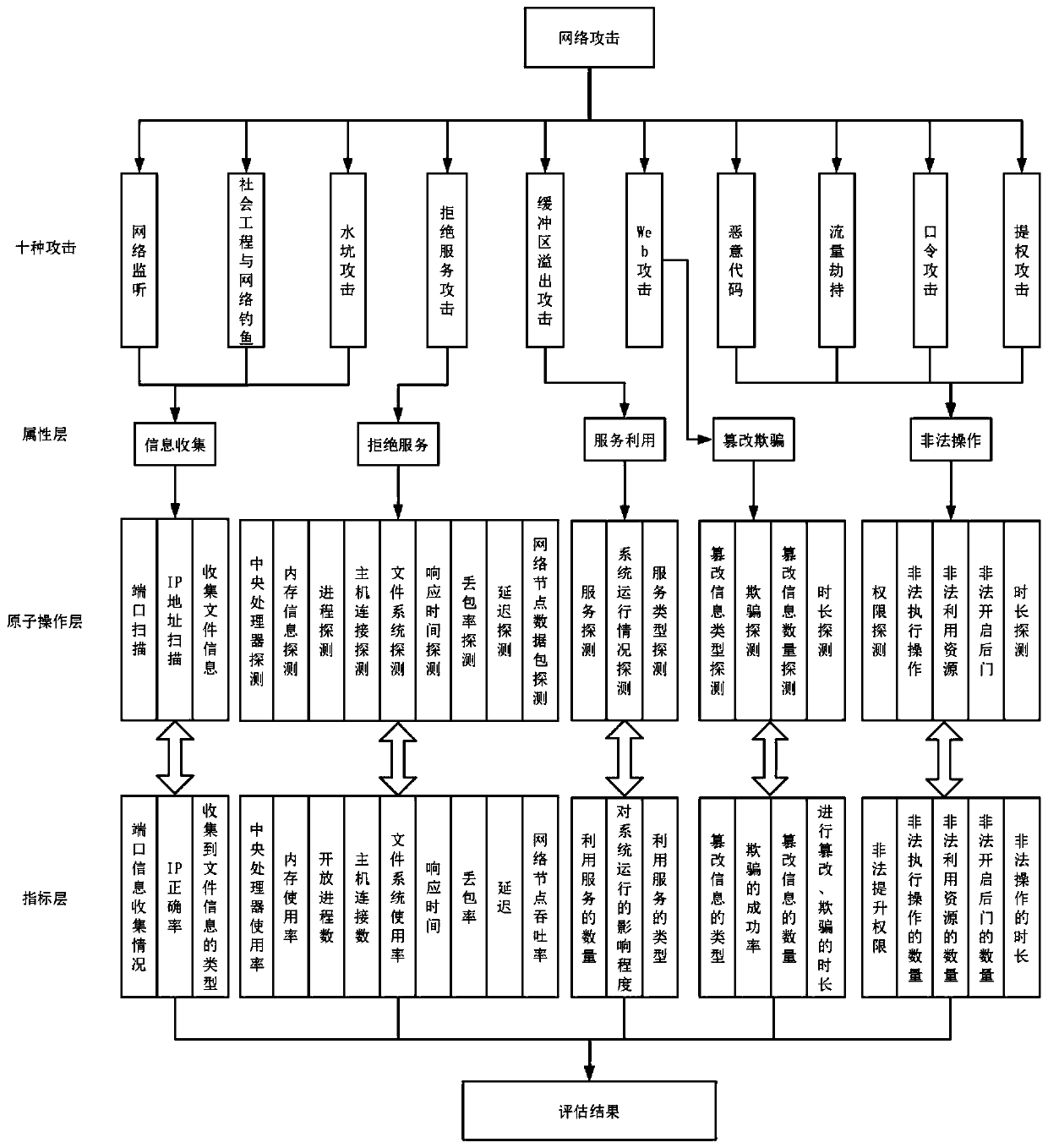
[0092] 1) Use the AHP method to obtain the attribute weight corresponding to the attack. A i is a set of attributes, A i ={a 1 ,a 2 ,...,a i}, i=5, among which five attributes {a 1 ,a 2 ,...,a 5} means {information collection, denial of service, service utilization, tampering and deception, illegal operation}, and the set of five attribute weights is {w 1 ,w 2 ,w 3 ,w 4 ,w 5}. The expert set is P={x 1 ,x 2 ,x 3 ,...,x j}, j...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D Engineer
- R&D Manager
- IP Professional
- Industry Leading Data Capabilities
- Powerful AI technology
- Patent DNA Extraction
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2024 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com