Full path monitoring methods, equipment and device and memory medium
A full-path, target technology, applied in the field of network security, can solve the problem of low efficiency of full-path monitoring, and achieve the effect of fast business process monitoring and display
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0050] It should be understood that the specific embodiments described here are only used to explain the present invention, not to limit the present invention.
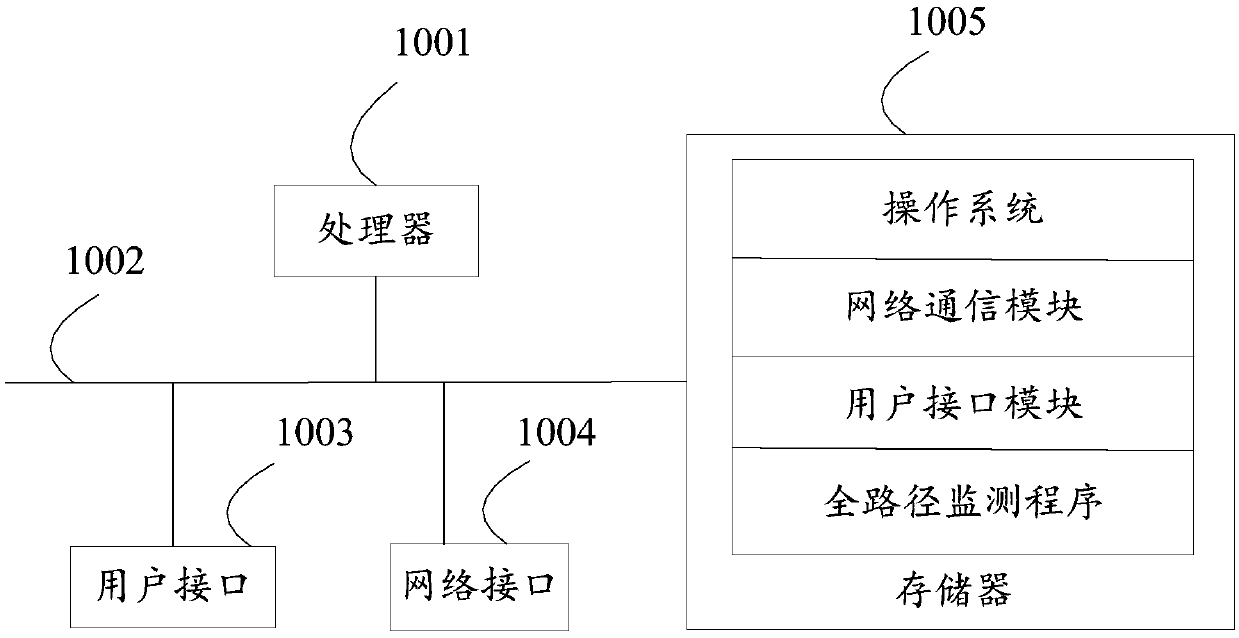
[0051] refer to figure 1 , figure 1 It is a schematic structural diagram of the full-path monitoring device of the hardware operating environment involved in the solution of the embodiment of the present invention.
[0052] Such as figure 1 As shown, the full-path monitoring device may include: a processor 1001 , such as a central processing unit (Central Processing Unit, CPU), a communication bus 1002 , a user interface 1003 , a network interface 1004 , and a memory 1005 . Wherein, the communication bus 1002 is used to realize connection and communication between these components. The user interface 1003 may include a display screen (Display). The optional user interface 1003 may also include a standard wired interface and a wireless interface. The wired interface of the user interface 1003 may be a USB interface ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com